7 Ways to Protect Your Brand from Impersonation in 2026

Table of contents
What do you do when traditional trademarks and copyrights don‘t cut it anymore?
Brand protection strategies are becoming essential to preventing brand abuse by malicious actors. Counterfeit products and brand impersonation aren‘t just a marketing problem anymore—it‘s a cybersecurity risk that can lead to major financial losses and reputational damage.
“Criminals are always willing to use all possible ways to get access to value, much of which is contained in the cyber infrastructure. Consequently, to stay ahead, those of us who defend must use every tool at our disposal – which now includes agentic AI.” Arvind Krishna, Chief Executive Officer, IBM.
In this 2026 guide, you‘ll discover how effective brand protection can stop bad actors from collecting and selling customer data, prevent trademark infringement, and even increase your brand‘s value.
Brand abuse in 2026
These days, brand abuse is a form of sophisticated identity theft. Hackers can use AI-powered tools to craft lookalike domains to lure customers, gather their data, and resell it on the dark web.
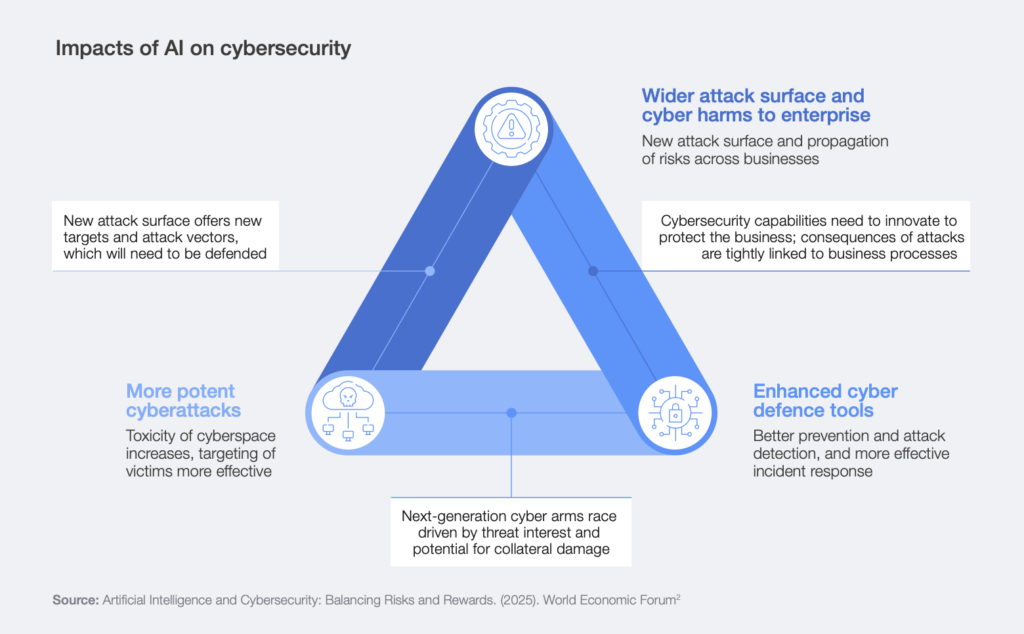
