Akira Ransomware: How the Conti Successor is Targeting the West

جدول المحتويات
Akira is not a new ransomware group. It is the operational continuation of Conti, the Russian-speaking extortion operation that collapsed in May 2022 after a Ukrainian researcher leaked its infrastructure. Blockchain analysis by Arctic Wolf documented three separate transactions in which Akira operators sent ransom payments totaling over $600,000 directly to Conti-affiliated wallets. Arctic Wolf assesses this linkage with high confidence. TRM Labs, in a March 2026 profile, places Akira’s developers in Russia or the broader post-Soviet region. The Akira binary refuses to execute on systems with a Russian keyboard layout — a fingerprint shared with every major CIS-excluded ransomware family of the past decade. Western CISOs defending against Akira are, in operational terms, defending against Conti v2.
Most threat intelligence on Akira focuses on what it does — the four-hour attack chain, the VPN CVEs, the .akira extension. Our full Akira defense guide covers that ground in detail. This article covers something else: who Akira actually is, where it came from, and why that matters for organizations in North America, Europe, and Australia that are absorbing the bulk of its attacks.
Who is behind Akira ransomware?
Akira is a ransomware-as-a-service operation run, at the operator level, by threat actors assessed with high confidence to be affiliated with the dissolved Conti ransomware group. The attribution rests on three independent lines of evidence: blockchain transactions linking Akira wallets to known Conti addresses, behavioral overlap in intrusion workflows and encryption methodology, and language artifacts in the malware itself that indicate Russian-speaking developers.
The US Treasury sanctioned several Conti and TrickBot members in February 2023 and September 2023, formally confirming these operators as Russia-based threat actors. Akira emerged in March 2023 — the same window in which Conti affiliates needed new infrastructure after their original operation collapsed. The timing is not a coincidence. It is the operational handoff.
What happened to Conti, and where did its operators go?
Conti was the most successful ransomware operation of 2021, generating approximately $2.7 billion in cryptocurrency revenue across more than 600 campaigns that year. The group ran a corporate-style operation with HR, payroll, and performance reviews — documents that later became public when the group imploded.
The collapse began on February 25, 2022, one day after Russia invaded Ukraine. Conti publicly pledged allegiance to the Russian government and threatened retaliation against any country conducting cyberattacks against Russia. Within 48 hours, a Ukrainian security researcher using the handle “ContiLeaks” responded by publishing the group’s internal Jabber chat logs, ransomware source code, training materials, and administrative infrastructure. The leaks ran for weeks and exposed the operation from the inside.
