Cyber Roundup — Week of April 20

جدول المحتويات
Here are the main stories you missed last week.
1. France: The HexDex seizure reveals how one threat actor fed multiple headline breaches.
The headline: French authorities seized the online profile of “HexDex,” the pseudonymous actor behind several of France’s most damaging data breaches this year. The BL2C (Brigade de lutte contre la cybercriminalité) replaced the hacker’s social profiles with an official seizure notice, signaling the culmination of a months-long investigation. HexDex had claimed responsibility for breaches affecting the French Ministry of Education (243,000 personnel records), multiple sports federations via the Exalto platform, and other high-profile targets.
What we’re actually watching: When authorities seize a threat actor’s infrastructure, they’re not just stopping one person — they’re disrupting an entire data monetization pipeline. And that’s where most breach coverage gets it wrong.
Three things our team tracks when a major data broker like HexDex goes down:
- Supply chain fragmentation. HexDex operated what he described as a “retail resale chain” — analysis, indexing, sale to intermediaries who resold to their own customers. When the top of that chain gets severed, the fragments don’t disappear. They scatter across smaller forums and marketplaces, often at higher prices and with less quality control. We monitor those secondary markets for our customers’ data appearing in new hands.
- Attribution validity windows. French authorities have made arrests in connection with some of HexDex’s claimed breaches, but as CybelAngel’s analysis notes, the attribution chain isn’t closed. Two individuals were charged in March for the OFII attack, but nothing in official communications confirms they’re behind the HexDex persona or the Ministry of Education breach. Until that chain is complete, treating “HexDex as neutralized” would be premature.
- Reconnaissance data permanence. The most dangerous part of HexDex’s model wasn’t the initial breach — it was what came next. Data exfiltrated by actors like HexDex directly feeds reconnaissance for ransomware crews. An employee credential compromised in a 2024 HexDex data sale becomes the entry point for an Akira ransomware attack in 2026. Those data trails don’t vanish when the original broker is arrested.
The CISO question: If your employees’ or customers’ data passed through HexDex’s “retail chain” — and statistically, given the scale of French breaches this year, it likely did — do you know which downstream buyers now hold it, and are you monitoring for it being used as reconnaissance against your own organization?
2. Germany: The Die Linke ransomware attack tells you which third parties are about to be targeted.
What we’re actually watching: Qilin’s victim selection is a leading indicator, not a lagging one. When a ransomware group lists a political target, they’re advertising — to other affiliates, to access brokers, and to the buyers of stolen data — that the broader sector is in season.
Two patterns we watch in the weeks after a politically-tinged ransomware claim:
- Sector echo. A successful hit on one political party is followed, statistically, by reconnaissance against adjacent organizations: other parties, party-aligned NGOs, campaign vendors, polling firms, donor CRMs. The reconnaissance is often visible — exposed admin panels, misconfigured S3 buckets, default-credential VPNs — before the second attack lands.
- Affiliate handoff. Qilin operates as ransomware-as-a-service, which means the access broker who sold the Die Linke entry point may have sold five others to the same affiliate. Those entry points often surface on initial-access-broker listings within 30–90 days of the public attack.
The CISO question: If you supply, advise, or process data for political organizations in Germany, are you scanning your own external attack surface as if you were the next name on the leak site?
3. UK: The NCSC’s “perfect storm” warning was really a warning about pre-positioning.
The headline: At CyberUK in Glasgow on April 22, NCSC head Richard Horne said the most serious attacks on the UK now come from Russia, Iran, and China. The agency is handling about four “nationally significant” incidents a week. UK Security Minister Dan Jarvis added that the NCSC dealt with more than 200 nationally significant incidents in the past year — more than double the prior year.
What we’re actually watching: The phrase to underline in Horne’s speech wasn’t “perfect storm.” It was his observation that in a real conflict, organizations “won’t be able to pay their way out.” That’s a tell about pre-positioning — the practice of state actors quietly establishing footholds in critical infrastructure now, to be activated later.
Pre-positioning leaves a particular kind of fingerprint. It looks like:
- Long-dwell, low-noise access. Compromised but unused credentials sitting in infostealer logs for months. Webshells on edge devices that haven’t been touched since deployment. VPN appliances with quiet, consistent beaconing to infrastructure that doesn’t match any known commercial service.
- Forgotten infrastructure. The public-facing assets a company forgot it owned: a subsidiary acquired five years ago, a developer’s test environment that ended up on a permanent IP, a marketing microsite with admin credentials in the page source. Our scanners find these every day. State actors find them too.
The CISO question: If your organization were going to be pre-positioned against, where would the foothold already be? Your shadow IT inventory is the answer — and most companies have never built one.
4. UK: The Biobank story is a wake-up call about “anonymized” datasets
The headline: UK ministers confirmed that anonymized health data from approximately 500,000 UK Biobank participants surfaced for sale on an Alibaba-linked Chinese marketplace. The exposed fields reportedly excluded direct identifiers but included demographic, lifestyle, and biological measures.
What we’re actually watching: “Anonymized” is a legal status, not a technical one. In our experience monitoring underground marketplaces, the buyers of health and genomic datasets are not buying them in isolation — they’re buying them to combine with other datasets they already hold. Re-identification is a merge query.
Three things we check when a research dataset surfaces:
- The full provenance chain. A Biobank record passes through a long supply chain: the originating institution, collaborators, grant recipients, cloud processors, third-party analytics vendors, contract researchers. The leak rarely happens at the origin. We look for exposed cloud buckets, misconfigured research portals, and forgotten file-share links across that entire chain.
