Are DDoS Attacks the 2021 Threat to Watch?
DDoS makes a comeback
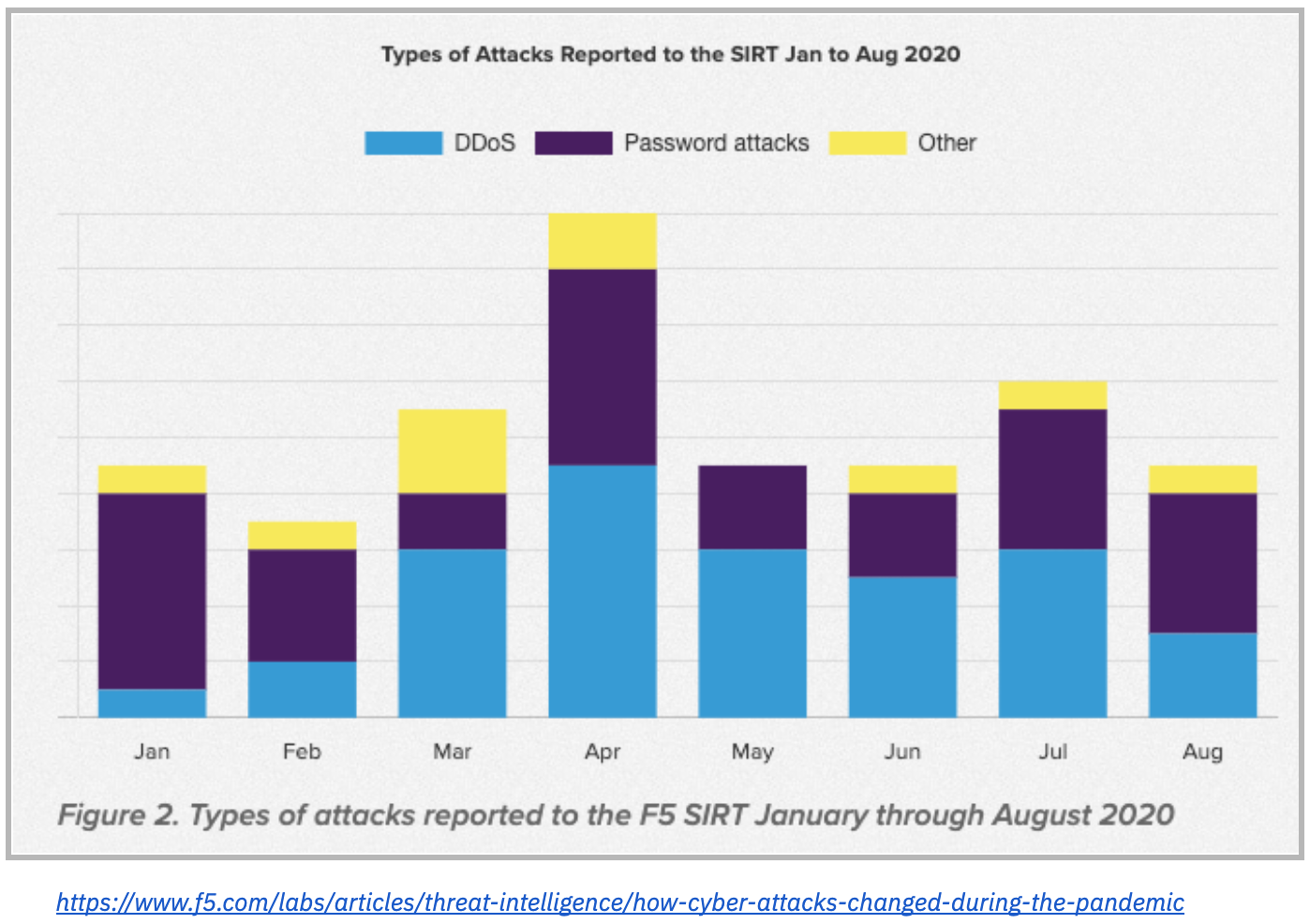
UPDATE: This morning Bleeping Computer reported another player using DDoS to extort money from their victims. In October of last year, they named SunCrypt and RagnarLocker as two cybercriminal enterprises using this scheme. Today, they shared that Avaddon has joined the ranks. CybelAngel analyst, Margaux Gemy’s following blog post shares more information about this type of attack and how to prevent it. Here’s a quick refresher about what constitutes a DDoS attack. A distributed denial of service (DDoS) attack is when there is a malicious plan to disrupt traffic to a server, network, or service. This is accomplished by overwhelming the target or its supporting infrastructure with an overflow of requests. As a consequence, the service, server, or network shuts down and is thus unavailable. Despite the fact that the first recorded DDoS attack was in 1996, many experts are predicting a resurgence in 2021. The reason for these predictions is fairly straightforward. The more organizations on machine-to-machine communication increases and the greater the pain inflicted by a DDoS attack. This coupled with the billions of unsecured IoT devices make it simple for cyber criminals to develop botnets to execute an attack. Some pundits even suggest that DDoS attacks will take its place