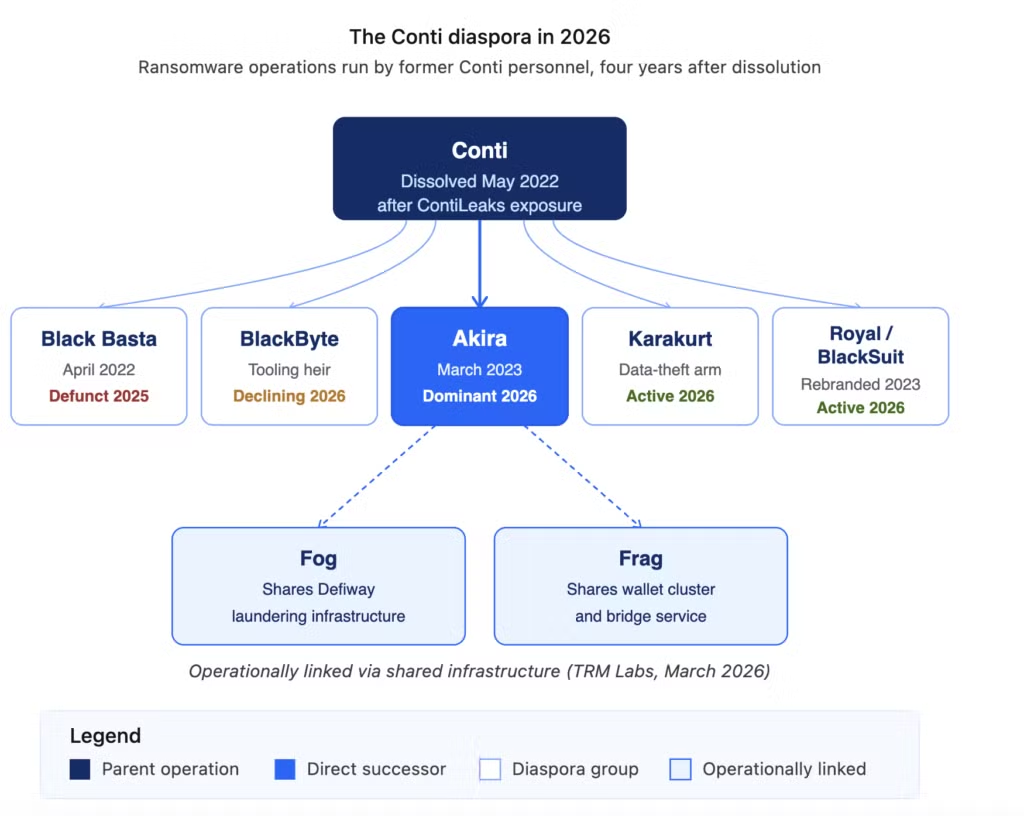
Conti stopped issuing new attacks in May 2022. Its leak site went dark the following month. The operators did not retire — they dispersed. Analysts have tracked Conti-affiliated personnel into multiple successor operations:
- بلاك باستا, emerged April 2022, identified by multiple vendors as a direct Conti successor before its own collapse in 2025
- BlackByte, received portions of Conti’s tooling and affiliate network
- Karakurt, Conti’s own data-theft-only extortion arm, operated continuously
- Royal / BlackSuit — built by senior Conti operators, later rebranded after law enforcement pressure
- أكيرا, the most commercially successful of the post-Conti diaspora
The Conti diaspora is not a single clean split. Analyst1’s February 2026 analysis describes it as a network of operationally linked groups sharing tooling and infrastructure — not competing rivals, but a loose federation of rebranded cells.
How do we know Akira is linked to Conti?
The attribution rests on four categories of evidence, each independently verifiable.
- Blockchain forensics. Arctic Wolf Labs traced three separate Bitcoin transactions in which Akira operators sent the full amount of received ransom payments to wallet addresses previously associated with Conti leadership. The transactions totaled over $600,000. Two of the receiving wallets were tied directly to Conti’s leadership team and had received payments from multiple ransomware families — a pattern consistent with a central laundering function serving the diaspora. TRM Labs confirmed similar on-chain overlap in its March 2026 profile, identifying shared Defiway laundering infrastructure used by Akira, Fog, and Frag — three groups that appear to be operationally coordinated.
- Behavioral signatures. Akira ignores the same file types and directories as Conti. It uses a nearly identical encryption algorithm selection. Negotiation styles match: the opportunistic ransom-setting based on data review, the specific pressure escalation patterns, the language used in victim communications. These are craft habits — the kind of detail that transfers with people, not code.
- Language artifacts. The Akira binary contains a hard-coded check that terminates execution if the infected system is running a Russian keyboard layout. This CIS-excluded targeting pattern — refusing to attack computers in former Soviet states — is the single most consistent fingerprint of Russian-speaking ransomware operations. Akira affiliates communicate in Russian on dark web forums. Barracuda’s research team documented both patterns.
- Source code inheritance. Avast Threat Labs concluded in June 2023 that the Akira encryptor’s creators were “at least inspired by the leaked Conti sources.” Because Conti’s source code was publicly leaked, pure code-overlap attribution is harder than usual — any group could theoretically fork from the leaked code without being tied to the original operators. This is why the blockchain evidence is the strongest single pillar of the attribution.
