How to Prevent DDoS Attacks: A 2026 Guide for Security Teams
Table of contents
- 1. What are DDoS Attacks?
- Types of DDoS attacks
- A quick DDoS glossary
- 2. Are DDoS attacks illegal?
- Is DDoS illegal in the US?
- Is DDoSing illegal in the UK?
- The bottom line
- 3. What is the scope of DDoS attacks in 2026?
- 4. What are the consequences of DDoS attacks?
- Service disruption
- Financial losses
- Reputational damage
- Opportunity costs
- Legal implications
- Service degradation
- Psychological impact
- 5. What are some recent examples of DDoS attacks?
- 6. How can DDoS attacks be prevented?
- 7. How to recover from a DDoS attack?
- 8. What can we expect from DDoS attacks in the future?
- A final word
DDoS attacks more than doubled in 2025. Cloudflare blocked 47.1 million attacks across the year, a 121% increase over 2024, peaking with a record-breaking 31.4 Tbps assault in Q4. Network-layer attacks grew 700% year-over-year. The average organisation is now being hit 139 times per day.
For US security teams, DDoS is no longer a periodic disruption risk, it is background noise that must be actively managed. Financial services, healthcare, and critical infrastructure remain the primary targets, with ransom DDoS campaigns increasingly used as cover for deeper intrusions. This guide covers how DDoS attacks work in 2026, the vectors that have changed, and the specific controls and response steps that stop them.
1. What are DDoS Attacks?
DDoS stands for ‘Distributed Denial of Service’. DDoS attacks involve overwhelming a target system with a flood of traffic from multiple sources, rendering it incapable of serving legitimate requests.
These cyberattacks leverage a network of compromised computers, often referred to as a “botnet”, to bombard the target system with traffic spikes.
But, what is denial of service? This refers to how the sheer volume of traffic exhausts the target’s resources, leading to service disruption or a complete outage.
Types of DDoS attacks
Here are some of the most common types of DDoS attacks to be aware of.
- Volumetric attacks: Volumetric DDoS attacks flood the target server or network with a high volume of traffic to consume the available bandwidth and resources, causing the network or system to slow down or crash.
- Protocol attacks: Hackers can exploit weaknesses in network protocols, consuming server resources and rendering them unavailable to legitimate users. Common examples of protocol attacks include TCP SYN floods.
- Application layer attacks: Also known as layer 7 attacks, these target specific services or applications on a server, taking advantage of vulnerabilities in the web application layer to exhaust server resources.
- Low-rate attacks: These attacks are designed to appear as legitimate traffic, bypassing traditional anti-DDoS defense measures. Internet traffic may occur at a low rate, making it difficult to detect and prevent.
- IoT-based attacks: These cyberattacks leverage vulnerabilities in unsecured connected devices such as cameras and routers to overload a targeted system with malicious traffic. An example is the Mirai botnet.
- Spoofed attacks: These attacks use a fake source IP address to hide the attacker’s identity and bypass authentication measures, making it difficult to detect any malicious traffic.
- Application-layer DOS: These attacks target specific applications or services. Common examples include HTTP floods, which overload servers with HTTP requests, and DNS amplification attacks, which exploit vulnerabilities in the domain name system.
A quick DDoS glossary
Before we go any further, here are some keywords that you might hear mentioned frequently in the DDoS landscape.
- Content delivery network (CDN): A group of web servers that cache content geographically near to their users
- Latency: The delay that a user experiences when they run a specific action
- Network bandwidth: The capacity of any given network, and a reflection of its speed and quality
- Load balancers: A technique to distribute network traffic across different resources to process them more efficiently
- Firewalls: A network security system that surveys and monitors traffic
- Web application firewall (WAF): Protects web applications by tracking traffic to and from the Internet
- User Datagram Protocol (UDP): A time-sensitive Internet communication protocol that sometimes falls victim to ‘UDP flood attacks’
- DDOX: Finding someone’s personal details and leaking them
- Internet Control Message Protocol (ICMP): A network layer protocol that can diagnose any communication issues
2. Are DDoS attacks illegal?
DDoS attacks are generally considered illegal in most jurisdictions. These attacks can cause significant harm to targeted systems, networks, and users, disrupt services, and result in financial losses for businesses.
Is DDoS illegal in the US?
In the United States, DDoS attacks are considered cybercrimes and can be prosecuted under the Computer Fraud and Abuse Act (CFAA). The CFAA makes it illegal to intentionally cause damage to a computer or computer network without authorization. DDoS attacks fall under this definition as they aim to disrupt or deny service to legitimate users.
Is DDoSing illegal in the UK?
In the UK, DDoS attacks could lead to a prison sentence or a fine, as the Computer Misuse Act makes it illegal to impair or block access to computer programs and data without prior authorization.
The bottom line
Laws and regulations may vary between countries, so the legality of DDoS attacks may differ depending on the jurisdiction. However, in general, launching or participating in a DDoS attack is considered illegal due to the harm and damage it can cause.
3. What is the scope of DDoS attacks in 2026?
Or to be specific let’s review what has changed for US security teams in 2026.
