Infostealers: Die Malware, die einbricht, ohne irgendetwas zu zerstören

Inhaltsübersicht
Im Jahr 2026 schlüpfen Cyberkriminelle durch die Lücken von Organisationen, um sensible Daten zu ernten und zu verkaufen. Infostealer, das hinterhältigste Werkzeug im Arsenal eines Angreifers, sind die bevorzugte Waffe, die sich unbemerkt in Bereiche eindringen, in die sie nicht gehören, ohne Sicherheitssysteme zu alarmieren.
IBM berichtete, dass 1 von 3 Vorfällen die im Jahr 2025 beobachtet wurden, beinhalteten den Diebstahl von Anmeldedaten, bei dem Kriminelle “ohne etwas zu zerbrechen eindrangen”. Die neuesten Angriffe erschweren es Cybersicherheitsexperten, einen möglichen Datenverstoß zu erkennen.
Auch Mac-Nutzer sind anfällig für die neue Ära von Infostealer-Malware. Microsoft hat gewarnt dass Cyberkriminelle sich rasant weiterentwickeln und sowohl Windows als auch Mac ins Visier nehmen, um mehr gestohlene Anmeldedaten als je zuvor zu sammeln.
In diesem Leitfaden führen wir Sie durch die neuesten Fortschritte in der Technologie von Infostealer-Malware und was Sie tun können, um Ihr Unternehmen zu schützen.
Was sind Infostahler?
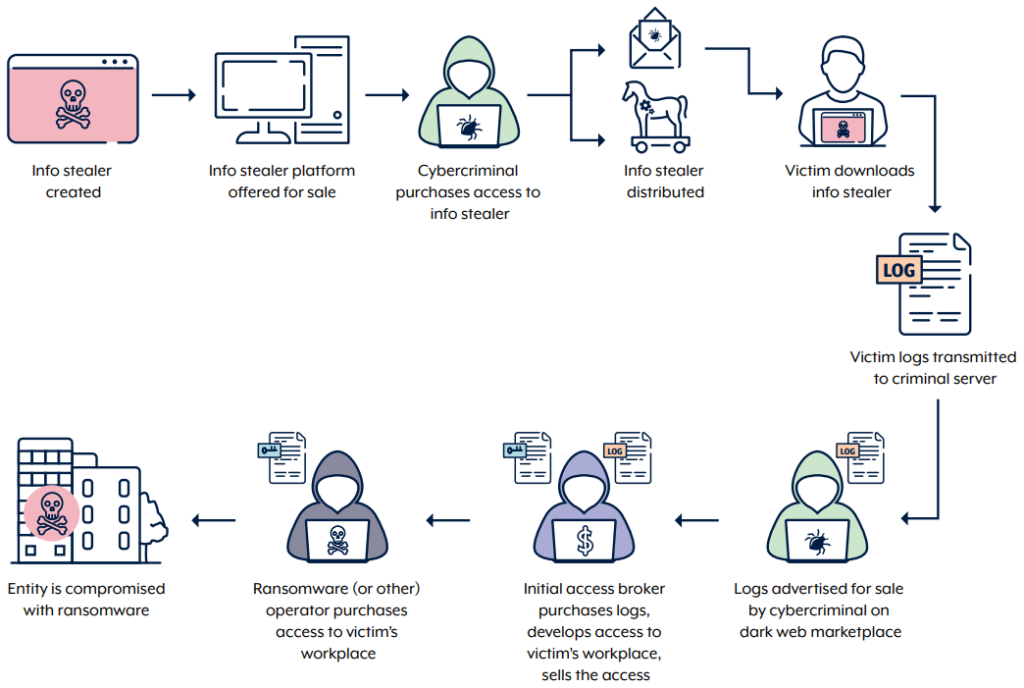
Informationsdiebe sind eine Art von Malware-as-a-Service (MaaS), die sensible Informationen von einem Gerät sammelt.
Cyberkriminelle nutzen Informationsdiebstahl-Malware, um Anmeldedaten zu stehlen, die sie dann auf dem Dark Web weiterverkaufen oder für zukünftige Cyberangriffe wie Phishing-Kampagnen und Ransomware-Angriffe nutzen.