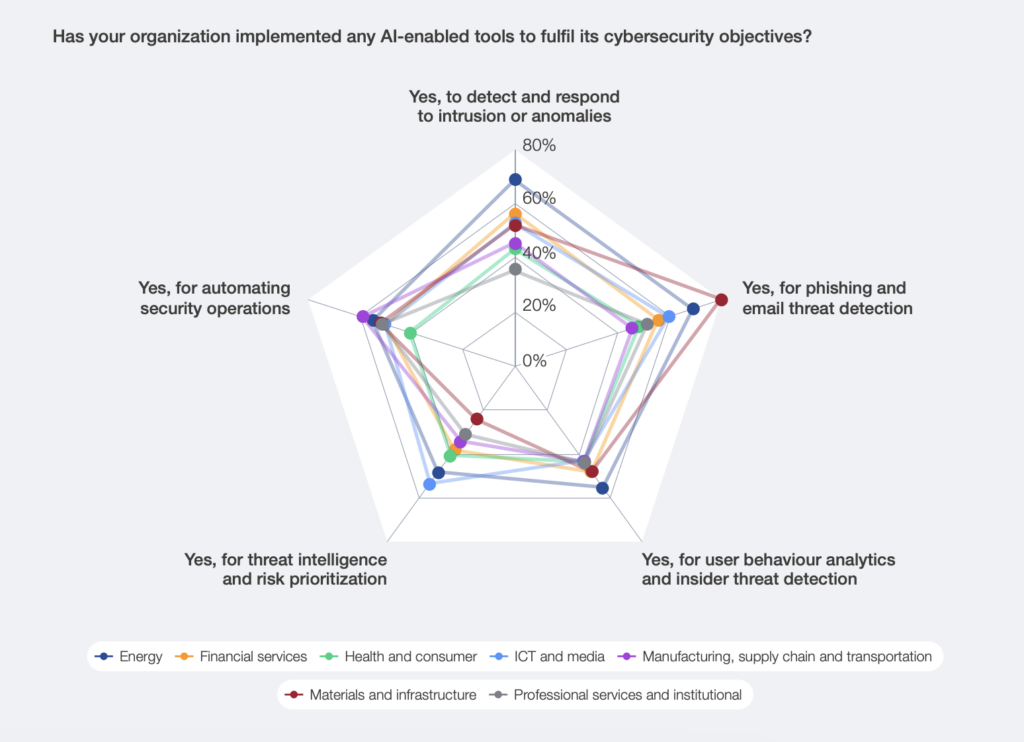
According to a survey from the World Economic Forum (WEF), AI-powered threats pose a significant risk to both brands and customers:
- 77% of those surveyed found that cyber-enabled phishing and fraud have increased in the past year.
- 79% of respondents in North America reported exposure to digital scams.
- 52% of brands have implemented AI for phishing and email threat detection.

Figure 1. A diagram showing how AI creates cybersecurity risks. Source: World Economic Forum (WEF)
As regulations and law enforcement struggle to keep up, brands need to take proactive action before bad actors can wreak havoc.
What are the most common types of brand abuse and impersonation attacks?
In 2026, scams have evolved using automation and AI in online marketplaces. Attackers are deploying clusters of fake accounts connected to phishing pages that cause real damage.
Let‘s take a look at some real-world examples of brand impersonation attacks that eroded customer trust.
1. Domain squatting and typosquatting
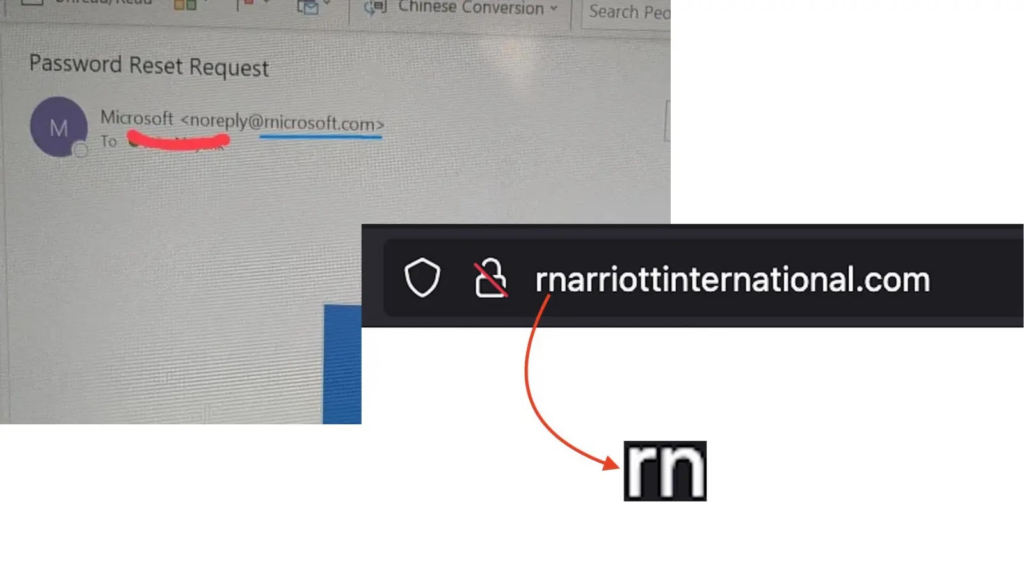
To trick customers into clicking, hackers register domains that appear legitimate but have slight misspellings.
