Smishing,Phishing, and Vishing [Everything You Need to Know]

Table of contents
- The main differences: Smishing, phishing, and vishing
- What is phishing?
- What is spear phishing?
- How spear phishing targets financial institutions
- What is smishing?
- What is vishing?
- What is AI vishing?
- Why fraudsters target your executive team?
- Smishing scams vs phishing emails vs vishing attacks: How do they compare?
- 6 key biases that social engineering attack scams exploit
- Final thoughts
Smishing, (aka SMS phishing), phishing (email phishing), and Vishing (manipulative phone calls) are scams beloved of cybercriminals.
But today’s cybercriminals are casting a wider net with more sophisticated smishing attacks that set out to snare you.
In this blog post, you’ll learn how to differentiate between these three threats and learn about trending scams and malware.
Let’s dive into these malicious scams.
The main differences: Smishing, phishing, and vishing
The first thing you need to do is to learn and educate your team about these common cyber attacks.

Here are the main differences:
- Phishing: You’ll receive deceptive messages, emails, and fake websites crafted to swipe your personal details.
- Vishing: You’ll receive manipulative phone calls aimed at collecting your personal data.
- Smishing: You’ll receive text messages skillfully designed to extract your sensitive data.
What is phishing?
Phishing is a classic cyber attack that follows a classic pattern: A hacker attempts to trick individuals into revealing sensitive information or installing malware by masquerading as a legitimate company.
This can take the form of fraudulent phishing emails, SMS texts and phone calls that appear to come from reputable sources like banks, companies, or government agencies.
The goal is to lure victims into performing actions that benefit the attacker, such as clicking malicious links, opening attachments with malware, or divulging login credentials, financial information, or other sensitive data.
What is spear phishing?
Spear Phishing, also known as tailored phishing, sets itself apart from the more widespread strategy of mass phishing, through its personalized approach.
A spear-phishing e-mail is far more dangerous form of phishing. person’s name and is sent only to people who are known to be customers of a certain business, greatly increasing the likelihood that the targets will be duped.
Before launching an attack, spear phishers gather detailed information about their intended victims or select a particular individual as their target.
What do Twitter and Sony employees have in common with British MPs?
Well, they’ve all been targeted by this type of phishing attack.
How spear phishing targets financial institutions
Usually, hackers initiate contact with victims through a request or query, seeking to prompt a reply that begins a seemingly legitimate company-to-company communication trail.
For example, the finance team receive an email that impersonates a company’s service provider, with an attached invoice that announces the company’s new financial information. Critically, it seems authentic. Key financial details such as the current provider and key contact are included, to make this update seem normal.
Often spear phishing emails create a subtle sense of urgency, by offering an “early payment discount” for settling the invoice within an expedited time frame, aiming to build trust. This sets the stage for subsequent fraudulent activities, such as soliciting unauthorized wire transfers
What is smishing?
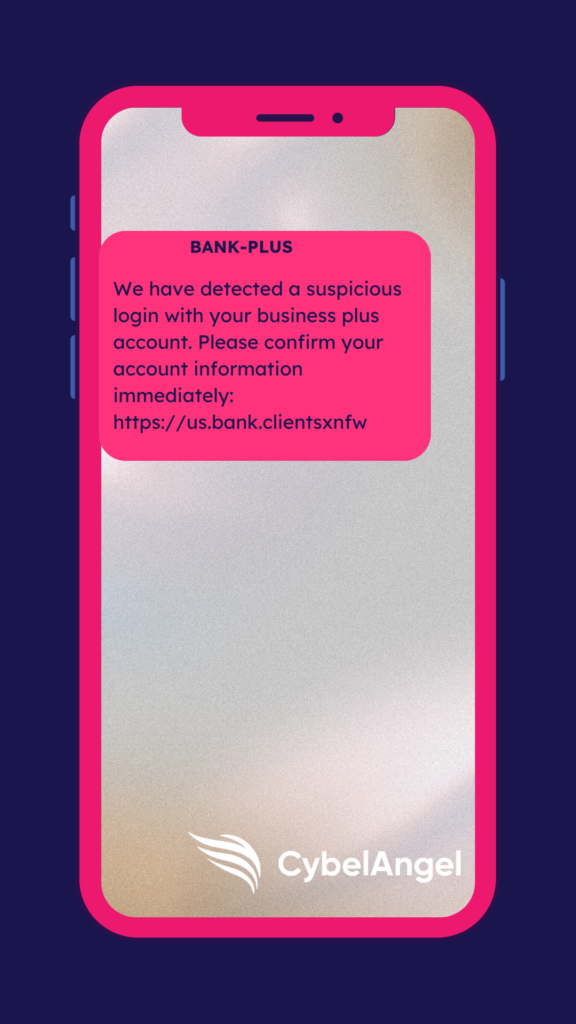
Smishing is a type of attack conducted via text message (SMS), derived from a combination of “SMS” and “phishing.” Similar to phishing, smishing involves sending the victim an unsolicited sms message that prompts them to divulge information by following a malicious link, calling or answering phone calls , or texting back.
