Data leak of 36 million user accounts : a brutal “awareness” campaign

Table of contents
A Romanian hacker acting under the pseudonym GhostShell has posted 36 million user accounts stolen by compromising 110 MongoDB databases. Among these accounts, 3.6 million are coupled with passwords.
A notorious hacker
The young 24-year-old Romanian hacker has already attracted attention several times in the world of cybercrime through his leading role in the former hacktivist team “Team GhostShell.” Between 2012 and 2015 this team attacked several governmental entities (US, Russian, etc.) and private actors by posting millions of pieces of confidential data. More recently, the hacker GhostShell made headlines by revealing his identity and his motivations in March 2016 during an interview granted to databreaches.net, hoping to get a job in a cyber security firm. This attempt refers to the myth that many hackers are hired by American companies in order to take advantage of their skills and “field experience.” After this unsuccessful attempt, he returned to the cybercrime scene by taking his fights online.
Anatomy of the data
The posting of the data was announced on GhostShell’s Twitter account. In fact, he posted a link (already followed by more than 7700 individuals) to the PasteBin site to adapt and convey his message to a wide audience. Within this page, it is possible to recover the entire information leak as an archive hosted on multiple download platforms, but also from links to screen shots that show: 1. The lack of security of the servers that he compromised 2. Previous visits by hackers on these same servers 5.6 GB of uncompressed components are thus available. The 110 files comprising the archive are likely named according to the IP address where the compromised data was hosted. 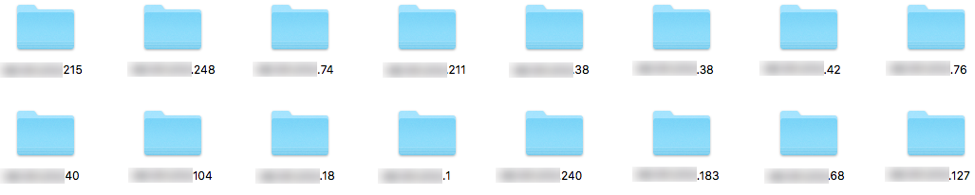 Each folder is organized as a mirror and always shows three distinct types of information: • A folder named “database” that contains data specific to the industry of the company that owns the server. Therefore, there are different kinds of available data: email addresses, passwords, geolocation, domiciliation addresses or users’ IP addresses • A folder named “General Info,” which provides technical data about the owner of the database • A screen shot taken by the hacker as evidence
Each folder is organized as a mirror and always shows three distinct types of information: • A folder named “database” that contains data specific to the industry of the company that owns the server. Therefore, there are different kinds of available data: email addresses, passwords, geolocation, domiciliation addresses or users’ IP addresses • A folder named “General Info,” which provides technical data about the owner of the database • A screen shot taken by the hacker as evidence
An awareness campaign
Under the auspices of an operation called ProjectVoriDazel, GhostShell wishes to convey a message to all MongoDB database users and programmers. He denounced the lack of security and seriousness during the configuration of these systems that host and administer internal documents or user data (logins, passwords, personal information etc.). In fact, the default configuration of the MongoDB protocol does not require identification. The developer is responsible for configuring basic protection by an authentication system. His message carries even more weight when he explains that these databases were discovered through turnkey software that scans ports and the connected objects search engine Shodan which appeared in 2009. The action taken by the hacker echoes various whistleblowers who assume the characteristics of cyber security researchers like Chris Vickery, who has repeatedly informed the press about the free access to multiple databases such as those of Hello Kitty (3 million accounts) or MacKeeper (13 million pieces of user data). Although the hacker’s method is clearly questionable since he is exposing 36 million internet users to phishing campaigns and other cybercrime attacks, he does raise an important question about the securing of personal data (users, customers or partners) by companies: indeed it is still too often seen as a subsidiary aspect in the development of a product, whatever that product may be.
Below is the full statement of the hacker
For more than a few years now various people across the net have been signaling an on-going vulnerability within the new MEAN Stack system of client/routing/server. The successor of the LAMP Stack, an already infamous vulnerable platform, many thought this new one is more secure, yet it’s almost the exact same as its predecessor. MySQL typically replaced by NoSQL and the main database configuration managed by MongoDB. This project will focus solely on this poorly configured MongoDB. I’d like to mention exactly how easy it is to infiltrate within these types of networks but also how chilled sysadmins tend to be with their security measures. Or should I say, lack thereof. In a lot of instances the owners don’t bother checking for open ports on their newly configured servers, not only that but they also don’t concern themselves with establishing a proper authentication process. (Just a simple username/password) Typical open ports: 22, 53, 80, 81, 110, 137, 143 443, 465, 993, 995, 3000, 8080, 27017, 3306, 6379, 8888, 28017, 64738, 25565 This can basically lead to anyone infiltrating the network and managing their internal data without any interference. You don’t even have to elevate your privileges, you just connect and have total access. You can create new databases, delete existing ones, alter data, and so much more. I am leaking more than 36 million accounts/records of internal data from these types of networks to raise awareness about what happens when you decide not to even add a username/password as root or check for open ports, let alone encrypt the data. Each server folder has within it a plaintext file with the general info of the target, a screenshot from within my MongoDB client with me having access and of course the leaked data in raw text. There are a few million accounts with passwords and the rest is private person data or other types. This should serve as a cruel reminder of what happens when you don’t use proper security hygiene. And don’t worry if you thought this is the only vulnerability out there, guess again. The old ones remain as well.