No single piece of this evidence would prove the connection on its own. Together, they converge.
Why is Akira targeting Western organizations specifically?
The geographic pattern is not random. Akira’s victim distribution tracks Conti’s old priorities almost exactly:
- الولايات المتحدة — approximately half of all Akira attacks
- Western Europe — France showed a striking 53.1% share of detected Akira attacks in one 2024 study period; the UK, Germany, and Italy follow
- Canada, Australia, New Zealand — the rest of the Five Eyes and commonwealth manufacturing base
There are two reasons Western organizations absorb the damage. The first is financial: Western enterprises have cyber insurance, Bitcoin liquidity, and boards willing to authorize large ransom payments to avoid operational disruption. The second is political: targeting Russian or CIS organizations is a red line for Russian-speaking operators both operationally (they live there) and politically (the state tolerates cybercrime that points outward).
France’s disproportionate share deserves its own note. French organizations sit at the intersection of high enterprise density, cyber-insurance penetration that matches US rates, and, per our recent analysis of the HexDex affair, a domestic criminal ecosystem that actively feeds foreign ransomware affiliates with initial-access credentials. A French organization’s data being sold on a forum today becomes an Akira affiliate’s entry point six months later.
What does Akira look like financially compared to Conti?
The FinCEN report on ransomware payments from January 2022 to December 2024 identified Akira as the fourth-most-extractive ransomware variant in the period, with 376 Bank Secrecy Act filings totaling $120.9 million in extortions from April 2023 through December 2024. TRM Labs’ 2026 analysis reports Akira collected $150 million in 2025 alone. Independent research cited by multiple vendors puts Akira’s cumulative total at $244 million or higher as of early 2026.
The operation is not Conti-scale — Conti’s 2021 peak of $2.7 billion remains unmatched. But Akira has achieved something Conti did not: sustained operational continuity across three years without a major law enforcement disruption. That durability, more than the dollar totals, is what Western defenders should be paying attention to.
What is the Conti diaspora, and why does it matter to CISOs?
The Conti diaspora is the informal network of ransomware operations staffed, tooled, or financed by former Conti personnel. It is not a single group. It is not a hierarchy. It is a federation of rebranded operations that share three things: Russian-speaking operators, common laundering infrastructure, and an operational playbook built during the Conti era.
For a Western CISO, this has three practical consequences:
- 1. Defending against Akira is defending against a moving target. If US or EU law enforcement disrupts Akira’s infrastructure tomorrow, the operators do not retire. They rebrand. The Conti pattern of 2022 repeats — and the same TTPs surface under a new leak site within months. The defenses that work against Akira work against the next iteration precisely because the people and the playbook carry across rebrands.
- 2. Threat intelligence must track operators, not brands. A feed that alerts on “Akira IOCs” is useful. A feed that tracks the Conti-affiliated operator cluster across brand changes is far more useful — because it catches the operation before the rebrand is publicly attributed.
- 3: Laundering infrastructure is a weakness. TRM Labs’ identification of shared Defiway infrastructure across Akira, Fog, and Frag is the kind of finding that enables broader disruption than any single-group takedown. When Western governments coordinate sanctions and infrastructure seizures against the laundering layer rather than individual leak sites, the Conti diaspora as a whole takes damage. The February 2023 and September 2023 OFAC sanctions against named Conti members are the template.
How should Western organizations defend against the Conti-Akira lineage?
The defenses are the ones our main Akira guide details — MFA on all VPN endpoints, immutable backups, EDR with behavioral analysis, network segmentation, patched Cisco and SonicWall appliances. What the threat actor profile adds is a mindset.
Treat Akira as a state-tolerated, durable, professionally-staffed criminal enterprise — not as a malware strain. The affiliates operate from jurisdictions that will not extradite them. The infrastructure rebuilds after disruption. The operators carry their skills into new brands. Defense-in-depth calibrated for a one-time adversary will lose. Defense-in-depth calibrated for a decade-long geopolitical problem wins.