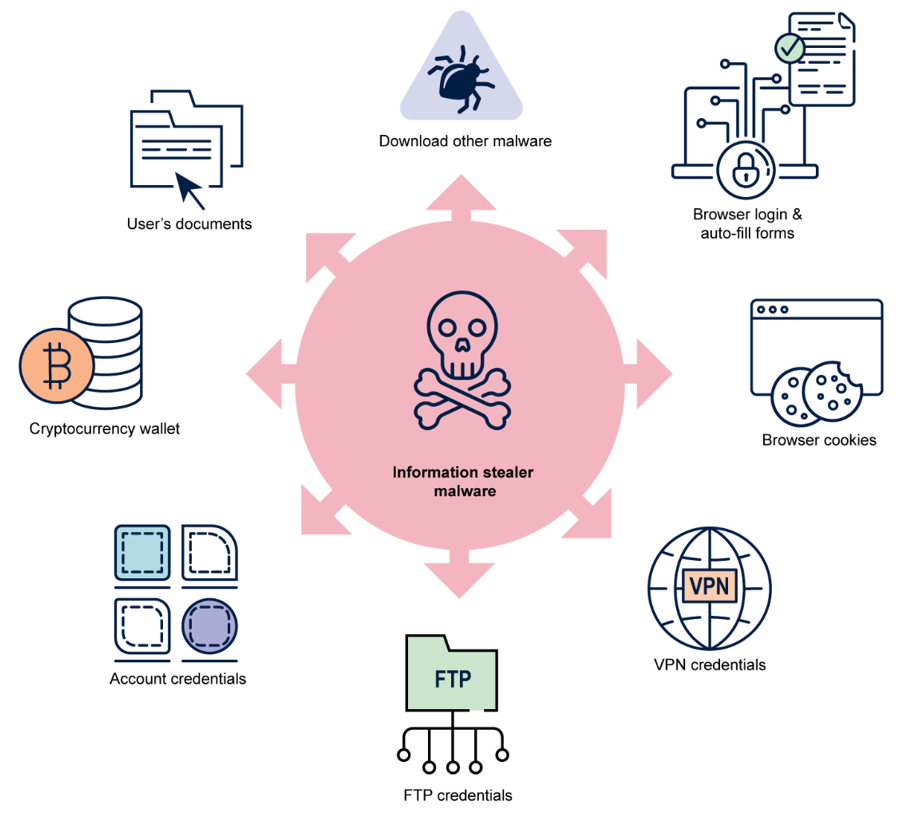
Infostealer tun mehr als nur Anmeldeinformationen zu stehlen; sie stehlen:
- Sitzungs-Cookies und Tokens Konten zu kapern.
- Browserdaten, einschließlich Browserverlauf, Suchverlauf, Autovervollständigungsdaten und gespeicherten Kreditkartendetails.
- Krypto-Wallet-Daten und Krypto-Schlüssel, um Gelder zu stehlen.
- Systeminformationen wie Betriebssystemversionen, installierte Apps und IP-Adressen.
- Bildschirmfotos sensibler Daten.
- Dateien einschließlich PDFs, Dokumenten und E-Mail-Protokollen.
Wie unterscheiden sich Infostealer von anderen Arten von Malware?
Während es viele Arten von Malware gibt, die Bedrohungsakteure nutzen können, gehören Infostealer aufgrund ihrer tarnkappenähnlichen Natur und schnellen Exfiltration zu den beliebtesten.
So unterscheiden sich Infostealer von anderen Arten von Malware:
- Troja kann einem Hacker Fernzugriff und Kontrolle ermöglichen, sind aber komplexer zu bedienen.
- Ransomware können Opfer infizieren und erpressen, aber sie sind nicht leise und nicht von Dauer.
- Keylogger und Spyware kann Eingabedaten aufzeichnen und ansehen, aber es ist nicht gut für die Exfiltration geeignet.
Infostealer gibt es fertig aus den dunklen Ecken des Internets. Abonnementmodelle und Kundensupport für MaaS machen diese Art von Cyberkriminalität zugänglich.
Sobald ein Gerät infiziert ist, können Angreifer in Sekundenschnelle die gewünschten Daten sammeln und verschwinden, ohne dass die Infektion von der Antivirensoftware erkannt wird.
