How OTP Bots Are Exploiting Two-Factor Authentication (+ What To Do)

Table of contents
Two-factor authentication (2FA) has long been considered the best way to secure accounts against account takeovers (ATO). Enter OTP bots—a sophisticated hacker solution to bypass 2FA.
One-time passwords (OTPs) aren‘t as secure as you think. Attackers have evolved, finding new ways to trick users into handing over their OTPs and compromising the entire organization.
In this article, we‘ll uncover the emerging OTP risks facing cybersecurity professionals and how you can secure your account against two-factor authentication bypass.
The rise in account takeover fraud
ATO cases are growing fast. Hackers are targeting identity verification platforms to trick victims into sharing access to their accounts—especially financial institutions.
Threat actors use social engineering schemes to gather credentials and other identifiable information from large corporations before launching their attack.
Here‘s the breakdown:
- Account takeovers rose to 53% with 22% of all ATOs being bank accounts.
- The FBI announced that during 2025, more than 5,100 complaints were lodged reporting ATO fraud, with losses exceeding $262 million.
- Gartner predicts that by 2028, 40% of all social engineering attacks will target executives and employees.
How hackers use OTP bots to take over accounts
To save time and scale up their attacks, hackers are using OTP bots to compromise accounts. New tools, like JokerOTP and BloodOTPbot, have become more popular and accessible, facilitating account takeover campaigns.
Between 2023 and 2024, threat intelligence reports mentioning [OTP bots on dark web forums surged by 31%]
Financial institutions and Fintech platforms are more widely targeted because of their vast funds. OTP bots alone have contributed to over $10 million in fraud losses.
1. Reconnaissance
The first step for an attacker is to gain in-depth information on the target. Hackers work to compromise accounts that could escalate to administrative privileges or those in positions with higher permissions.
To gather information, attackers:
- Deploy phishing attacks: Emails, SMS, or social media are used to send malicious links or attachments to the target in the hopes that one click will give them valid credentials.
- Scan ports: Exposed or misconfigured ports give attackers a glimpse into the organization‘s IT infrastructure, narrowing down their attack plans.
- Search the dark web: In online forums, cybercriminals can purchase valid login credentials from databases, increasing their chance of success.
- Social engineering: Hackers aim to deceive the victim by posing as tech support, a bank, or a vendor for the organization. OTP phishing, for example, puts the attacker in a position of trust for the victim to give up their one-time password (OTP).
2. Initial access
Cybercriminals then shift gears to obtain the user‘s login credentials and test which accounts would be ideal for an OTP attack.
Attackers do this by:
- Credential stuffing: Hackers use usernames and passwords from earlier research and test them across sites. Many employees reuse their passwords, making a compromise more likely.
- Malware and infostealers: Threat actors use custom malware scripts to harvest credentials by extracting saved passwords from the browser, stealing session cookies, or logging keystrokes with infostealers.
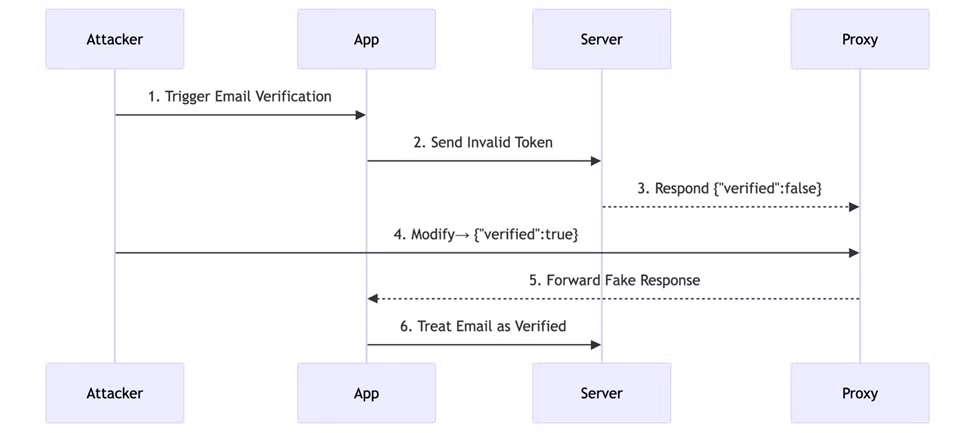
3. OTP interception
When an attacker has successfully obtained credentials from the victim, they trigger a specialized bot network to bypass multi-factor authentication protocols.