Three operational shifts follow from this framing:
- Assume the credentials are already out there. Conti-lineage operators buy initial access from brokers rather than developing it themselves. The credentials your organization lost in a third-party breach in 2024 are the credentials Akira affiliates will use in 2026. Continuous credential intelligence monitoring is not a nice-to-have.
- Reduce the external attack surface the operators are browsing. Akira’s preferred initial access vectors — unpatched Cisco VPNs without MFA, exposed RDP, forgotten SonicWall appliances — are the things external attack surface management finds before operators do. CybelAngel’s external attack surface management is designed for exactly this.
- Plan for rebrand, not resolution. Incident response playbooks that assume “Akira is taken down, problem solved” underestimate the diaspora. Assume that the operators who hit you as Akira today will come back under a different name in twelve months, potentially targeting the same weakness that let them in the first time.
Frequently asked questions
The Akira operation is assessed with high confidence by multiple independent threat intelligence vendors (Arctic Wolf, TRM Labs, Barracuda) to be run by Russian-speaking operators based in Russia or the post-Soviet region. Key evidence includes: Russian-language communication on dark web forums, hard-coded exclusion of systems with Russian keyboard layouts, and blockchain links to Conti-affiliated wallets tied to threat actors formally sanctioned by the US Treasury as Russia-based.
Akira is not Conti continued under a new brand — Conti’s infrastructure is gone, its code is public, and its operation formally ceased in May 2022. Akira is a separate operation, run by some of the same people. Blockchain analysis by Arctic Wolf documents direct financial links between Akira and Conti-affiliated wallets, and behavioral analysis shows extensive TTP overlap. Analysts describe Akira as a “Conti successor” or part of the “Conti diaspora” — terminology that captures the personnel and operational continuity without claiming the two are formally the same entity.
The Conti diaspora is the network of ransomware operations staffed by former Conti personnel after the original group dissolved in May 2022. Documented members include Akira, Black Basta (now defunct), BlackByte, Karakurt, Royal/BlackSuit, and — per TRM Labs’ 2026 analysis — the operationally linked Fog and Frag groups sharing Akira’s laundering infrastructure. The groups are not formally unified but share operators, tooling, and money-laundering infrastructure.
Reported figures vary by source and period. FinCEN documented $120.9 million in extortions from April 2023 through December 2024 based on Bank Secrecy Act filings. TRM Labs reports $150 million collected in 2025 alone. Independent totals cited across threat intelligence sources place cumulative Akira ransom revenue at approximately $244 million or higher as of early 2026. These figures likely underestimate true totals because they reflect only reported or traceable payments.
Two reasons. First, Western organizations have the financial resources — cyber insurance coverage, Bitcoin liquidity, executive authority to authorize large payments — that make ransom extraction commercially viable. Second, Russian-speaking operators avoid targets in Russia or CIS countries both operationally (they live there) and because Russian law enforcement tolerates cybercrime directed outward but prosecutes domestic targeting. The United States absorbs roughly half of Akira attacks; France, the UK, Germany, Italy, Canada, and Australia make up most of the remainder.
Sanctions alone have not historically stopped Russian-speaking ransomware operators. The February 2023 and September 2023 OFAC sanctions against Conti and TrickBot members formally identified them as Russia-based but did not halt the diaspora’s activity — the same operators continued under Akira, Black Basta, and related brands. Sanctions are most effective when combined with infrastructure seizures, laundering-layer disruptions, and coordinated international law enforcement actions. The recent pattern of disruptions against LockBit (2024) and BreachForums (2025) shows the model working, but the operators rebrand rather than retire.
Protect your organization against the Conti-Akira operator lineage. CybelAngel’s External Threat Intelligence platform tracks ransomware operators across brand changes — monitoring dark web forums, credential marketplaces, and exposed attack surface to identify the weaknesses that Conti-lineage affiliates exploit before they trigger encryption.