Infostealers im Jahr 2026
Im Jahr 2026 werden Infostealer-Malware-Infektionen immer beliebter, da die Einstiegshürde niedrig und die Benutzeroberfläche einfach zu bedienen ist. Ihre Funktionalität ermöglicht es selbst Hackern auf Einstiegsniveau, gestohlene Anmeldeinformationen für Social-Engineering-Angriffe zu verwenden oder zusätzliche Gelder zu beschaffen, indem Datensätze im Darknet verkauft werden.
- Der Markt für Identitätsdiebstahl boomt im Jahr 2026, angesichts der Nachfrage nach Datensätzen, die gegen Mitarbeiter und Organisationen eingesetzt werden können.
- Ende Januar 2026, Es wurde eine Datenbank mit 149 Millionen Passwörtern entdeckt, zusammen mit 48 Millionen Gmail-E-Mail-Konten und 6,5 Millionen Instagram-Konten.
- Hacker haben es nicht nur auf Geschäfts-Logins abgesehen; sie sind hinter Informationen über Mitarbeiter her, wie deren Social-Media-Konten, Bankkonten, sogar Konten für Streaming-Dienste – jedes kompromittierte Online-Konto, das ihnen mehr Zugang verschaffen kann.
Bedrohungsakteure betreiben Identitätsdiebstahl, um sich schnellen Zugang zu Geldern zu verschaffen, beispielsweise durch das Leeren von Bankkonten und die Eröffnung von Kreditkarten im Namen des Opfers.
Für Unternehmen reicht bereits ein einziger exponierter Mitarbeiter aus, damit ein Hacker Sicherheitsrichtlinien umgehen, finanzielle Unternehmensinformationen sammeln und diese Informationen auf dem Dark Web weiterverkaufen kann, um Profit zu machen.
Vergleichstabelle der wichtigsten Infostealer-Familien (2025 – 2026)
| Familie | Erstmals gesehen / Spitzenära | Primäre Fähigkeiten | Typische Ziele | Notizen (2025–2026) |
|---|---|---|---|---|
| RedLine | ~2020, immer noch dominant | Browser-Anmeldedaten, Cookies, Krypto-Wallets, Systeminformationen | Einzelpersonen, kleine und mittlere Unternehmen, erstmaliger Zugriff für Ransomware | Hohes Volumen auf Stealer-Log-Märkten; immer noch eine der Top-Familien. |
| Waschbär v2 | Wiederaufgetaucht 2023+ | Anmeldeinformationen, Cookies, Autovervollständigung, Krypto, Systeminformationen | Breite Verbraucherbasis, kleine Organisationen | Nach polizeilicher Unterbrechung zurückgekehrt; aktives MaaS im Jahr 2025. |
| Vidar | ~2018, hartnäckig | Anmeldeinformationen, Kekse, Krypto, Systemprofilierung, Dateien | Gamer, Piraterie-Ökosysteme, Verbraucher | Häufig mit urheberrechtlich geschützter Software und Malvertising gebündelt. |
| Lumma (LummaC2) | 2022+, ansteigend | Anmeldeinformationen, Cookies, Krypto, 2FA-Daten, Systeminformationen | Geschäftskonten & Privatkonten | Sehr schnelle Entwicklung; starker Fokus auf Session-Tokens. |
| RisePro | ~2022 | Anmeldeinformationen, Cookies, Krypto, Systeminformationen | Globale Kundenbasis | Häufig in Stealer-Log-Shops; oft mit Loadern gekoppelt. |
| Rhadamanthys | 2022+ | Anmeldeinformationen, Cookies, Kryptografie, Systeminformationen, Dateien | Höherwertige Unternehmens- und Finanzziele | Fortgeschrittenes Panel, starke Verschleierung, aktives MaaS. |
| MetaStealer | 2023+ | Browserdaten, Anmeldedaten, Cookies | macOS-Benutzer, Kreative, kleine Studios | Bemerkenswert für den Fokus auf macOS und Täuschungsmanöver mit falschen Arbeitsangeboten. |
| Stealc | 2023+ | Anmeldeinformationen, Cookies, Krypto, Systeminformationen | Broad, often via malvertising | “All‑in‑one” stealer, frequently rotated in campaigns. |
Welches sind die aktivsten Infostealer-Familien im Jahr 2026?
In the last 2 years, IBM noted that Lumma Stealer, RisePro, and RedLine Stealer were among the top 5 infostealers used by threat actors.
