Cyber Threat Intelligence: Ein vollständiger Leitfaden für Sicherheitsteams

Inhaltsübersicht
The cyber threat intelligence market reached $10 billion in 2026und die SANS 2025 CTI Survey, the most comprehensive annual practitioner survey in the field, found that 84% of CTI teams now cite threat hunting as their primary use case, 72% are already integrating AI into their programmesund 68% are producing threat landscape reports that feed directly into board-level strategy. According to the World Economic Forum’s Global Cybersecurity Outlook 2026, presented at FIRST CTI Munich this April, 87% of security leaders now identify AI-related vulnerabilities as the fastest-growing cyber risk they face.
More data, more investment, and still a significant gap between what intelligence programmes collect and what security teams actually act on. A Feedly survey of 14 senior CTI practitioners published in January 2026 found that teams are misallocating attention toward AI hype while foundational capabilities in supply chain visibility and infrastructure monitoring remain underresourced. Closing that gap is what a well-built CTI programme does.
In this article, we‘ll dive into how you can harness cybersecurity threat intelligence to build methodologies that stop attackers before they cause irreparable damage.
What is cyber threat intelligence?
Cyberthreat intelligence is the process of collecting raw data and analysing it to enhance an organization‘s security posture. From the data collected, security professionals can create intelligence reports designed to overcome current and future threats within the threat landscape.
Understanding the Tactics, Techniques, and Procedures (TTPs) used by threat actors is an essential part of threat hunting—improving attribution and thwarting potential attacks.
What are the different types of threat intelligence?
Security teams use different types of threat intelligence to accomplish various goals throughout the organization.
Intelligente Bedrohung can help smaller companies to build comprehensive in-house security operations, often targeted by threat actors due to the perceived lack of security.
For larger organizations, threat intelligence can reduce costs and support large teams to gather information and implement effective security tools.
The three main types of threat intelligence include:
- Tactical threat intelligence: Focuses on predicting future attacks and threat detection. Tactical threat intelligence includes searching for indicators of compromise (IOCs) such as IP addresses used in phishing attacks and file hashes of malware attacks. Threat hunting also relies on tactical intelligence to pinpoint APT attacks and other hidden vulnerabilities.
- Operational threat intelligence: Aims to understand the behaviour of threat actors by looking at TTPs, various attack vectors, and the vulnerabilities they exploit. Operational threat intelligence involves real-time monitoring of networks and systems, utilizing actionable intelligence to develop security controls and mitigation strategies.
- Strategic threat intelligence: A high-level overview of intelligence that positions the organization within the threat landscape. Strategic threat intelligence provides C-level decision-makers with a better understanding of the cyber threats facing the organization.
Why is threat intelligence important?
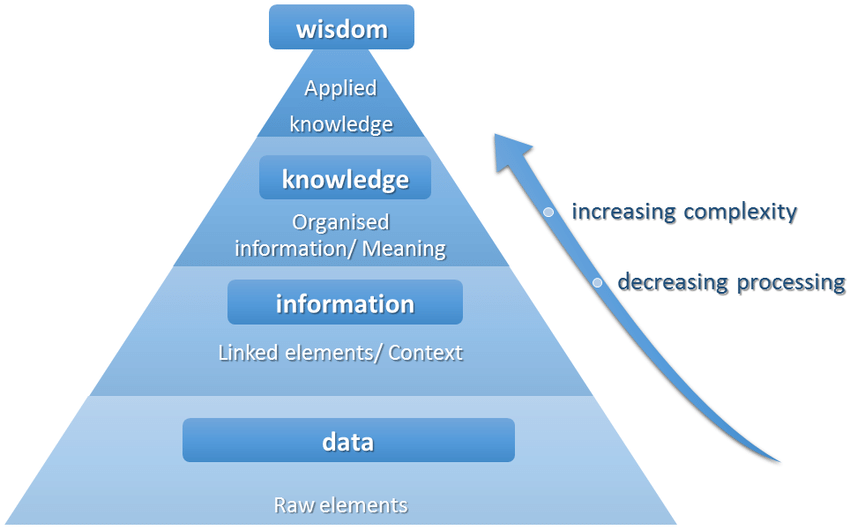
Threat intelligence helps organizations turn raw data into actionable insights. Processed data is used to create in-depth intelligence reports that improve security operations and mitigate risk.