It follows the class social engineering attack pattern, to exploit emotions like fear or a sense of urgency to spur the recipient to react and respond quickly.
Though it relies on the same principles as traditional phishing, smishing tends to be more effective due to several factors:
- Most smartphones don’t have an auto “spam” folder
- Limited awareness about smishing across certain demographics
- Greater trust in SMS compared to email
- Challenges in authenticating the identity of these hackers
What is vishing?
Vishing is typically defined as a type of social engineering attack that uses voice calls, voicemails, or voice messages to trick victims into revealing sensitive personal or financial information.
This attack method uses phone calls or voicemails to deceive people into divulging sensitive data like financial information, social security numbers, credit card numbers, and other passwords. Attackers often impersonate trusted entities like banks or government agencies.
With the proliferation of AI, vishing is set to be a huge cybersecurity headache for businesses and executives alike.
AI vishing is incredibly effective at identity theft.
What is AI vishing?
AI-enhanced vishing attacks are a rising threat.
These scams harvest voice samples from public recordings found online typically on social media. Scammers then accurately recreate and manipulate voices to convincingly impersonate family members or acquaintances.
Why fraudsters target your executive team?
These scammers utilize voice samples obtained from public recordings or social media to produce highly convincing imitations of familiar voices.
By manipulating these sounds, they can effectively impersonate family members or acquaintances, thus tricking individuals into divulging sensitive data like personal financial information.
In a disturbing case of deep fake fraud, UK engineering giant Arup was swindled out of $25 million after scammers created an AI-generated video impersonating the company’s CFO during a video call.
High-level executives, who are no strangers to sensitive data, like critical corporate intel and financial assets, find themselves at significant risk, from many angles.
Given their authority to make substantial financial transactions and access to critical data, they are prime targets for cybercriminals aiming for monetary gain or corporate espionage.
The implications of a successful attack on such individuals are far-reaching. Implementing robust security measures, should include:
- Incorporating multi-factor authentication (MFA) as part of all login credentials
- Educating your team on the risks of business email compromise (BEC)
- Sharing emerging spear phishing trends with executives
Let’s take a look at what these phishing attempts have in common.
Smishing scams vs phishing emails vs vishing attacks: How do they compare?
They are all forms of social engineering attacks that prey upon human error and judgement.
The main thing to keep in mind is that social engineering stands as a potent technique of psychological manipulation. It is designed to provoke specific actions from the target to compromise private information, using malicious software.
If you feel a twinge and something feels off, you are more than likely right.
But sometimes, especially with the plethora of social media data that exists online, that is really not the case for most victims.
Scammers know how to leverage your inherent cognitive biases and coupled with social media intel about your life, they leverage shortcuts for finding your weak points.
Though we rely on these biases for efficiency, human nature makes them exploitable. The wrong decision can then jeopardize sensitive information.
So, what are are some clear biases to watch out for?
6 key biases that social engineering attack scams exploit
Hackers are often armed with solid intel about their targets. You’ll need to be just as au fait with how they leverage phishing scams.
Here is an essential list to share with your team.
1: Authority: Attackers will impersonate someone in a position of power, such as a police officer or a government agency, to demand private information. This could extend to voice calls, where the attacker poses as a legitimate authority figure asking for sensitive information.
2: Intimidation: By threatening negative consequences, attackers coerce victims into handing over personal details, creating a high-pressure situation that demands immediate action.
3: Consensus: You are more likely to divulge personal information if you believe others have done the same. A fraudster tactic will suggest, that “many have already updated their financial information,” pressuring you to act in kind.
4: Scarcity: The creation of a false scarcity can spur you into action out of fear of missing out. An example might be a smishing message to confirm your company’s bank account information to avoid service disruption.
5: Urgency: This method pushes you to respond within a 24-hour window. This is often linked to a query regarding a credit card issue. You feel ruffled and pressed to respond.
6: Familiarity: Hackers may impersonate a family member or friend. They often ask for your help through a messaging app or via an unknown phone number provided in a misleading way.
Overall, educating your wider team about these subtle manipulation tactics is crucial.
Social engineering attacks work for a reason.
But understand the above will help you and your team to safeguard critical sensitive information from unauthorized access. This is so important when our mobile devices are central hubs for our personal and financial information.
Final thoughts
If you’re trying to educate your team around you about smishing, phishing, and vishing malware, this blog will be enough to provide some good context. However, as scammers grow more elaborate, cybersecurity tools, like external attack surface management solutions are worth your consideration.
EASM tools, like CybelAngel’s allow you to comprehensively monitor and prevent digital threats outside of your IT perimeter.
Looking to learn more about more emerging threats? Read our The Dangers of PII Leaks: 7 Key Insights guide.