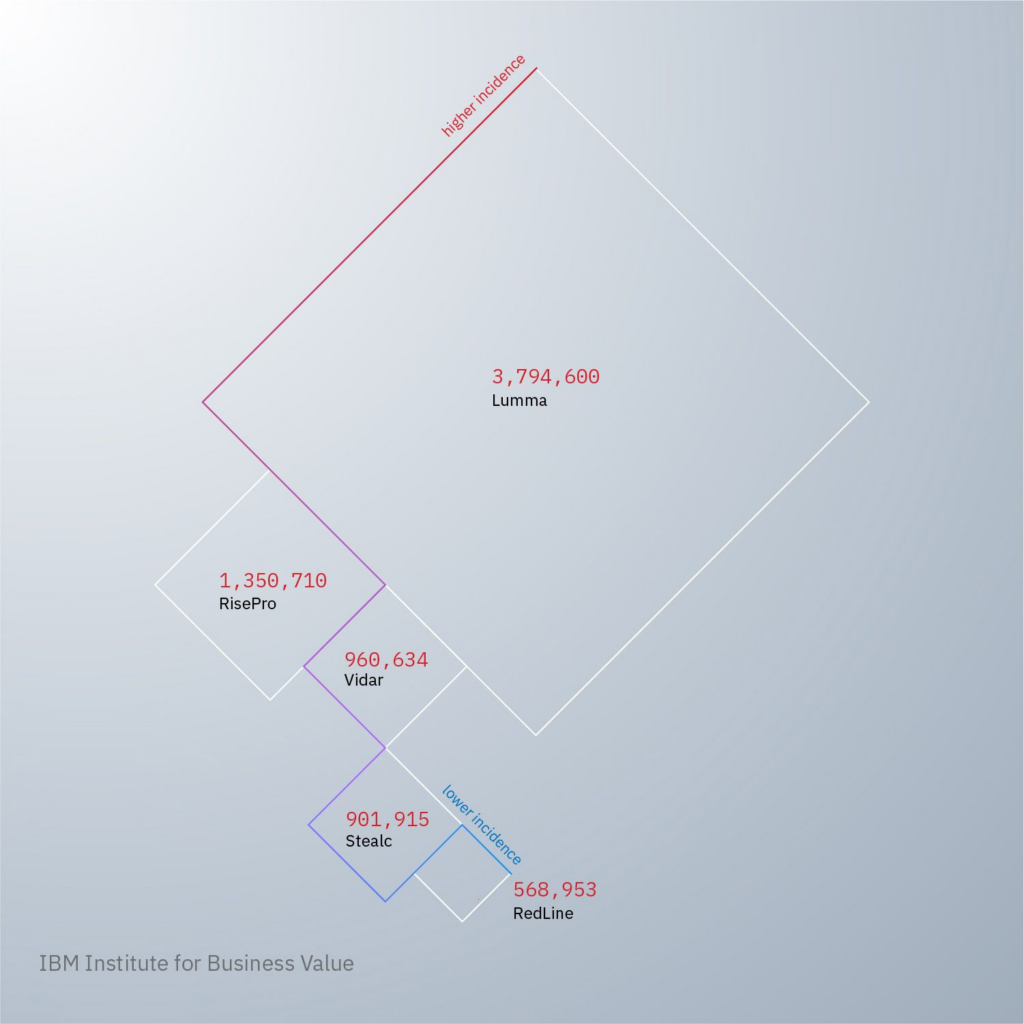
IBM dark web investigations revealed infostealer malvertising increased by 12% in 2024, making them a more prolific threat to businesses.
Here are some examples of how infostealers work.
1. RedLine Stealer
Available on the dark web as a Malware-as-a-Service (MaaS), RedLine Stealer grabs login credentials, autocomplete fields, passwords, and credit card information from browsers. It can also exfiltrate data on the user‘s OS, hardware configuration, location, and any installed security software.
Vertrieb: RedLine Stealer is often shared in malicious attachments sent via phishing emails. As a Trojan, RedLine is also embedded into malicious software that appears to be legitimate.
