CybelAngel’s 2024 State of EASM Report [Executive Summary]
Mini but mighty. If you’re a cybersecurity professional short on time, you’ll love our executive..
We are proud to protect a global network of hundreds of enterprise clients, providing them with advanced EASM protection for enhanced security
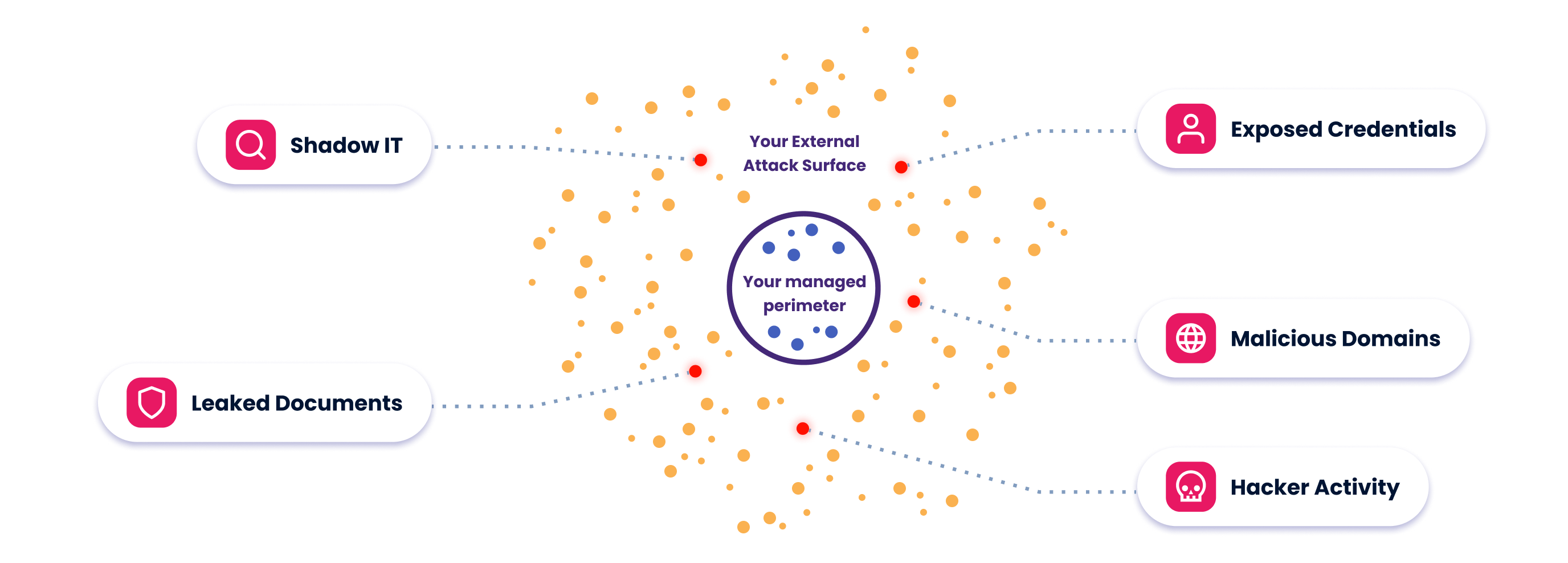
Real-time, comprehensive scan of the internet
ML models & dedicated analysts, combined
Fast remediation through takedown services, API integrations and pre-built connectors