- AI has made DDoS-as-a-Service accessible to anyone. Platforms like GhostGPT now let attackers configure and launch a campaign with a text prompt, renting botnet capacity for under $20. In February 2026, the FBI and Europol’s Operation PowerOFF disrupted 27 DDoS-for-hire services — but the underlying market immediately rebuilt. US financial services and healthcare organisations are the primary commercial targets.
- Hyper-volumetric burst attacks grew 700% in 2025. The record-breaking 31.4 Tbps attack blocked by Cloudflare in Q4 2025 lasted just 35 seconds. These are no longer sustained floods — they are precision bursts timed to overwhelm automated mitigation before it activates. US critical infrastructure operators, including energy and water utilities, have seen this pattern in documented 2025 incidents flagged by CISA.
- Application-layer (L7) attacks rose 74% year-over-year in Q2 2025. Unlike volumetric floods, L7 attacks mimic legitimate user traffic — HTTP requests, DNS queries — making them nearly invisible to traditional detection tools. US e-commerce and SaaS platforms are disproportionately targeted because their applications are always internet-facing.
- DDoS is now routinely used as a smokescreen. A volumetric attack draws the SOC team’s attention while a separate intrusion exploits a deeper vulnerability in the same window. In 2025, multiple US banks and payment processors received ransom DDoS demands followed by simultaneous credential stuffing campaigns targeting their login infrastructure. CISA specifically flags this dual-vector pattern in its 2025 critical infrastructure guidance.
4. What are the consequences of DDoS attacks?
So what happens when you get DDoSed? DDoS attacks can have severe repercussions on organizations, individuals, and the overall digital ecosystem.
Service disruption
The primary impact of a successful DDoS attack is the disruption of online services. This can lead to downtime, making websites and applications inaccessible to legitimate users—affecting the overall user experience.
Financial losses
Downtime resulting from DDoS attacks can translate into significant financial losses for businesses. In addition to direct revenue impact, organizations may also incur additional costs associated with remediation efforts from response teams, legal implications, and reputational damage control.
Reputational damage
The aftermath of a DDoS attack can tarnish an organization’s reputation. Following any issues or blockages, users may perceive the organization as being unreliable, leading to erosion of trust and potential loss of business.
Opportunity costs
Beyond immediate financial implications, DDoS attacks can result in missed business opportunities. Organizations may lose out on potential sales, partnerships, or strategic initiatives due to the unavailability of their online services.
Legal implications
Depending on the nature of the targeted industry and the impact of the attack, organizations may face legal consequences. Regulatory bodies may impose penalties for failing to protect customer data or maintain service availability.
Service degradation
Even if a DDoS attack does not completely disrupt services, it can still lead to significant degradation in service quality. Slow response times, unresponsiveness, and intermittent outages can all result from DDoS attacks.
Psychological impact
DDoS attacks can have a psychological impact on users and employees. Users may feel vulnerable and hesitant to engage with a platform that has been targeted, while employees may experience stress and anxiety when trying to restore services under attack.
5. What are some recent examples of DDoS attacks?
The world has witnessed several high-profile DDoS attacks in recent years, including:
- GitHub: In 2018, GitHub faced a DDoS attack which used an amplification technique to send huge amounts of traffic to their site
- Amazon: In 2020, Amazon Web Services announced that it had to counteract a huge DDoS attack
- Google: In 2023, Google stopped a DDoS attack that was 7.5 times larger than previous attacks on record (see chart below)
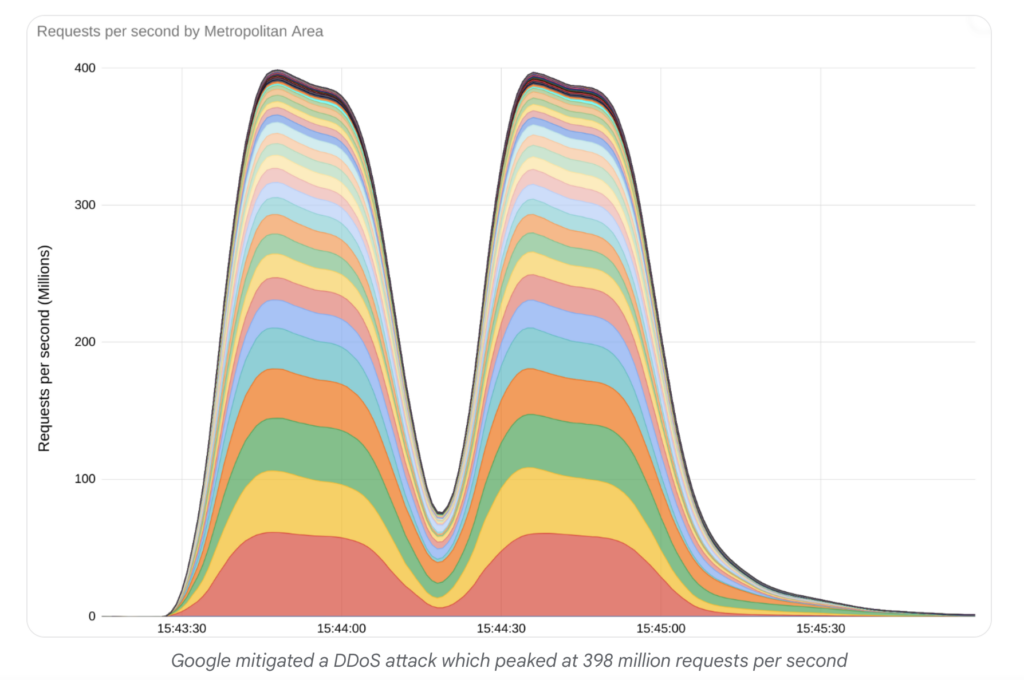
These examples show that any company can face DDoS attacks—no matter how established they are. So, what can protect your network from DoS attacks?