Starting with data, security professionals work to understand threats within the IT environment. With that context, high-level insights can be ascertained, helping C-level professionals make informed decisions.
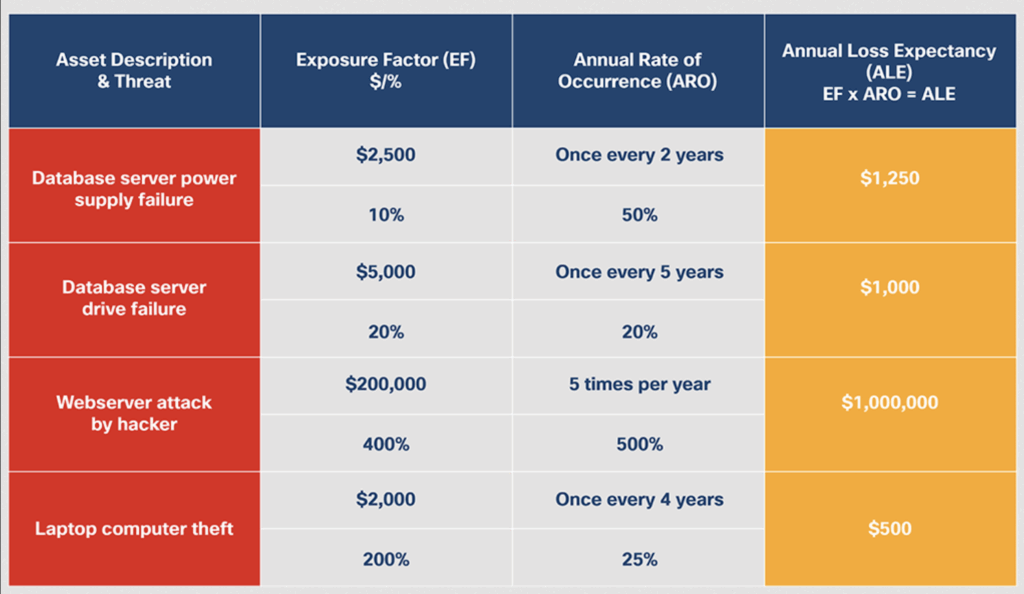
The cost of not having a CTI program can quickly rise, eating into profit margins. A new server can cost up to $20,000, not to mention the time drain on security professionals.
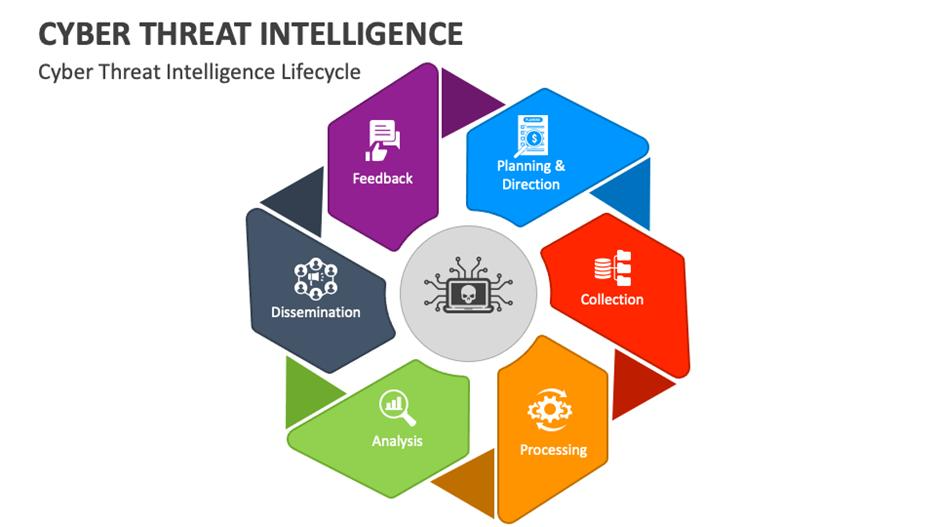
The threat intelligence lifecycle
The threat intelligence lifecycle is a process used in cybersecurity to manage threats. It helps organizations to manage specific threats within the attack surface.