2. AI‑generated cloned domains
Using generative AI, bad actors can scrape and clone your website‘s UI and brand voice within minutes.
3. Fake social media profiles
Scammers can use AI-powered tools to scrape a brand‘s legitimate social media profile and create a new account, preying on customer loyalty.
4. Social engineering and phishing accounts
Hackers craft emails, SMS messages, or social media accounts to phish for customer information, reselling these later on the dark web.
5. Sponsored scam campaigns
Bad actors run paid ads on social media using brand names that redirect to fraudulent phishing sites or counterfeit merchandise.

6. Counterfeit products
Scammers create listings on e-commerce platforms like Amazon that mimic legitimate brand storefronts and genuine products. These fake goods either don‘t actually exist or are of a far inferior quality.
Why you need brand protection in 2026
A comprehensive brand protection strategy stops unauthorized sellers from exploiting your brand and infringing on intellectual property rights.
You need brand protection to avoid:
- Revenue loss: Fake storefronts siphon off profits from brands, reducing the overall effectiveness of marketing campaigns.
- Loss of consumer trust: Scams erode customer trust in the legitimate brand, pushing them towards competitors.
- Reputational damage: Unauthorized use of a brand‘s image makes the brand itself appear unsafe or careless.
- Compliance risks: If brands don‘t do enough to protect customers‘ data from being stolen, they may incur regulatory fines or be forced to prove they took adequate measures.
- Increased operational costs: Investigating incidents and working with law enforcement can chew up resources and budget.
Monitoring for brand abuse across the surface, deep, and dark web
1. Surface web monitoring
Start with the top-most layer of your attack surface. The surface web includes public websites, social platforms, e-commerce marketplaces, and search engines.
To thwart these attempts, brands need to:
- Set up monitoring tools that scan for fake websites that use your brand name, logo use, and other trademarked material.
- Monitor for suspicious patterns in real-time to detect new top-level domains (TLDs) that contain your brand name.
- Implement social media impersonation detection tools that analyze profile behavior patterns.
- Run scanners across e-commerce marketplaces to catch counterfeit listings.
- Utilize AI models that can visually or textually detect similar assets being used.
2. Deep web monitoring
The second layer is the deep web, the part of the internet that isn‘t indexed by search engines. This includes paywall content, login portals, or areas with restricted access.
To protect your brand on the deep web, it‘s important to:
- Monitor paste sites and data leak repositories to find leaked credentials before they harm the brand‘s reputation.
- Automate alerts for brand-related keywords to catch planning efforts before scammers deploy harmful campaigns.
- Deploy crawlers to scan private forums to locate online chatter before scammers utilize tools like phishing kits.
- Develop partnerships with e-commerce platforms like Amazon to ensure counterfeiters are stopped before fake products circulate.
- Map coordinated fraud rings to better understand potential cybercriminal gangs that may be targeting your brand.
3. Dark web monitoring
The last layer of your attack surface is the dark web. At this stage, criminal marketplaces trade malicious assets like fake storefronts and phishing kits to infringe on a brand‘s intellectual property.
Dark web brand protection should include:
- Continuous dark web monitoring helps identify emerging impersonation campaigns by flagging stolen materials and keywords.
- Automate takedowns of fake assets across apps to shorten the lifecycle of stolen assets and prevent their spread.
- Detect credential leaks before they are circulated and traded.
- Harden assets against cloning by using dynamic security elements and watermarking to make it harder for attackers to replicate your brand.
- Automate reports for law enforcement to streamline regulatory compliance and alert authorities to large‑scale fraud operations.
What to do when you discover your brand has been impersonated
When uncovering an impersonation campaign against your brand, it‘s important to act fast.
Having a prepared incident response plan ensures a structured, coordinated approach that protects customer trust and limits reputational damage.
Here are some practical tips you can apply to your brand protection strategy:
1. Validate the threat and triage it
Monitoring tools can help validate the threat against your brand to determine if it‘s high-risk for triaging up the chain.
It‘s useful to consider:
- Is the asset using your brand name, logo, or identity? Look for the use of similar UI to your brand website, reuse of keywords, and logo replication.