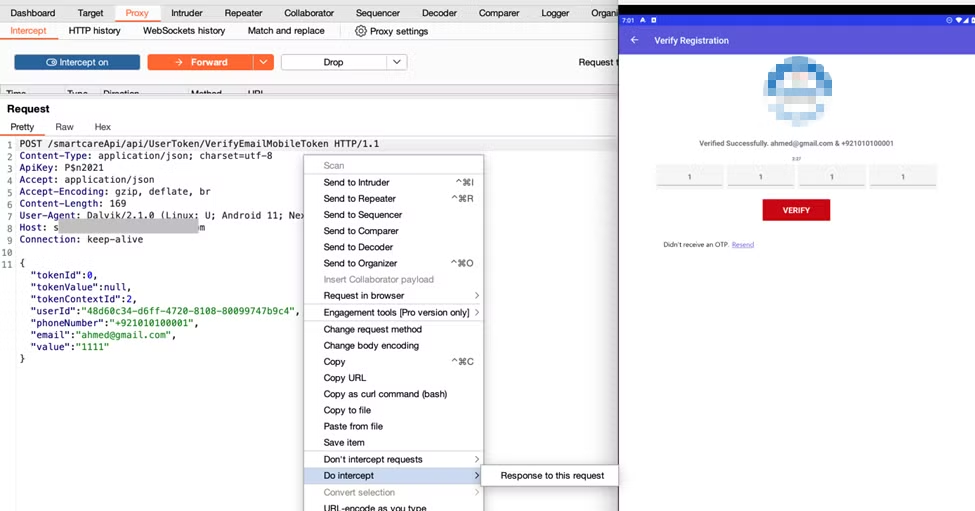
This is how an OTP bot service works:
- Hackers set up the OTP bot system to gain access to the target account. The attacker first logs in to trigger the bot and waits for the bot to return the OTP.
- Once activated, OTP bots generate a fraudulent SMS message, email, or AI-generated voice call to the victim. The bot uses a pre-determined script to convince the victim that their account is compromised, pressuring them to send the OTP to secure the account.
- Once the victim enters the OTP sent by the bot, it‘s sent to the attacker in real-time.
In the past, hackers relied on SIM swapping or SMS interception that relied on exploiting the telecom provider and the victim to take over the account. With OTP bots, SMS interception is done by the bot, forwarding the message to the attacker directly.
4. Account compromise
Once the attacker has the OTP, they can now bypass the two-factor authentication process. The hacker can now legitimately log into the victim’s account and gain control.
5. Persistence
To hold onto access to the victim‘s account, the hacker then works to secure the account, making it impossible for the victim to regain control.
Threat actors use a few techniques to accomplish this:
- Password change: Attackers change the password to the user‘s account so they‘re unable to log back in.
- Replace MFA devices: Threat actors change the MFA authentication from connecting to the user‘s phone or authenticator app to their own.
- Change recovery email: To ensure that the victim can‘t regain access to their account, hackers replace the recovery email with their own or add a new phone number.
6. Lateral movement
When an attacker has gained access to a legitimate account, they can use the account against the organization.
Attackers use legitimate accounts to give themselves higher permissions, allowing them to move within the organization‘s systems.
7. Command and control (C2)
Once the system is under the adversary‘s control, they begin exfiltrating sensitive data to their own servers. Hackers often mimic expected traffic patterns, making them even more difficult to detect.