beside ransomware attacks in 2021. According to Help Net Security, 4.83 mill DDoS attacks took place in the first half of 2020, a 15% increase. DDoS alerts rose with the onset of the Covid-19 pandemic with peaks in late March through April and another in July. 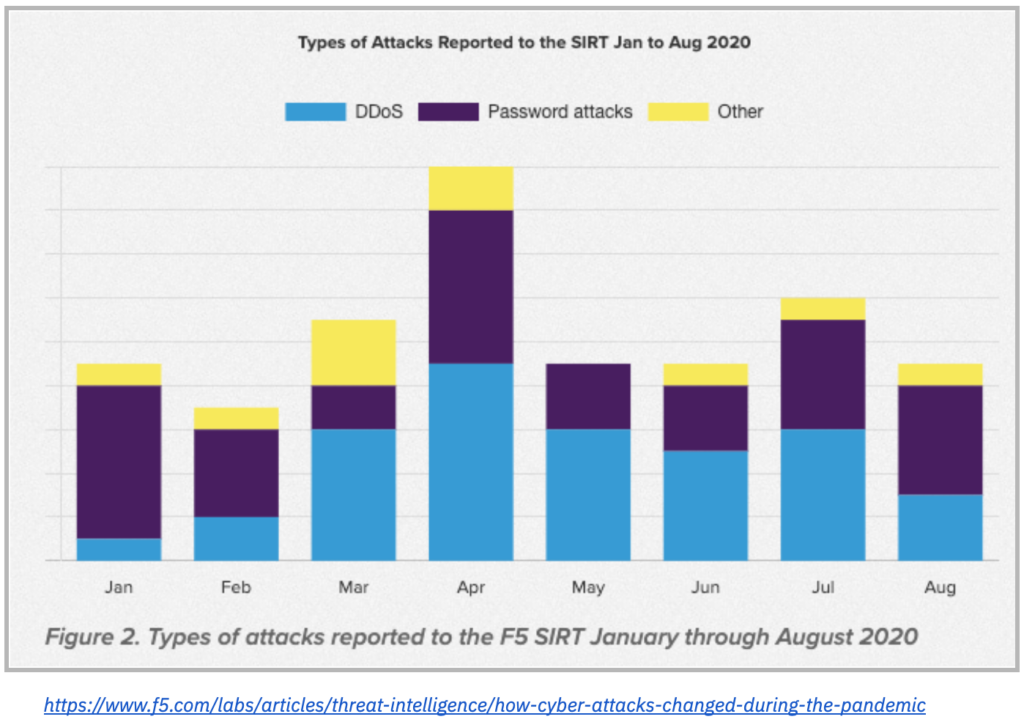
DDoS as a Service
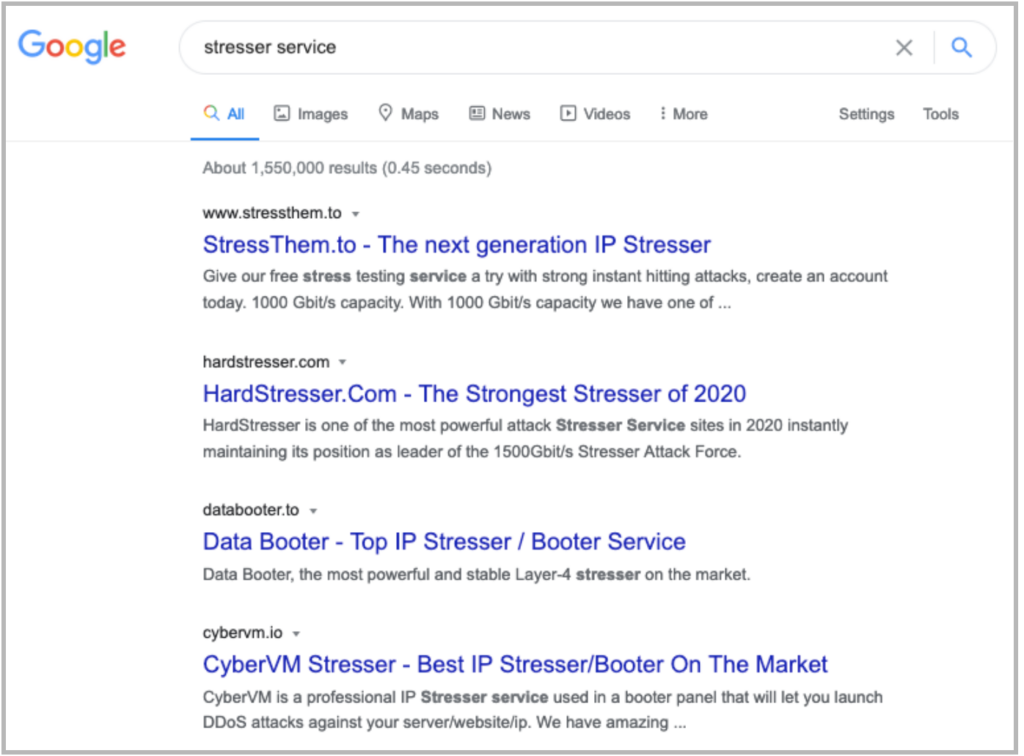
DDoS attacks were once the domain of sophisticated attackers; however with the advent of DDoS as a Service, an assault is within even the novice’s reach. Like ransomware, cyber criminals recognize there is more money to be made by “franchising” DDoS attacks by packaging the tools to make these attacks easier to initiate and to monetize. The “as a service” model now extends to the XaaS (Anything as a Service), including criminal activity. The premise is the same — package technology services in a consumption model for those who either lack the skills or resources and are willing to pay for an on-demand service. There are a variety of sites on the Dark Web who offer DDoS as a service, also called “stresser” or “booter.” However DDoS is no longer limited to the Dark Web, a simple Google search will reveal a number of these services on the Public or Clear Web. The price for DDoS as a Services varies between $25 an hour to $5 for five minutes, and most of these services allow only anonymous payment with cryptocurrency. The price does