Vulnerability Threat Intelligence: A 5-Step Framework

Table of contents
What happens when the weakest link in your ecosystem is exposed? Vulnerabilities are hiding everywhere, and more often than not they go undetected before being exposed and exploited by threat actors with malicious intent.
Many software organizations seek to detect and patch vulnerabilities as they occur, but in most cases, attackers are faster. Fortinet researchers discovered that it takes attackers 5.4 days on average to exploit disclosed vulnerabilities.
Non-profit organization Mitre indexes disclosed vulnerabilities in their Common Weakness Enumeration (CWE). Attackers use this as a guide, preying on vulnerabilities before companies react.
An X post from Microsoft detailing how vulnerabilities can lead to ransomware attacks.
New innovations such as automatic scans used by hackers allows them to perform large-scale reconnaissance campaigns, exploiting obvious vulnerabilities and detecting which assets can be exploited with minimal effort.
In this guide, you‘ll discover how to build an informed threat vulnerability management framework to stop your critical infrastructure from being compromised.
Vulnerability intelligence in numbers
New vulnerabilities are emerging every day. From 2024 – 2025, novel vulnerabilities have been the most prolific attack vector for hackers seeking to break in.
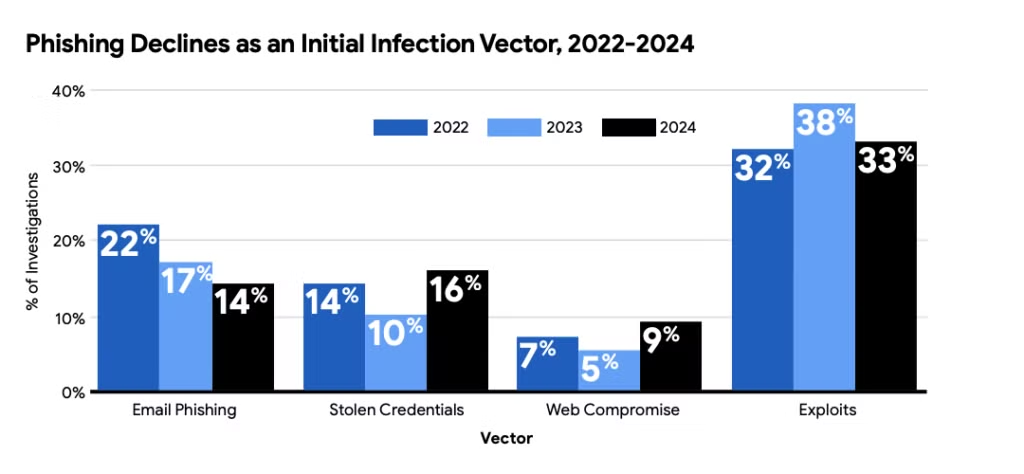
- Vulnerability exploit compromise rose to 33% in 2024, becoming the most popular initial entry tactic.