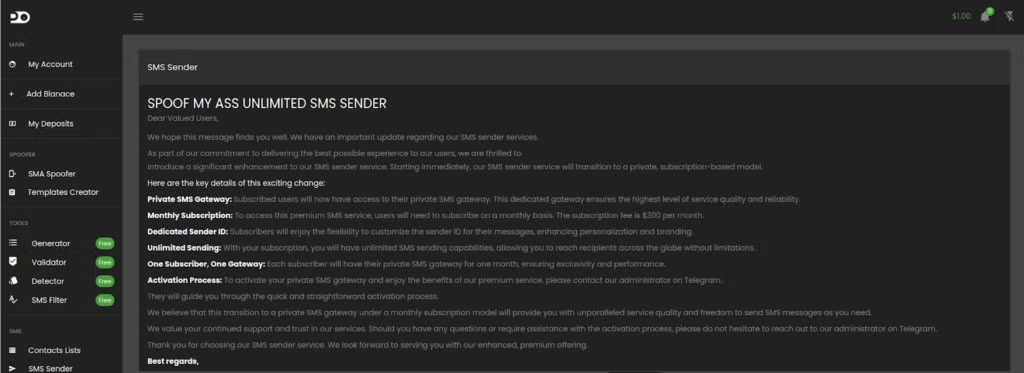
Crimeware as a service
Crimeware-as-a-service has fueled the growth of OTP bots on the dark web. Affordable pricing and accessible tools mean businesses face growing risk from scalable, real-time social engineering attacks.
OTP bot services offer user-friendly dashboards, customizable scripts, and step-by-step guides, making them easy to use even for entry-level attackers.
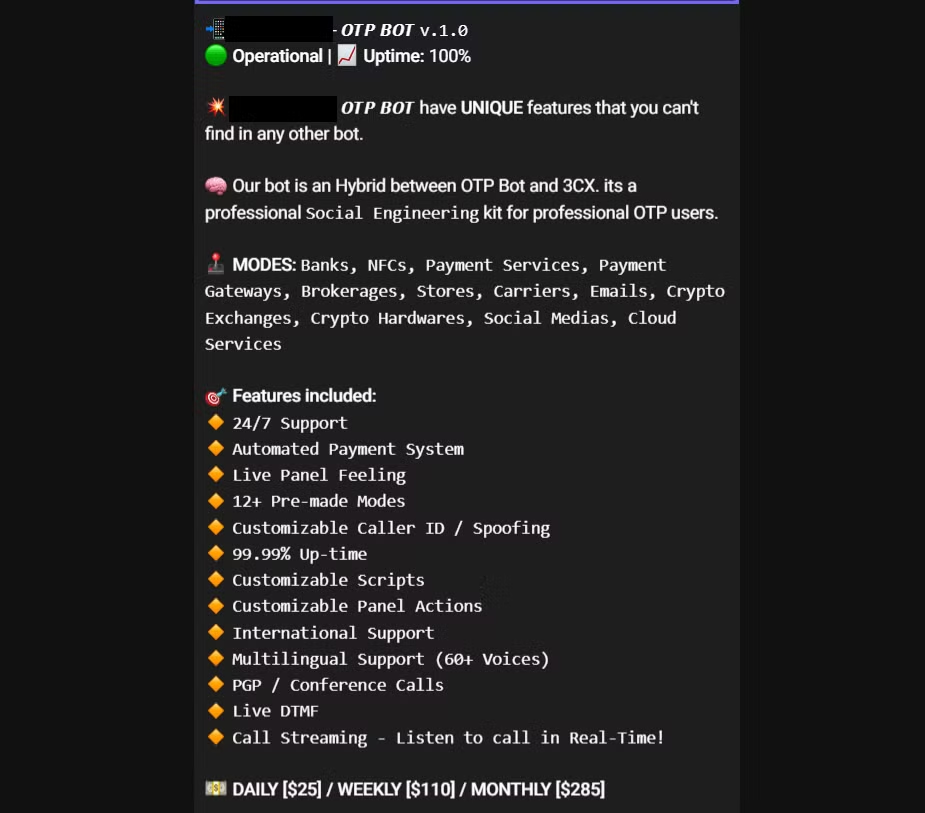
Telegram has become a centralized marketplace for various types of hacking services. Cybercriminals can hop onto dedicated chats where OTP bot packages are presented to target different vectors, including social media platforms, fintech apps, and cryptocurrency wallets.

Prevent account takeovers
The most effective fraud prevention doesn’t just react to bots when they request an OTP—it stops them before they bypass OTP-based two-factor authentication.
Here are some tactics to prevent unauthorized access and mitigate risk:
- Use bot detection algorithms: Bot detection services add a layer of security by analyzing traffic patterns and behavioural anomalies to block automated OTP‑harvesting bots.
- Don‘t rely on SMS based authentication: Hackers can co-opt SMS authentication for 2FA bypass. Harden rate limits per device, IP address, and phone number, and use stronger MFA protocols.