During the threat intelligence cycle, cybersecurity professionals work together with relevant stakeholders to mitigate emerging threats by developing a cross-functional plan tied to measurable business objectives.
By concentrating on pertinent threats, the lifecycle reduces the impact of cyber attacks and creates a methodology for effective responses and improved cybersecurity posture.
1. Planning
Cybersecurity professionals first must set the foundation by planning the direction for the entire threat intelligence process.
It‘s important to consider:
- Stakeholders: Identify organizational decision-making stakeholders who will be effective in implementing intelligence efforts. Security teams will collaborate with stakeholders to define the threat intelligence program’s objectives and goals.
- Define assets, objectives, and scope: Determine which assets and data need protection to define the scope of intelligence efforts. From there, resources and budget can be allocated, along with Key Performance Indicators (KPIs) to define the project‘s success.
- Set priorities: Understanding the immediate threats that may impact your organization‘s IT ecosystem can help better direct the threat intelligence process. Prioritize based on previous cyberattacks and emerging threats.
2. Collection
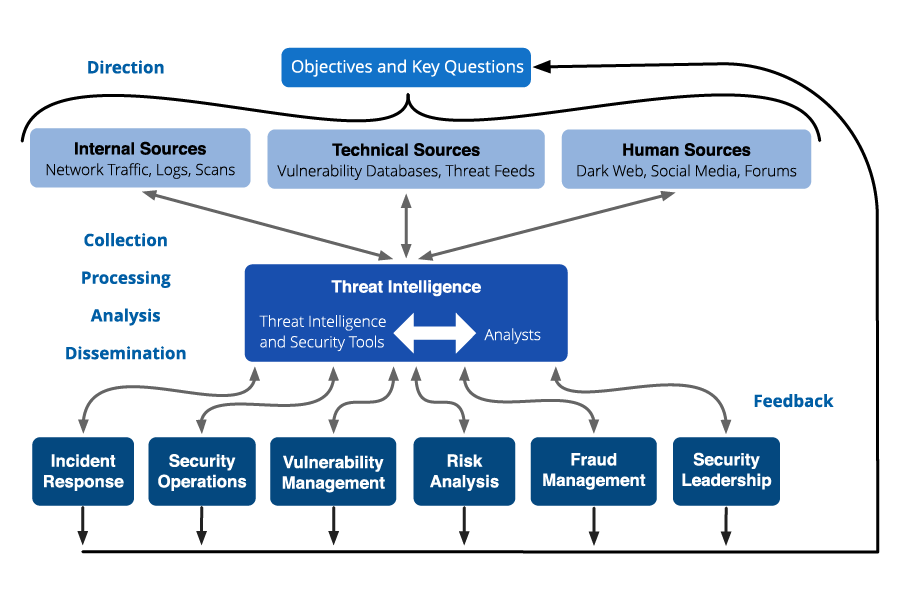
During the collection phase, organizations gather threat data from various sources identified during the planning phase. The collected data includes raw data that will need to be processed to address the intelligence requirements.
Threat intelligence collection should cover all available sources, including internal sources (logs, scans, and network activity), technical sources (threat feeds and databases), and human sources (social media, dark web, and internet forums).
| Source Type | Examples | Use Case |
|---|---|---|
| Internal Logs | Firewall, IDS/IPS, endpoint telemetry | Detect anomalies and internal threats |
| Open Source (OSINT) | News, blogs, social media, forums | Track emerging threats and public chatter |
| Commercial Feeds | Threat intelligence platforms (e.g., Recorded Future, Mandiant) | Enriched, curated threat data |
| Dark Web | Marketplaces, forums, breach dumps | Monitor criminal activity and data leaks |
| Human Intelligence (HUMINT) | Industry sharing groups, analyst networks | Contextual insights and early warnings |
| Technical Sources | Honeypots, malware sandboxes, scanners | Capture TTPs and IOCs |
3. Processing
The raw data collected in the previous phase can now be transformed into an accessible format for analysis. Data should be sorted, decrypted, and translated into a usable form.
When processing raw data, it‘s important to ensure all data is clean, removing any duplicate data entries or corrupted data that may have occurred during the data collection process.
Next, data should be converted into usable formats depending on the stakeholder group. For automation analysis, formats such as STIX, TAXII, JSON, and YAML can be used, while CSV formats are ideal for bulk imports and exports.