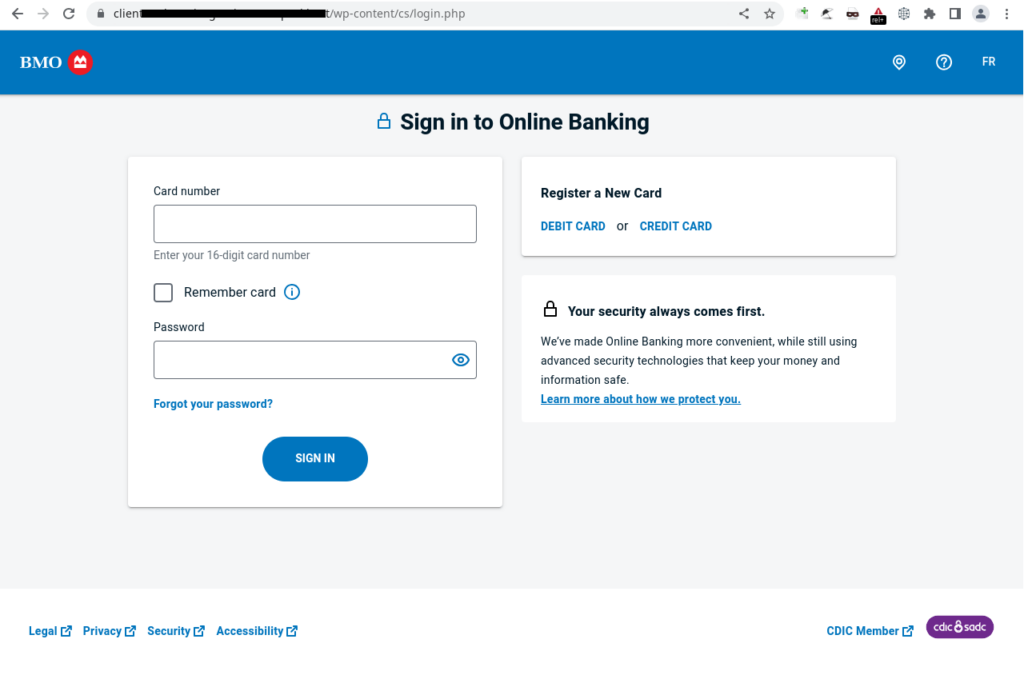
- Is it pretending to be an official channel? Fake customer support accounts, cloned login pages, or fraudulent ads are tell-tale signs of impersonation.
- Is it targeting your customers or employees? Hackers target your loyal customers with phishing emails using similar email addresses, fake promotional discounts, or scam storefronts on social media platforms and e-commerce sites.
- Is it part of a known impersonation pattern? Cybercriminals create similar domains with AI-powered tools or reuse brand templates found in online communities.
2. Contain the threats
Once you‘ve determined any high-risk threats, it‘s time to contain the threats by implementing strong brand protection solutions:
- Block malicious domains and URLs at the network and email gateway level.
- Notify internal teams, including cybersecurity teams, communications and marketing, and customer support, to remain vigilant.
- Warn supply chain partnerships or distributors if they may be impacted.
- Use monitoring tools to scan for clustered attacker infrastructure like proxy chains, lookalike domains, VPNs, and phishing sites.
3. Investigate impersonation threats
Use the tools at your disposal to take down impersonation threats and shut down cybercriminal operations exploiting your brand:
- Collect and preserve evidence, including screenshots of impersonation, recording URLs and domain registration information, fake social media profile links, copies of phishing emails, and customer complaints reporting scams.
- Analyze the assets by checking WHOIS data, inspecting SSL certificates, locating the hosting providers and IP addresses, identifying redirected pages, and inspecting spoofed domains or forged authentication.
- Map threat infrastructure by looking for domains registered to the same bad actor, shared hosting and IP addresses, reused phishing templates, connected social media accounts, and overlapping email infrastructure.
- Scan for activity on the dark web to catch mentions of your brand in forums, phishing kits using your brand assets, credential dumps, and bundled lookalike domains being sold.
- Determine legal actions to facilitate takedowns, legal escalation, and reporting to law enforcement.
