Our Investigation of the Oracle Cloud Data Leak [Flash Report]

Table of contents
In mid March a threat actor posted on Breachforums, asserting a successful breach of Oracle’s systems. CybelAngel has received information from a threat intelligence source that confirms Oracle has admitted to a security incident involving their Gen 1 servers, and has started to notify customers.
What has been happening at Oracle?
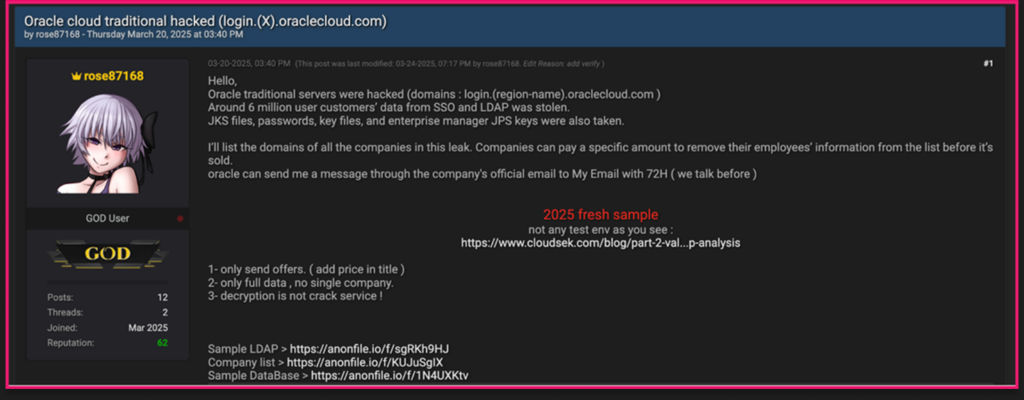
Oracle has reportedly acknowledged a security incident involving unauthorized access to its cloud infrastructure to select clients. On March 20, 2025, a threat actor posted on Breachforums, asserting a successful breach of Oracle’s systems. The stolen data, including a cache of 6 million data records, were subsequently offered for sale, accompanied by ransom demands and proposals for the trade of zero-day exploits.
In the days that followed, the actor provided additional information, proof, and samples, further strengthening their credibility within the cybersecurity underground community.
An outline of the Oracle breach prior to April 1st
- The compromised data, according to Oracle, was approximately 16 months old and did not include complete Personally Identifiable Information (PII).
- Exposed data included email addresses, usernames, and hashed passwords.
- Instead of solely seeking financial payment, the attacker is willing to exchange stolen data for zero-day exploits, indicating a broader cybercriminal agenda.
- The stolen data includes: SSO (Single Sign-On) and LDAP credentials JKS files (Java Key Store) Passwords and key files Enterprise Manager JPS keys
- Oracle reportedly has taken proactive security measures to mitigate further risks.
Oracle has officially denied that their organization the company’s Oracle Cloud federated SSO login servers had been breached. They stated to Bleeping Computer in mid-March that, “There has been no breach of Oracle Cloud. The published credentials are not for the Oracle Cloud. No Oracle Cloud customers experienced a breach or lost any data.”
Additional exposure details that CybelAngel has learned about this breach [April 1st]
CybelAngel has received information from a threat intelligence source that reports Oracle has communicated to stakeholders regarding a security incident involving their Gen 1 servers. Our source, who we are not naming as requested, is reporting that Oracle has allegedly determined an attacker who was in the shared identity service as early as January 2025.
This exposure was facilitated via a 2020 Java exploit and the hacker was able to install a webshell along with malware. The malware specifically targeted the Oracle IDM database and was able to exfil data. Oracle allegedly became aware of a potential breach in late February and investigated this issue internally.
Within days, Oracle reportedly was able to remove the actor when the first demand for ransom was made in early March. Before this was made public by the attacker, Oracle reportedly took measures to contain the breach and reinforce security around the affected servers.
Information CybelAngel has received claims the Gen 1 servers impacted have no connection with their Gen 2 servers. No complete PII has been exposed and is at least 16 months old.
The sensitive data exposed contains user emails, hashed passwords, and usernames.
A threat actor profile: Who is rose87168?
“rose87168” the threat actor behind these data breach initiatives, is a little know cyber threat player.
The actor, “rose87168” appears to be a relatively new threat actor, given their account creation date on March 5th, 2025. They have low activity suggesting they might still be building their presence.
fresh sample.
Their primary motive appears to be financial gain, possibly targeting individuals or organizations for data theft or financial exploitation.
The requested ransom is a payment of 20 million USD.
The hacker has also stated on Breachforums that they are also willing to exchange stolen data for zero-day exploits, indicating a broader cybercriminal agenda.
Please note that Oracle is reportedly also involved in investigating an unrelated breach involving health data.