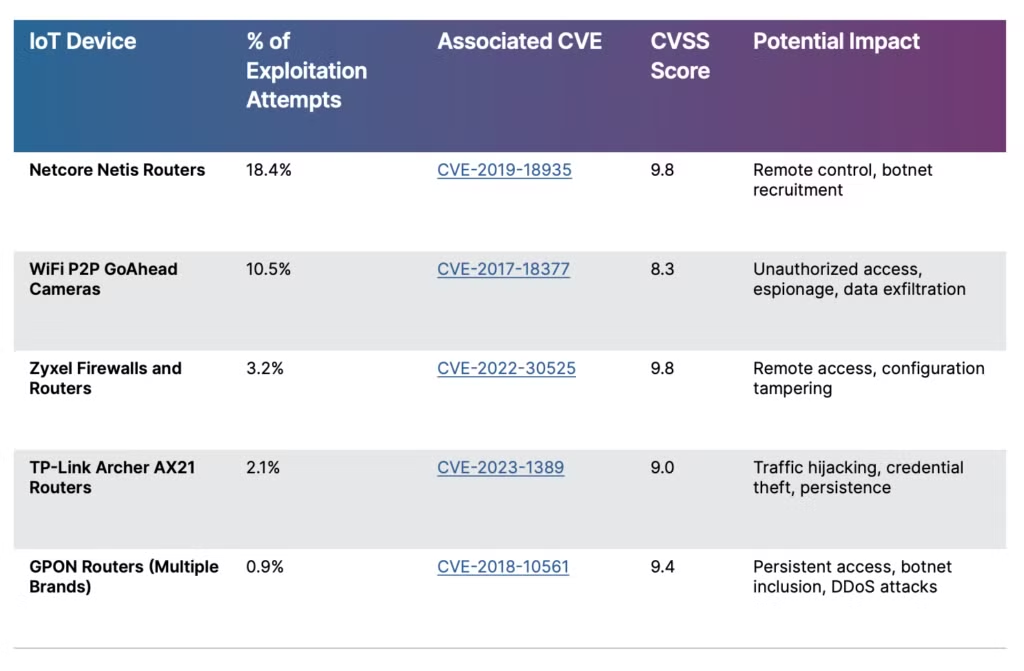
- Threat actors are using automation to perform exploit attacks, launching 97 billion exploitation attempts in 2025.
- 56% of 40,000 vulnerabilities in 2025 could be exploited without any authentication.
- 29% of incidents targeted North America.
How hackers are using automation to find vulnerabilities
To find and exploit vulnerabilities before they‘re patched, hackers are using sophisticated tools to automate attack surface mapping, optimizing their exploit campaigns.
Threat actors have been observed using:
- SIPVicious: Used in nearly 50% of all detected scanning events to discover SIP (Session Initiation Protocol) servers, phones, and gateways on a network. Threat actors adapted legitimate SIP software to exploit vulnerable SIP servers.
- Nmap: Also known as Network Mapper, this open-source tool regularly used by professionals is for network exploration and security auditing. Threat actors use Nmap to scan networks and identify open ports and vulnerable services.
- Nessus: A commercially available vulnerability scanner, threat actors use Nessus to identify vulnerabilities and misconfigurations to prioritize weak entry points.
The large uptick in automated vulnerability scans means threat actors can identify and exploit weaknesses before organizations have a chance to react. To counter this, cybersecurity specialists have to ensure they‘re always at the forefront of emerging vulnerabilities.
Let‘s dive into how to set up your vulnerability intelligence framework before a breach occurs.
5 step system: Applying vulnerability intelligence
Building your vulnerability intelligence framework starts by understanding the potential weaknesses in your assets, then prioritizing remediation strategies without excessive down time.
1. Gather your data
Cybersecurity professionals can start by aggregating valid vulnerability data from various sources. To get a complete picture, it‘s best to check public CVE repositories, vendor advisories, threat research blogs, underground forums, and private intelligence reports. This variety will give teams a comprehensive view of known and emerging threats.
Our Cyber Threat Intelligence platform can curate specialized lists of emerging threats so teams can stay on top of the changing landscape.
2. Contextualize the data
Next, teams should put the vulnerabilities into context to better determine the real-world risk. It‘s important to consider whether current CVEs have been linked to an APT (Advanced Persistent Threat), or whether news outlets have already publicized the vulnerability.
3. Prioritize based on business risk
When a vulnerability is labelled as “critical” by outside sources, it can be easy to get lost in the weeds. It‘s important that cybersecurity professionals evaluate the risk to the organization by considering:
- Are attackers targeting your industry?
- Is the software being used internally or externally at risk?
- Does the vulnerability affect business critical operations?
Internet-facing vulnerabilities must be identified and patched quickly, as hackers can find a way in through open ports and other zero-day exploits.
4. Launch a fix
As soon as vulnerabilities are prioritized, it‘s time to act.
- Patch critical vulnerabilities, either with automation or manually.