4. Analysis
The analysis stage aims to transform raw data into meaningful, actionable insights to make informed decisions and guide the organization‘s security posture.
Thorough analysis can identify vulnerabilities within the IT ecosystem, identify patterns and anomalies, and indicate where a potential data breach could take place.
Cybersecurity professionals should question:
- Are there correlations between different indicators of compromise (IOCs), events, or threat behaviors?
- Can the anomalies be attributed to a known threat actor group?
- How do the threats relate to the broader threat landscape?
- What is the risk of the emerging threats?
- How can professionals use the data to inform strategies to thwart adversary goals?
5. Dissemination
After analysing all relevant data, stakeholders can now be informed of the findings to steer the decision-making process.
Weekly or monthly threat reporting for relevant stakeholders and real-time feeds turns intelligence into actionable insights. Threat intelligence can then be used by high-level executives to inform strategic planning and allocate budget for security activities.
| Stakeholder Group | Intelligence Focus | Format & Delivery Method |
|---|---|---|
| C-Suite & Executives | Strategic risks, business impact, regulatory exposure | Executive briefings, slide decks, dashboards |
| Board of Directors | Governance, risk posture, compliance | Summary reports, presentations |
| Security Leadership (CISO, SecOps) | Threat trends, strategic planning, resource allocation | Threat landscape reports, dashboards, internal briefings |
| SOC Analysts | Real-time threat data, IOCs, alerts | IOC feeds (STIX/TAXII), SIEM alerts, chat notifications |
| Incident Response Team | TTPs, forensic data, containment actions | Tactical reports, playbooks, ticketing system updates |
| Threat Hunters | Hypotheses, detection logic, adversary emulation | Hunt packages, Sigma rules, internal wiki |
| Vulnerability Management | CVEs, patch prioritization, exploitability | Patch bulletins, RSS feeds, ticketing system tasks |
| Risk & Compliance | Regulatory threats, audit findings | Risk summaries, compliance dashboards |
| IT & DevSecOps | Supply chain risks, code vulnerabilities | API alerts, GitHub issues, CI/CD pipeline integrations |
| General Staff | Awareness, phishing, hygiene practices | Newsletters, training modules, simulated phishing campaigns |
6. Feedback
This stage is often overlooked; however, it is crucial to develop effective incident response protocols and improved risk management.
Die SANS 2025 CTI Survey found that 84% of security teams cite threat hunting as their primary CTI use caseund 72% are already integrating AI into their CTI programmes. But a Feedly roundup of 14 senior CTI practitioners published in January 2026 found that teams are systematically misallocating attention toward AI narratives while foundational capabilities in supply chain visibility and infrastructure monitoring stay underresourced. The intelligence exists. The decision to act on it does not.
The gap is not a data problem. It is a distribution problem. Intelligence that does not reach the right person at the right moment in a format they can act on is not intelligence, as it is documentation. Before adding another feed or another framework, ask one question: of the threat intelligence your team produced last quarter, how much of it directly changed a security decision? If the answer is uncomfortable, the issue is not what you are collecting. It is how you are using it.
But what seperates effective CTI?
- Anchoring collection to specific, named intelligence requirements rather than general threat awareness. Validating everything like treating feed data as a starting point, not a conclusion
- Depending on routing intelligence directly into the workflows where decisions are made (not into a separate reporting system) that stakeholders have to go looking for.
- Requiring feedback loops
- Treating automation as a force multiplier on analyst judgment, not a replacement for it.
Cyber threats continue to evolve at machine speed. Ransomware attacks increased 42% in the past year, with a 125% increase in active threat groups, according to CybelAngel’s own 2025 External Threat Intelligence Report. Time to exploit collapsed to just five days, down from 63 days in 2018. And according to the World Economic Forum’s Global Cybersecurity Outlook 2026, presented at FIRST CTI Munich this April, 87% of security leaders now identify AI-related vulnerabilities as the fastest-growing cyber risk they face. A CTI programme running on quarterly reviews and annual threat assessments is not a defence — it is a paper trail.
CybelAngel’s Cyber Threat Intelligence platform combines continuous monitoring across deep, dark and open web sources with analyst-validated IOC feeds and on-demand REACT team investigations, giving security teams the context and the speed to act before threats reach internal systems.