6. How can DDoS attacks be prevented?
What is the best defense against a DDoS attack?
If you’re wondering how to defend against DDoS, here are 7 cybersecurity best practices and anti-DDoS software recommendations to protect any organization.
- Regular network monitoring: Real-time monitoring helps proactively identify and mitigate suspicious traffic patterns.
- Scalable infrastructure: Designing a scalable infrastructure with excess capacity can absorb sudden spikes in traffic and ensure business continuity.
- DDoS mitigation services: Employing professional DDoS mitigation services, such as CybelAngel, allows organizations to leverage the expertise of specialized providers who can monitor web traffic and apply necessary filtering techniques to thwart attacks.
- Traffic rate limiting: Implementing rate-limiting measures detects abnormal traffic patterns and restricts traffic from suspicious sources.
- Application Layer Security: Ensuring robust application layer security prevents attacks targeting vulnerabilities in web applications and APIs.
- Intrusion Prevention Systems (IPS): IPS systems detect and block malicious traffic by inspecting them and comparing them against known attack patterns.
- Incident response planning: Having a well-defined incident response plan enables organizations to mitigate attacks promptly and minimize the impact on services.
So, can you stop a DDoS attack? These measures can certainly make a difference.
Prevention is better than cure, and the best DoS protection strategies will safeguard your organization against external cyber threats.
7. How to recover from a DDoS attack?
What if, in spite of your best efforts, a DDoS response is required?
To recover from a DDoS attack, organizations can take the following steps:
- Analyze and understand the attack: After a DDoS attack, it is essential to analyze the scale, duration, and attack vectors used. This analysis guides the recovery strategy to prevent future attacks.
- Mitigate the attack: Implement measures to mitigate the ongoing attack and minimize its impact. This may involve filtering and blocking malicious traffic, deploying DDoS protection services or solutions, and working with Internet service providers (ISPs) to block traffic originating from the attack.
- Restore services: Once the attack is mitigated, organizations should restore affected services and systems. This may involve checking the integrity of affected systems, repairing any damage caused, and verifying the functionality of associated applications and services.
- Learn and improve: After recovering from a DDoS attack, it is important to conduct a post-incident analysis to identify vulnerabilities, weaknesses, and areas for improvement. This analysis can help organizations enhance their security measures and develop a more robust defense strategy against future network traffic attacks.
It is also crucial for organizations to have proactive measures in place to prevent and mitigate future DDoS attacks. This includes implementing comprehensive DDoS protection solutions, conducting regular security assessments, staying updated with security patches, and educating employees about the risks and signs of DDoS attacks.
Every DDoS attack is unique, and the recovery process may vary based on the specific circumstances. Engaging with cybersecurity professionals, such as CybelAngel, and consulting industry-specific guidelines can provide organizations with tailored guidance for recovery.
8. What can we expect from DDoS attacks in the future?
The numbers are still climbing. Here is what security teams should be tracking over the next 12 to 18 months.
- Volume will keep growing. StormWall forecasts 58 million attacks mitigated in 2026, nearly three times the 2025 figure. For US organisations, that means DDoS pressure is a constant, not a calendar event.
- Attacks will get smarter, not just bigger. AI tools are already automating campaign setup. The next step is adaptive attacks that profile your defences and rotate vectors in real time. Static mitigation rules will struggle to keep up.
- Ransom DDoS and data theft will arrive together. In 2025, several US banks received ransom demands alongside demonstration attacks, with credential stuffing running in parallel. That combined model is spreading across sectors. By 2027, a standalone DDoS attack on a US enterprise will be the exception, not the rule.
- US regulators will formalise resilience requirements. CISA’s dual-vector guidance is the starting point. Expect DDoS incident reporting thresholds, similar to the SEC’s 72-hour disclosure rule, to follow for critical infrastructure operators.
A final word
DDoS prevention in 2026 is not solved by mitigation services alone. Attackers begin by identifying what’s exposed on your internet perimeter, open ports, unpatched services, misconfigured APIs, before they launch. The organisations that detect and contain DDoS fastest are those with continuous visibility into their external attack surface before the attack starts.
CybelAngel’s attack surface management monitors your internet-facing assets continuously, alerting your team to the exposed services and vulnerabilities that DDoS actors and their follow-on intrusion attempts rely on.