2. Waschbär-Dieb
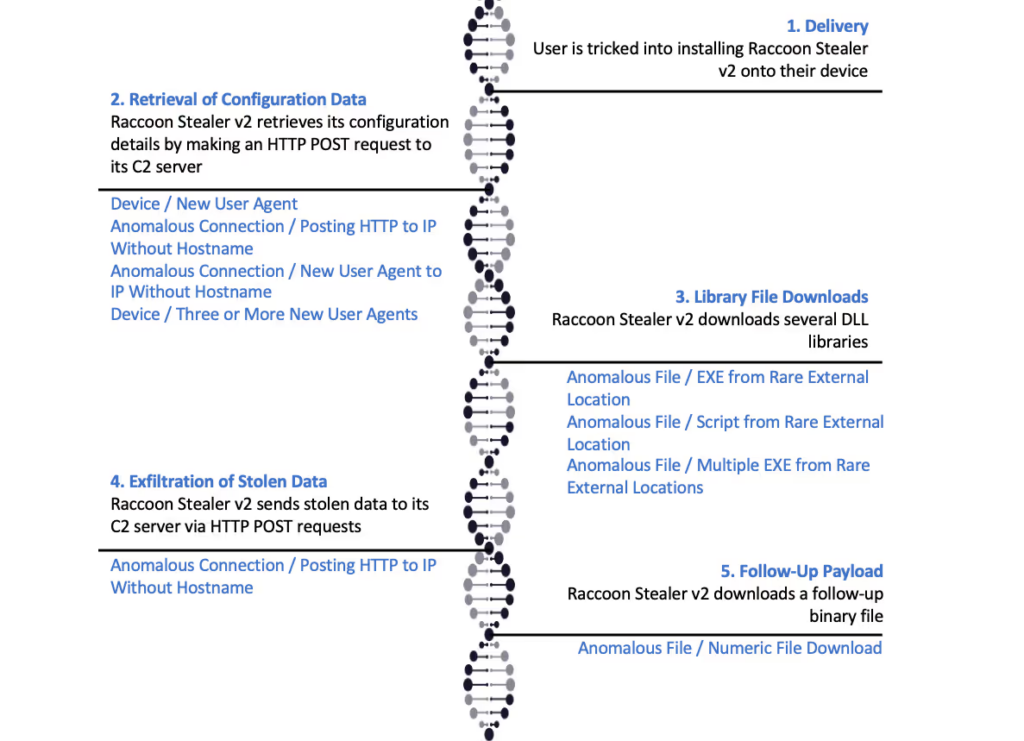
Raccoon Stealer v2 is an infostealer specializing in stealing sensitive data stored in users‘ browsers, specifically session cookies, saved login details, and credit card details.
For cryptocurrency wallets, Raccoon Stealer targets public keys, private keys, and seed phrases to compromise accounts.
Vertrieb: Raccoon Stealer is usually promoted through SEO-poisoned websites that offer “free” or cracked software.
3. Lumma Stealer
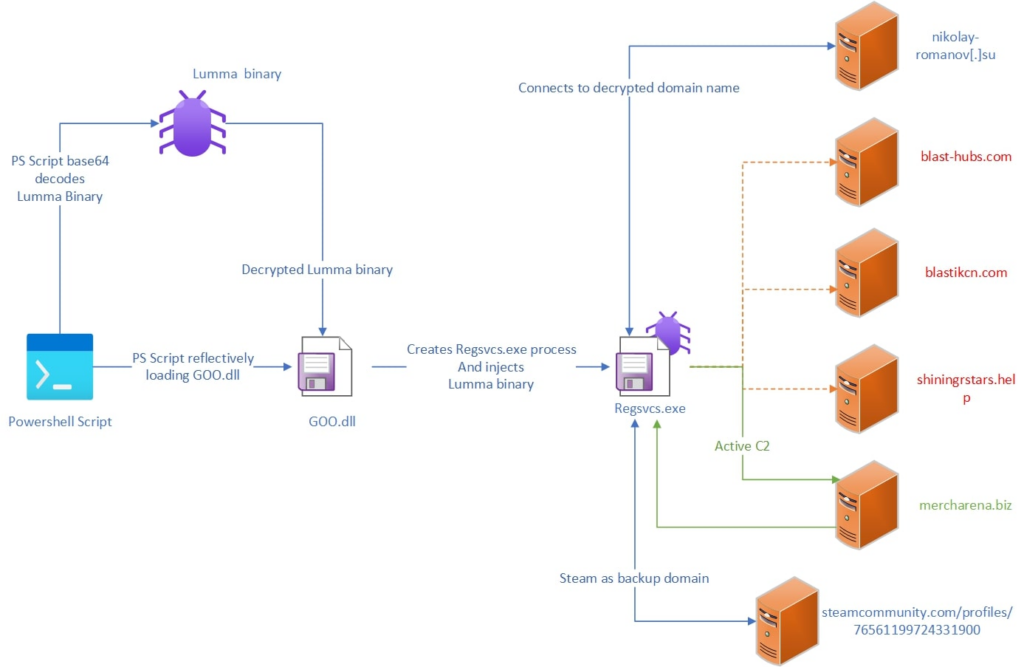
Lumma Stealer has continued to rise in popularity amongst cybercriminals. Lumma specializes in credential and token theft, allowing attackers to bypass multi-factor authentication (MFA) to hijack accounts. Even VPNs can be compromised by collecting the session tokens and configuration files.