4. Clean up attacker infrastructure
Take control back from scammers by removing the tools they use to scam victims:
- Remove fake domains and websites, such as filing takedown requests with domain registrars to cut off hackers at the source.
- Take down fraudulent social media profiles by reporting abuse to platforms so fake accounts can‘t continue to cause damage.
- Disable hosting and server infrastructure via IP and DNS reports, blocking IP ranges, and requesting suspension of hosting services to bad actors.
- Remove phishing kits and cloned assets by initiating takedown requests and reporting malicious servers.
- Flag malicious email addresses and messaging accounts with the platform provider to stop attackers from communicating with potential victims.
- Clean up malicious SEO results by requesting their removal from search engines by citing copyright infringement.
5. Strengthen defenses
Ensure your cyber infrastructure can stand up to vulnerabilities and threats:
- Harden your digital assets by securing websites, email infrastructure, and authentication systems to make them more resistant to spoofing.
- Continuously monitor domains and social media platforms to detect lookalike sites, fake accounts, and emerging impersonation attempts.
- Protect employee and customer credentials by enforcing multi-factor authentication (MFA) for all employees and retain customer data on secure servers.
- Strengthen brand assets by keeping important brand assets in offline servers and not in any repositories that could be compromised by bad actors.
- Integrate threat intelligence tools to scan for fraud and reinforce greater anti-counterfeiting defenses.
- Educate customers on known scams so they can recognize fraudulent messages, avoid malicious links, and verify legitimate goods.
- Conduct regular brand and security audits to uncover vulnerabilities to protect your most valuable assets.
6. Communicate with customers and stakeholders
Restore trust and transparency with your customers and ensure stakeholders are onside:
- Communicate impersonation incidents to customers to avoid backlash and prevent confusion.
- Educate customers on what to look for so they can avoid scams using the same templates.
- Post scam alerts to social media to take control back from scammers and promote awareness.
- Inform internal stakeholders across departments to get everyone on the same page and coordinate responses.
- Share resolution results to close the loop with customers and stakeholders and reinforce trust.
7. Collate reporting data for law enforcement
Take further legal action to stop targeted scams for good:
- Document evidence from the investigation phase and format it to pass on to law enforcement.
- Report on scam infrastructure by outlining the domains, hosting services, social accounts, and communication channels used to operate the fraudulent scheme.
- Show evidence of criminal intent by highlighting actions such as credential harvesting, payment requests, malware delivery, or deceptive messaging designed to mislead victims.
- Communicate the impact on victims by summarizing how individuals or customers were affected, including financial loss, data exposure, or reputational harm.
FAQs
Brand protection is the act of taking back your brand from scammers and bad actors across the internet. It‘s the process of taking actions to prevent unauthorized use of your intellectual property (IP) and brand name.
To protect your brand‘s reputation and financials in 2026, companies must:
Deploy continuous monitoring tools across domains, social media, ads, and marketplaces.
Work with cybersecurity experts to curb brand abuse.
Understand the risks of AI and how AI can be used to thwart scams.
Restore customer trust after impersonation by scammers.
Invest in proper trademark registration for your brand identity, brand names, and logos to protect your brand from unauthorized use.
An effective brand protection strategy includes automation and AI to catch fake products and phishy domains at scale.
You can use AI and automation tools to quickly detect brand impersonation by scanning for your brand‘s keywords, similar logos, and even leaked credentials.
Investing in an online brand protection strategy offers returns both in reducing lost sales due to counterfeit products and understanding the cost of inaction.
Use specific metrics and KPIs, such as the number of threats discovered, the number of domains taken down, the number of customers saved from scams, and the total number of financial losses avoided.
Inaction is costly. It results in a loss of customer trust, financial loss from diverted sales, and costly regulatory fines.
Protect your brand with CybelAngel’s 24/7 brand monitoring and threat intelligence across the surface, deep, and dark web
Counterfeit goods and phishing domains are becoming more common with the rise in AI tools. Cybercriminals can quickly generate thousands of lookalike sites designed to confuse customers, damaging your brand‘s reputation in the process.
CybelAngel‘s Brand Protection platform gives your team the power to take back your brand‘s intellectual property to streamline takedowns and report on fraud schemes.
If you don‘t know where to start, contact our experts to request a demo to see how simple brand protection can be.

