Hackers Defend Their Reputation Across the Criminal Community
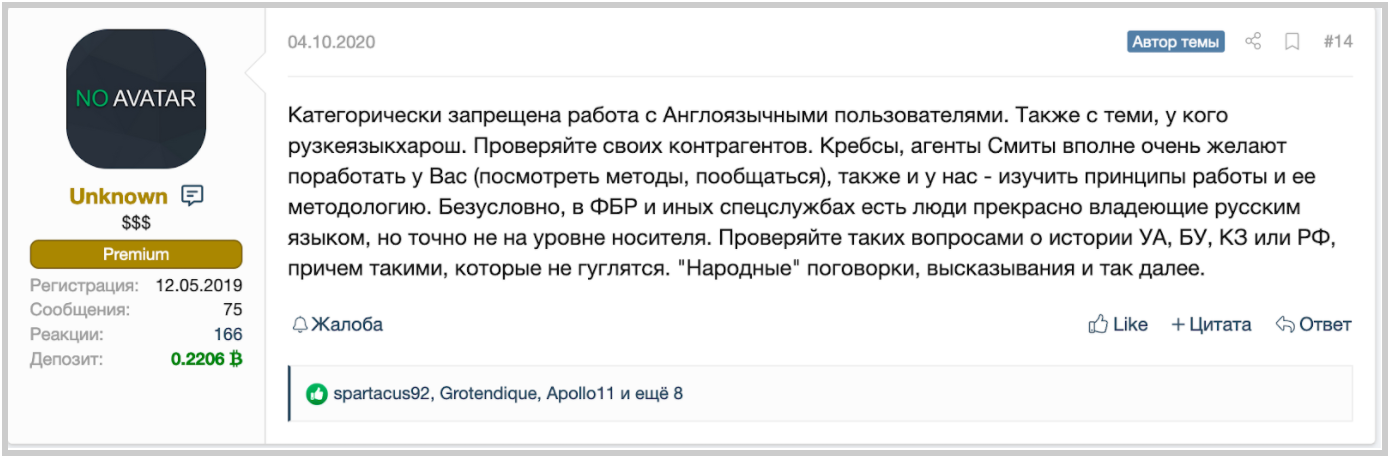
Table of contents
Developing a hacker reputation
The Russian YouTube channel “Russian OSINT” creates and publishes news about cyber crime from the hackers point of view. The channel often shares interviews of Russian cyber experts or former hackers. However in October of 2020, the channel published a seminal interview of a Russian hacker from the ransomware gang, REvil. The REvil member interview was significant in that a malicious and still active hacker agreed to answer questions regarding theirs activities. The hacker used the word “partners” to describe people involved with REvil in their exploits to increase the gang’s revenue. It appears the REvil ransomware gang develops and follows operational processes to run their business.
Value of reputation in cybercrime
This Russian OSINT channel interview appears to be part of REvil’s recruitment process by sharing and emphasizing their business reputation. And, it appears to have worked. The cybersecurity community was stunned in September 2020, when a hacking forum member made a deposit of 1 million dollars on that forum. This deposit appears to have been made to to attract new people to join the gang. A member of the cybercriminal gang recently confessed that they are facing a recruitment problem, particularly attracting hackers with the skills, competency, and culturally fit to join the group. Among the hacker candidate requirements, is of course, experience and knowledge of information technology, but more surprisingly is that of being a proficient Russian speaker. 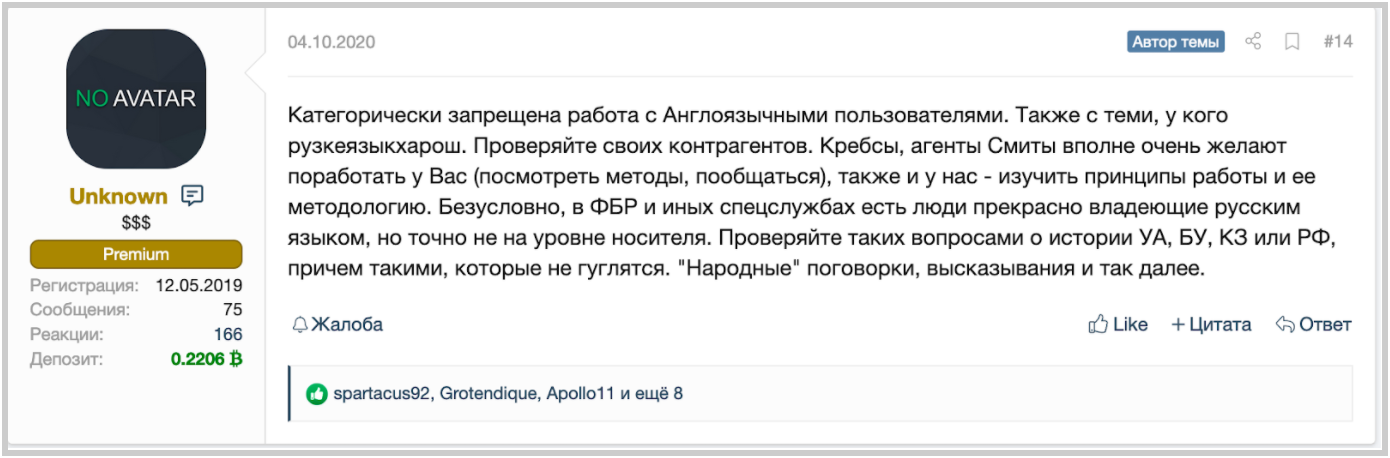
What is a hacker reputation?
The definition of reputation is “an opinion based on the past behavior.” In cybercrime, reputation is a question of trust. Whether you are an enthusiast, a hacker, or a buyer on Dark Web forums, everything relies on trust. A significant problem in the cybercrime community is you don’t know with whom you are talking. Is the person really who she/he tells me she/he is? Building a reputation is critical for hackers. This can be difficult as the true identity of a cybercriminal is purposefully hard to ascertain. Therefore, hackers often use and guard their pseudonym to stop it from being used by other cybercriminals. Hackers mark their work with the same pseudonym everywhere on the dark web. This practice gives the hacker recognition, and over time, they are recognized as a trusted member of the community. Reputation is essential for hackers seeking to become an important actor or leader in the cybercrime community.
Hackers target other hackers
Similar to the business world, when you have a good reputation you are often the target of scams. Frequently scammers steal the pseudonym of a famous and trusted actor for use in places the ‘real actor’ only includes their signature. Bad actors often steal more than a pseudonym. Rival gangs have chosen to publish data breached by other hackers or gangs to increase their popularity within the community. This is a common practice, as it is difficult to know who stole what, because there is rarely clear proof. Even in the ransom domain, it happens that different actors have ransomed the same data to the same company. The concurrence is high in this niche, which means even in this scenario there may be a need to defend reputation with respect to other competitors.
Hackers guarding their reputations
The hacker protects his/her pseudonym, as well as the reputation of their group. Reputation is key to ensuring others will want to do business with them, and resolve any dispute that may occur between partners or victims. Should you be the unfortunate victim of cybercriminals, think twice before doing business with the hacker. We highly advise against negotiating with cyber criminals; however if you choose to do so, check the hacker’s or gang’s reputation in dealing with other victims before doing anything.
Moral of the story
As in cybercriminal world the reputation is the key, the actors don’t stop at stealing data from one another. Actors often publish the data leaks provided by other people simply to increase their popularity in the community. Even in the ransomware domain, different actors have attempted to ransom the same company over the same breached data. Therefore, cybercriminals find it critical to defend their reputation, even from their competitors.

