Unmasking NoName057(16): Botnets, DDoSia, and NATO
Table of contents
NoName057(16) is one pro-Russian hacktivist group targeting NATO. Their attacks are not technically sophisticated, but they do cause real disruptions for Ukrainian allies and civilians.
To destabilize critical infrastructure, the group utilizes botnets to deploy DDoS attacks (distributed denial-of-service) to many EU countries and NATO allies. NoName05716‘s DDoS attacks have been compared to other pro-Russian hacktivist groups like KillNet—especially due to the volume of attacks launched.
Let‘s evaluate how NoName05716 is launching its attacks and what this means for businesses and governments around the world.
What is NoName057(16)?
NoName057(16) is a pro-Russian hacktivist group known for its cyberattacks on Western countries including financial institutions, government websites, and transportation services.
Since March 2022, the threat actor group has conducted over 1,500 DDoS attacks (distributed denial-of-service) on pro-NATO countries in an attempt on behalf of Russia to destabilize anti-Russian forces.
NoName in numbers…
NoName05716 has continued to ramp up their DDoS attacks since their conception in 2022. 3 years on, new data continues to come out about the success of their operations and who might be the next target.
Here are some key insights into the group‘s cyber attacks:
- They consistently launch successful attacks. The group has a 40% success rate according to Avast.
- Banks and transport companies are targets. To undermine critical infrastructure, the group has targeted the transportation and banking vertical sectors 25% of the time.
- 2023 saw intensified attacks against neighboring EU countries. The top 5 countries impacted in 2023 (Q1 – Q3) were Poland, Lithuania, Czech Republic, Italy and Spain.
- They‘re focused on bringing down Ukraine‘s support networks. Ukraine was only at position #6 in NoName057(16)’s list of victims for 2023.
What is the primary motivation behind NoName057(16)’s cyberattacks?
Fueled by pro-Russian nationalism, the hacktivist group is primarily motivated by political reasons. When Russia aggressed against Ukraine and invaded, the group became more motivated than ever to interrupt and stop support for Ukraine.
When the group released their manifesto, it highlighted their hostility towards NATO countries.
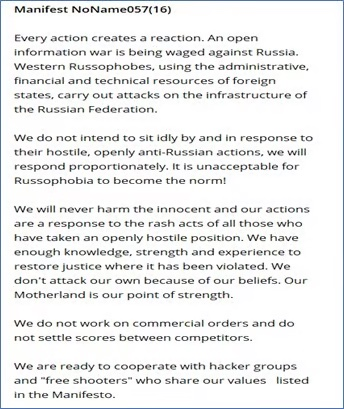
Since the start of the war, Russian cyberattacks on Ukraine surged by nearly 70% in 2024. Hacker groups like NoName057(16) and Killnet show how Russia has taken the war online, attacking supply chains and governments of Ukraine-sympathetic nations worldwide.
How do NoName operate?
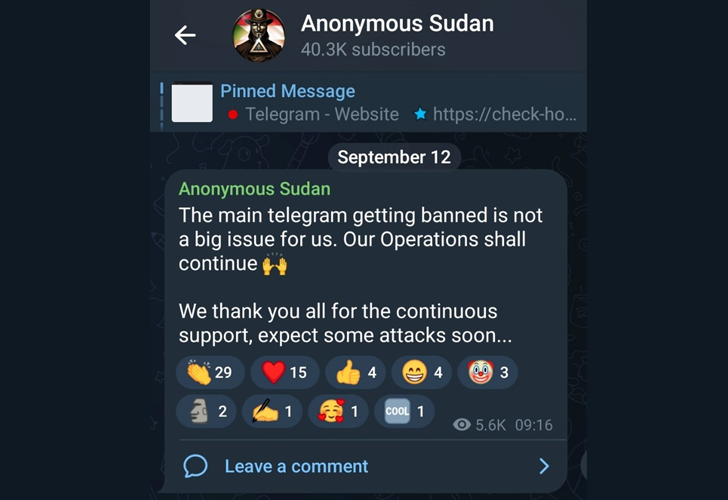
NoName057(16) operates using Telegram channels—Telegram is an open-source, encrypted telecommunications app, often used by cybercriminals to conceal their organization. The current NoName05716 Telegram channel has over 52,000 subscribers.
GitHub is used by the group to host their DDoS tool, website, and associated repositories—enabling them to share materials and techniques with their audience.