- Consider virtual patching, using WAFs and API gateways inspect traffic and block malicious patterns without modifying the underlying system.
- Segment networks to protect high-value assets when a patch isn‘t immediately available.
- Increase monitoring to detect exploitation attempts early. SIEM alerts and anomaly detection can be useful for low-severity vulnerabilities.
5. Reporting & learnings
Once the system is secure, it‘s time to log all activity to refine your vulnerability management lifecycle.
Data can be fed back into the SIEM and SOAR systems to turn raw findings into actionable detection, automation, and response.
Improving automation results reduces time to remediation, eliminate repetitive manual tasks, and respond to threats in real-time.
FAQs
Vulnerability intelligence is the process of collecting data to inform security decision-making so organizations can reduce risks to their cyber infrastructure.
Vulnerability management is the ongoing process of identifying, investigating, assessing, reporting, and patching vulnerabilities.
Vulnerability intelligence on the other hand, are the insights that direct where and how vulnerabilities are to be managed.
Organizations need both to stay on top of emerging vulnerability threats to prevent devastating breaches.
There are many different types of vulnerability intelligence that all have their own purpose:
Raw vulnerability feeds: Unprocessed data from foundational sources that list emerging vulnerabilities. This includes CVE entries, CVSS scores, and reports from affected products.
Exploit intelligence: Whether a vulnerability can actually be exploited including the practical risk. This includes public exploit codes, circulating malware kits, exploits used by ransomware groups, maturity of the exploit, and EPSS (Exploit Prediction Scoring System) scoring.
Threat contextualized intelligence: Puts the threat within the context of real-world activity. This includes CISA KEV (Known Exploited Vulnerabilities) status, campaigns targeting specific CVEs, industry specific exploit campaigns, and attack path analysis.
Patch intelligence: Focuses on the availability, quality, and impact of patches or mitigations to help teams plan safe, fast remediation. This includes patch availabilities and release dates, patch reliability, patch urgency, temporary mitigations, and downtime from patching operations.
Zero-day intelligence: Intelligence that helps security professionals defend against zero-day exploits before a patch is available. This includes, IoCs, hacker attack patterns, threat actor attribution, and patch intelligence timelines.
CVSS scores are standardized numerical ratings (from 0 to 10) that measure the severity of a software vulnerability, helping organizations understand how dangerous a vulnerability is and how urgently it should be fixed.
Here‘s a breakdown of the CVSS scoring system:
Score Range
Severity
0.0
None
0.1–3.9
Low
4.0–6.9
Medium
7.0–8.9
High
9.0–10.0
Critical
Automation is useful because it shortens the gap between when the vulnerability is discovered and when it can be fixed.
Automating vulnerability fixes reduces human workload, errors, and bottlenecks that can prevent teams from addressing vulnerability exploits before they cause a breach.
Cybersecurity professionals can stay updated with the latest emerging vulnerabilities by looking at these sources:
Vulnerability databases: NVD (National Vulnerability Database), MITRE CVE List, and CISA‘s Known Exploit Vulnerabilities (KEV) Catalog.
Vendor databases: Google Exploit Database, CISCO Security Advisories, and Microsoft Security Response Center.
Open-Source Intelligence (OSINT): GitHub Advisory Database and Open Source Vulnerability Database.
Threat intelligence feeds and blogs: Bleeping Computer, DarkReading, and SecurityWeek.
Dark web forum monitoring: CybelAngel‘s Dark Web Monitoring Service.
Wrapping up
Supply chain compromise is a real risk facing businesses going forward into 2026. Threat actors harnessing automation to execute their attacks, many bypassing authentication in the process, means attackers can rely less on phishing attempts to break in.
CybelAngel provides comprehensive Threat Intelligence Platform to find and prioritize vulnerabilities in a curated feed, so you can get ahead of malicious actors. Gather data on critical vulnerabilities, profile specific threats targeting your systems and industry, and narrow in on known IoCs like malicious IP addresses, domains, and file hashes.