Vertrieb: Lumma Stealer is usually distributed on the dark web and sold as a subscription. Using obfuscated PowerShell scripts, threat actors drop the malware into the victim‘s environment to steal data undetected.
4. Vidar-Dieb
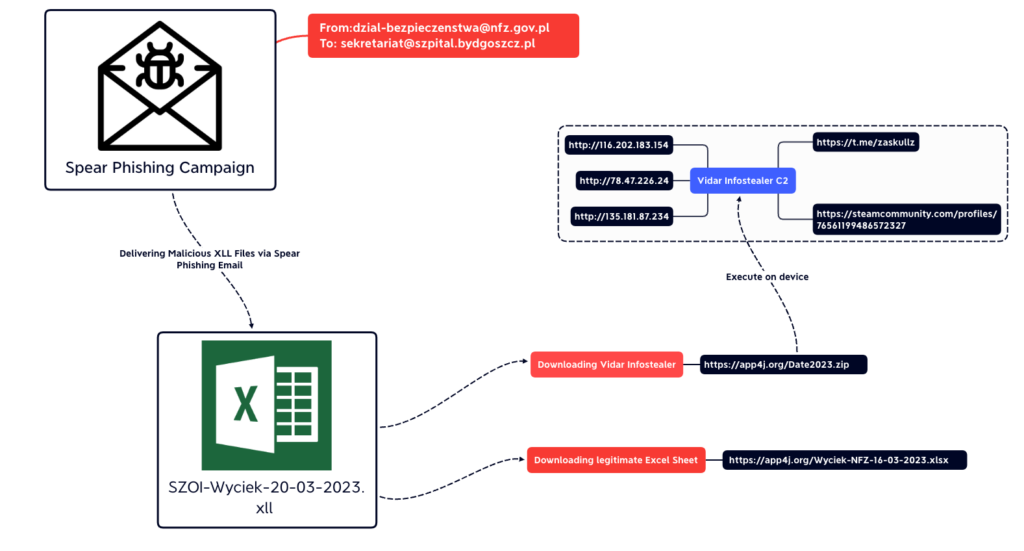
Vidar Stealer focuses on credential theft, stealing browser passwords, cookies, autofill data, crypto‑wallet information, and detailed system fingerprints.
Vertrieb: Methods to distribute Vidar have evolved from malicious email attachments and malvertising campaigns to a MaaS subscription model sold on the dark web. In some cases, Vidar has mimicked legitimate software updates, secretly embedding the malware.
5. RisePro Stealer
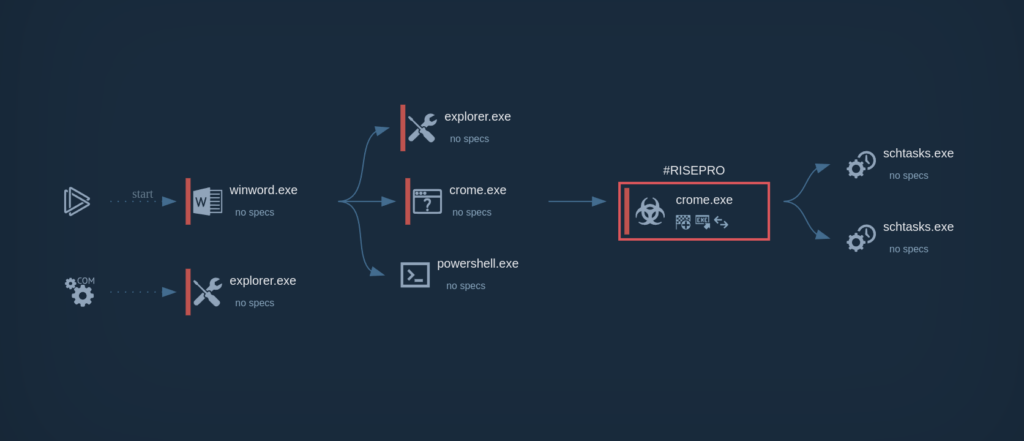
RisePro is a rising infostealer designed to grab credit cards, passwords, and crypto wallets from infected devices.