vary based on the time of the attack or the protection used by the target. With DDoS as a service, it is both accessible and affordable to every hacker regardless of their skills. Below are two screenshots of DDoS offers. One was taken on the Dark Web and the other one on the Clear Web. Interestingly, there are a large number of these DDoS as a service sites are scams. 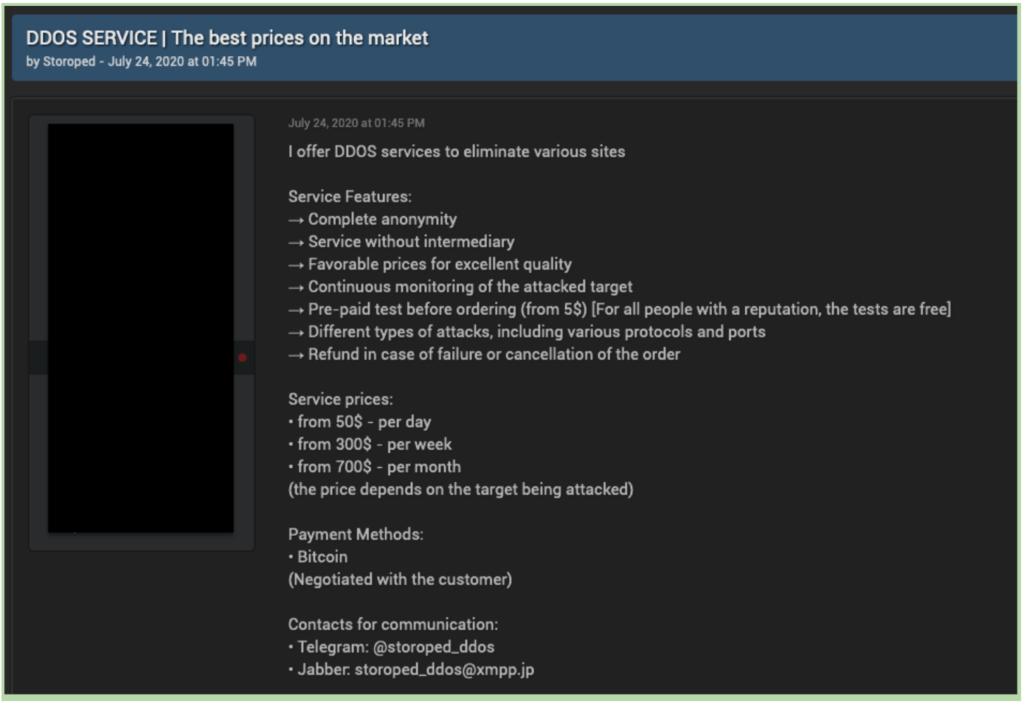
DDoS consequences
Before we look at the consequences of a malicious DDoS attack, organizations should first examine the resistance of your own network against a surge in visits. Organizations need to be as vigilant about testing the vulnerabilities in their infrastructure, as the cyber criminals planning an attack are. Researchers explain the threat as malicious traffic coming from hundreds or even millions of IP addresses; however, detecting the attacking devices is much more difficult. We previously talked about the low cost entry point using DDoS as a service; however, an attack can cost the targeted company as much as $50,000 per hour. Large scale attacks can cripple businesses, shut down their ecommerce sites, disrupt day-to-day operations, and ruin brand reputations. Routine DDoS attacks may be launched against any website to disturb its visitors — damaging the image and reputation of the victim. But just imagine, threatening a famous e-commerce site on a strategic sales day, such as Black Friday — the losses could be staggering. It is easy to see the potential to monetize a potential attack by demanding payment to stop an attack. Last but not least, DDoS attacks have also been used as a decoy, to keep the attention of the IT security team focused on the down services while attackers were conducting malicious activities elsewhere on the network. Whatever the reason, DDoS attacks become more and more easily accessible while more and more sophisticated at the same time.
DDoS protection
It goes without saying that “planning is best done ahead of time.” In this case, having a contingency plan should a DDoS attack occur is critical. This includes identifying your most critical and vulnerable infrastructure points, which must include your Cloud providers. In addition, your IT and Security team needs to secure the entirety of its infrastructure to ensure it cannot be weaponized in a DDoS attack. CybelAngel immediately notifies IT and Security teams when:
- Internet-facing RDPs are providing information to attackers in their reconnaissance phase.
- Misconfigured industrial protocols are leaving your security perimeter making these more vulnerable to hacking.
- Shadow web servers are expanding your attack surface.
To better understand how CybelAngel can assist you in protecting your business from a DDoS attack, talk to one of our experts. Click HERE.