- Identify API anomalies: Detecting abnormal API patterns helps look for unusual request rates to prevent API abuse.
- Implement phishing-resistant MFA: The CISA suggests using FIDO/WebAuthn authentication to remain secure against 2FA bypass attacks.
- Add biometrics to security measures: Biometric data, such as fingerprints or facial recognition, can strengthen MFA.
- Encrypt communication channels: Prevent OTP bots from intercepting one-time passwords with encrypted communication channels to secure OTP delivery methods. Hardware tokens and dedicated authenticator apps provide an added layer of security.
- Research dark web trends: Use tools that report on current trends in the cybercrime space to stay ahead of emerging threats that could impact your business.
- Monitor user patterns: Analyzing suspicious user behavior indicates an account takeover before it happens.
- Real-time reporting: Uncover actionable insights with real-time monitoring and reporting to speed up response time.
FAQs
What is an OTP?
A one-time password (OTP) is a single-use security code to verify a user‘s identity when logging in. As a security function, OTPs can be co-opted by hackers when they‘re not delivered within a secure environment.
What are OTP bots?
OTP bots are automated tools used by hackers to bypass two-factor authentication protocols. OTP bots intercept temporary codes sent via SMS, email, or authenticator apps.
These services help attackers gain access to legitimate accounts after they‘ve obtained the user‘s username and password.
How do OTP bots work?
Hackers can choose from a variety of different OTP bots to compromise an account. Some bots automatically send OTPs via SMS messages or email, while others send fake voice messages to phish the OTP.
Automating the social engineering process makes OTP attacks efficient for the hacker, making it more difficult for the organization to catch and stop attacks.
What are the different types of OTP bots on the market?
There is a range of OTP bots on the dark web that fulfill different functions.
Here are some of the most popular OTP bots:
- SMS interceptor bots: These bots exploit weaknesses within mobile networks to intercept OTP SMS messages. Mobile networks rely on SS7 protocols that contain unpatched vulnerabilities, resulting in a lack of proper SMS encryption. Bots then transfer the message containing the OTP to the attacker within seconds.
- Phishing bots: Attackers use these bots to automate phishing attacks, sending large volumes of malicious malware-laden emails and messages to trick the user into handing over sensitive information.
- Voice call bots: Hackers use bots to send automated phishing voice calls to impersonate service providers like customer support. User unknowingly hand over their OTPs to the attacker, losing access to their account.
- Social engineering bots: A form of MFA bombing, hackers use social engineering bots to bypass 2FA. The bot sends the user a request to secure their account, unknowingly handing over their one-time password to the attacker.
- SIM swapping bots: Adversaries use these bots to automate SIM card transfers to gain control of the user‘s phone number and intercept OTPs. The hacker tricks the mobile service provider into switching the user‘s phone number to the adversary‘s SIM card.
What is 2FA?
Two-factor authentication (2FA) uses only two authentication factors to verify the account user, such as biometric data (fingerprints and face scans), SMS codes, and hardware tokens.
In recent years, 2FA bypass has become easier due to OTP bots.
How is 2FA vulnerable to OTP bot attacks?
2FA isn‘t secure against OTP bots, which are designed to target vulnerabilities in the authentication chain. Once an attacker has access to the one-time password, they can quickly bypass 2FA authentication methods and take over the account.
What is MFA?
Multi-factor authentication (MFA) involves more than two authentication methods. For MFA bypass, a stolen password or OTP isn‘t enough for an attacker to break through.
Adding a barrier for friction for the attacker results in less OTP bypass than relying on 2FA alone.
OTP bot scams to watch out for
Be cautious about sudden calls from customer support or your bank—it could be an OTP bot scam!
- Never share your OTP with anyone, even if they seem legitimate.
- Don‘t click on redirect links within emails or SMS; instead, navigate to the page yourself to log in.
- Hang up on phone calls asking for your OTP, and call back the service provider with a number from their official website.
Secure your credentials with CybelAngel
The rise of account security threats is troubling. Hackers are becoming more sophisticated, launching attacks within seconds.
Organizations need to strengthen their account takeover defenses to protect credentials from being leaked on the dark web—balancing security with user experience.
CybelAngel helps you protect credentials from being stolen by malware and alerts you to leaked credentials.