Vertrieb: RisePro is embedded in cracked versions of popular software sold online, game modifiers, and key generators. RisePro has links to PrivateLoader, a malware distribution service, which uses its network of fake and malicious websites to distribute the malware.
7-Schritt-Infostealer-Infektionskette
Infostealers compromise an organization from the inside, delivered under the guise of legitimate software, before exfiltrating and encrypting sensitive data straight to the threat actor‘s server.
To protect your organization from infostealer malware, it‘s imperative to understand the full infection chain.
Lieferung
- Cybercriminals embed infostealer software into malicious files and attachments, tricking users into downloading and installing the malware onto their devices.
- Infostealers are hidden within phishing emails, malvertising campaigns, scam sites, fake browser updates, cracked software, fake installers, or a loader that drops the stealer.
- The goal is to make the infostealer malware appear legitimate to systems.
2. Ausführung
- Once the victim opens the malicious file, the infostealer malware performs anti-analysis checks to avoid sandboxes and virtual machines, then prepares modules for data theft.
- Infostealers operate within the memory of a device, completing their operation within seconds to avoid detection.
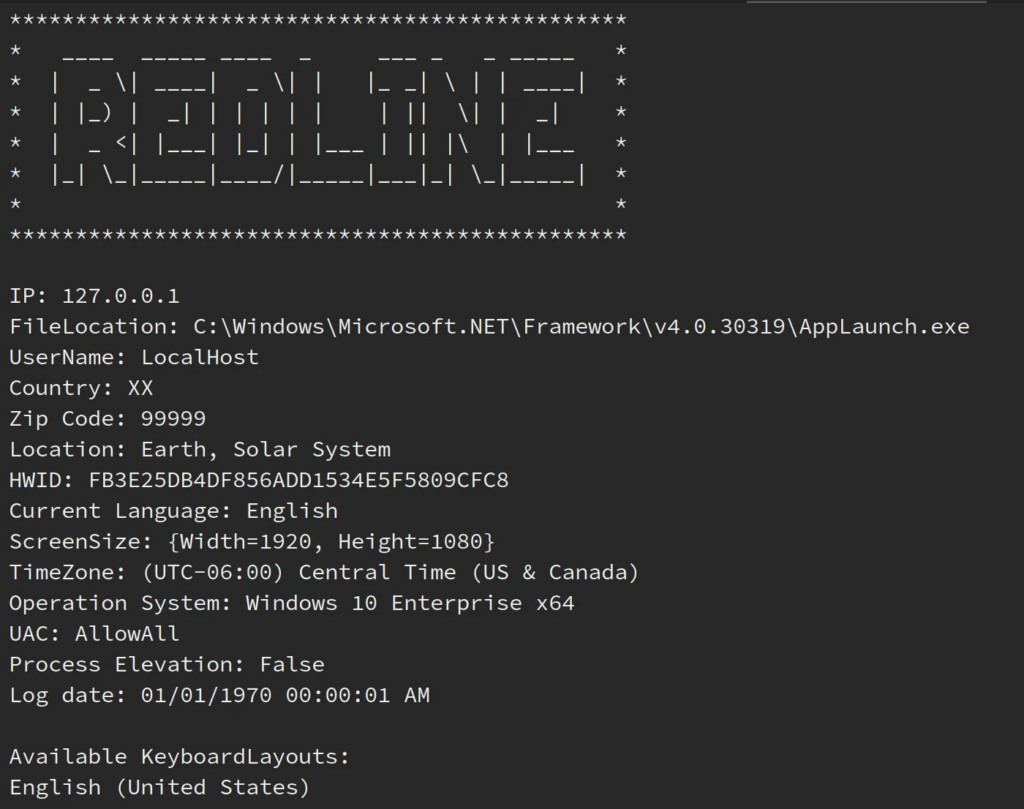
3. Aufklärung
- Before the infostealer starts taking sensitive data, the malware gathers information about the operating system (OS) to discern which data is available and valuable.