- Adjacent listings on the same marketplace. A vendor selling one health dataset usually sells more. The “shop window” tells you who else is at risk before they know.
- Re-identification potential. Demographic + lifestyle + biological measures, combined with even one direct-identifier dataset (a payer database, a pharmacy loyalty program, a fitness app leak), produces named records. We model that risk against our customers’ own data exposure.
The CISO question: When you share data with a research partner, processor, or grantee, do you know — at any given moment — whether their external attack surface is more exposed than yours?
5. Middle East: The Iran-linked OT campaign is a story about exposed devices, not zero-days.
The headline: Federal advisories this week remained anchored on the April 7 joint advisory from CISA, FBI, NSA, EPA, DOE, and US Cyber Command on Iranian-affiliated exploitation of internet-facing Rockwell/Allen-Bradley PLCs. More than 3,000 such devices remain exposed online across U.S. water, wastewater, and energy operators. Separately, the Iran-linked persona Handala publicly claimed it had destroyed 6 petabytes and exfiltrated 149 terabytes from Dubai Courts, Dubai Land Department, and Dubai RTA — a claim that, more than two weeks on, remains unverified.
What we’re actually watching: None of the U.S. critical-infrastructure compromises this campaign has produced have required novel exploits. They’ve required exposed devices with default or weak credentials. That’s an attack surface problem, not a vulnerability problem — and it’s one defenders can fix this week.
The two things we check first when a customer asks about Iran-linked OT risk:
- What’s actually exposed. Not “what does the asset inventory say is exposed” — what is actually reachable from the public internet right now, including assets the asset inventory doesn’t know about. Subsidiary networks, contractor-installed gear, devices brought online for a project five years ago and never decommissioned. PLCs, HMIs, FactoryTalk instances, VNC services, and engineering workstations are the recurring offenders.
- What’s already in the credential dumps. Operator and engineer credentials for industrial systems show up in infostealer logs at a rate that surprises most people. We check those dumps against customer-owned domains continuously. If the credential is already out there, no perimeter control is going to save you.
The CISO question: If a Rockwell PLC belonging to your organization were internet-reachable right now, would your team know within 24 hours? Within a week? Ever?
6. US: The BlackCat negotiator case is a procurement story, not a crime story.
The headline: On April 21, a Florida man pleaded guilty in U.S. federal court to conspiring with the BlackCat (ALPHV) ransomware group while working as a ransomware negotiator. He misused client negotiation data — including insurance limits and strategy positions — to help attackers extract larger payments. About $10 million in assets was seized.
What we’re actually watching: This case is going to drive a wave of contractual and procurement changes through the IR industry, and rightly so. But the underlying problem is broader than negotiators: the people you bring into a breach response have access to information more sensitive than the breach itself.
Five things our IR and threat-intelligence team flags when reviewing third-party crisis responders:
- What information they actually need to do their job — and what they’re being given that they don’t.
- Whether their own infrastructure is exposed. A negotiator with a leaky cloud bucket is a worse risk than the original ransomware crew.
- Conflict-of-interest disclosure. Have they negotiated with this affiliate before? Do they take referral fees from anyone in the recovery chain?
- Communications hygiene. Is the channel they’re using to talk to the threat actor isolated from your corporate network and their own?
- Post-engagement data handling. What happens to your insurance policy, your decryption key, and your negotiation transcript after the engagement closes?
The CISO question: Do you have a pre-vetted IR roster — selected before an incident, not during one — and have you stress-tested their own external attack surface the way you would a critical vendor?
The pattern across all six stories
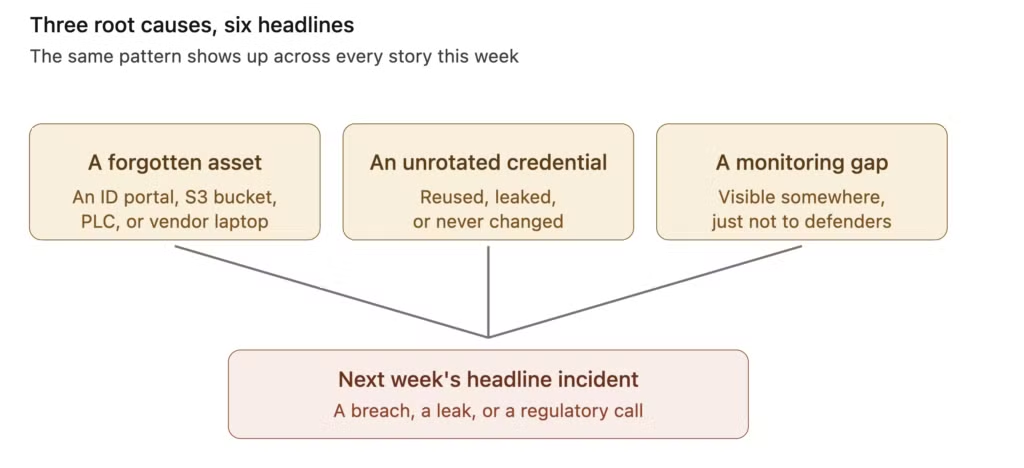
- An asset someone forgot they owned — an ID portal with a known unpatched flaw, a forgotten S3 bucket with research data, an exposed PLC, a third-party negotiator’s laptop.
- A credential that should have been rotated — and wasn’t.
- A monitoring gap — the breach was visible, somewhere, before it became a headline.
That’s the work CybelAngel does: we find those three things on your behalf, continuously, before they become next week’s roundup. If you’d like a complimentary external attack surface assessment to see where you stand against the patterns in this article, we’re happy to arrange one.
Stories covered in this roundup were reported between April 20 and April 26, 2026.