- Infostealers gather information on browser versions, OS details, system architecture, hardware details like CPU, GPU, and RAM specs, IP addresses, geolocation data, installed security tools, and system language.
4. Datenerfassung
- At this stage, the infostealer can begin harvesting sensitive data.
- Data commonly stolen includes saved browser credentials, FTP accounts, session cookies and tokens, autofill browser data, crypto wallet information, system fingerprints, VPN credentials, files, screenshots, and clipboard data.
5. Datenausleitung
- Once data is collected, the infostealer malware begins exfiltrating to the attacker‘s command and control (C2) server.
- Cybercriminals also exfiltrate data through Telegram bots, custom APIs, encrypted HTTP POST requests, and extensive botnet infrastructures.
- Many infostealers complete data exfiltration in under 3 seconds.
6. Aufräumen
- After the operation has been completed, infostealers delete themselves, remove temporary files, clear execution traces, and exit the system without persisting.
- Infostealer malware is stealthy, cleaning up after itself to reduce detection attempts.
7. Monetarisierung
- Cybercriminals use stolen data to resell on the dark web.
- In some cases, the stolen data is used to launch further attacks, such as social engineering and ransomware attacks.
- Data sold on the dark web helps attackers to perform account takeovers, business email compromise (BEC), gain control of cloud environments, network intrusions using VPN access, and ransomware staging with stolen credentials.
Tipps zur Vermeidung von Infostealern
To prevent unauthorized access of personal devices and work accounts, security teams have to remain vigilant against cyber threats.
Infostealer detection is difficult, but there are warning signs to look out for.
Nachweismethoden
- Monitor for unexpected access requests to browser credential stores.
- Check for outbound access to newly registered domains.
- Detonate suspicious files in sandbox environments to reveal suspicious behavior.
- Block unsigned executables from running.
- Monitor for suspicious hijacking patterns like token reuse from unknown devices.
- Scan the dark web for gestohlene Zugangsdaten before hackers can use them.
Verteidigungsmaßnahmen
- Block execution from Downloads, Temp, and User Profile paths.
- Keep OS and browsers fully patched to harden endpoints.
- Disable or restrict PowerShell, WScript, and macro execution where possible.
- Reduce malware credential harvesting by disabling or restricting web browser password storage.
- Verwenden Sie FIDO2 to avoid phishing attacks.
- Monitor the dark web in real-time for stolen credentials.
Wie sollten Incident-Response-Teams mit Infostealer-Kompromittierungen umgehen?
If you notice any tell-tale signs of an infostealer malware infection, follow these steps to ensure you contain the spread.
- Revoke access: Disable the user’s access to internal systems and networks, then terminate all active session tokens to prevent these from being used by the threat actor.
- Investigate: Log any unusual IPs, devices, suspicious login times, and unusual access to sensitive files. Check for large file transfers and copying of confidential data.
- Remove the malware: Cybersecurity teams should clean the user‘s infected device, including both business and personal devices.
- Reset passwords: Ask the user to reset their password and ensure all passwords are stored on a secure password manager. Additionally, enforce MFA if it is not already being used.
- Harden your ecosystem: Prevent unmanaged devices from being used at work, shorten the duration of session tokens, monitor the dark web for stolen credentials, and raise employee awareness on the dangers of infostealers.
Einpacken
Avoid being compromised by infostealers in 2026 by going beyond firewalls. Being compromised by infostealers can lead to Datenschutzverletzungen, unauthorized access to internal systems, business email compromise (BEC), supply chain attacks, and ransomware attacks.
Vulnerabilities like outdated APIs give threat actors a foothold in your organization‘s ecosystem, leading to potentially devastating data breaches caused by infostealers.
Detect compromised credentials and exposed data with CybelAngel’s continuous dark web and infostealer monitoring
Dealing with infostealer compromises can be a strain on resources and lead to potentially damaging financial losses.
CybelAngel‘s Dark Web Monitoring helps your security teams better defend against infostealers. Our in-depth threat intelligence reports help teams better assess your organization‘s risk and alert you when stolen credentials are circulating.
Interessiert an einer Demo? Siehe unser Lösung in Aktion mit einem fachkundigen Mitglied unseres Teams.