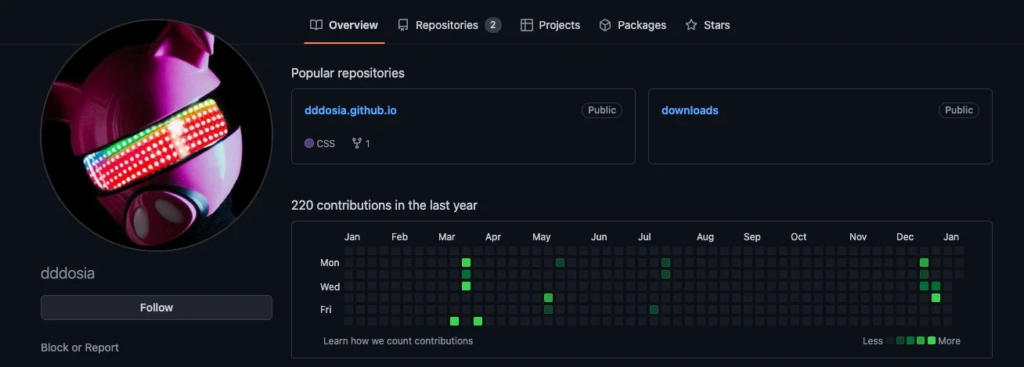
They have also developed a DDoS tool named DDoSia, allowing them to perform DDoS attacks to target sites repeatedly.
What are the most notable attacks attributed to NoName057(16)?
Since 2022, NoName057(16) has launched a series of cyberattacks across Western government websites including against Ukraine, Poland, Denmark, Lithuania, Estonia, Italy, the Czech Republic, and Canada.
Here are some of the known DDoS attacks attributed to Noname057(16):
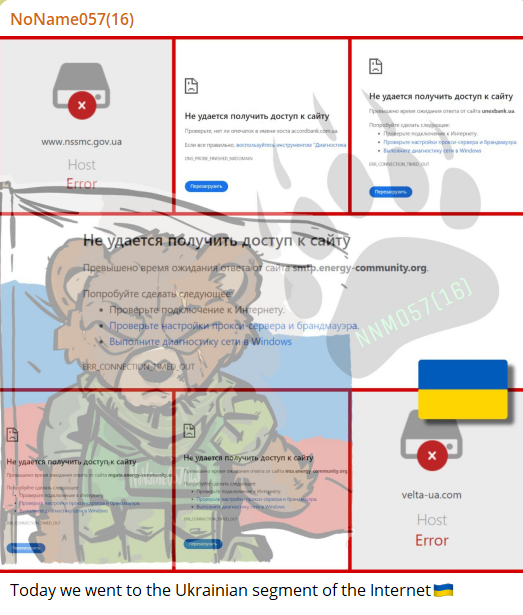
Ukrainian government attack
In June 2022, the group launched a DDoS attack on the Ukrainian government, utility, armament, transportation, and postal websites. The goal was to destabilize Ukraine during the ongoing war against Russia.
Shortly after, the group focused on disrupting Ukrainian news sources, launching attacks on multiple news servers. Their goal was to stop the spread of information that could be harmful to Russia‘s progress in the war.
Targeting the Baltic states: Lithuania, Estonia, and Latvia
In mid-June 2022, NoName05716 began to target neighboring Baltic states following a ban on the transit of goods subject to EU sanctions. The group targeted transportation companies, and local railway, and bus transportation companies to disrupt their supply chains.
The group also targeted Lithuania‘s largest bank, SEB in July 2022.
Danish financial sector attack
In June 2022, NoName057(16) targeted multiple Danish banks, causing operational delays. Among the banks targeted were the largest in the country in a bid not just to disrupt but also to collect data.
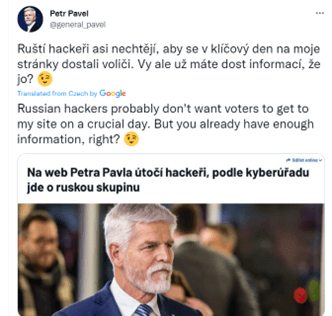
Attack on Czech presidential election
In January 2023, the group began to target the websites of Czech presidential candidates. Among the websites affected was a nonprofit organization that presented the election programs of all candidates. The goal of the attack was to disrupt the presidential election process, especially against candidates that were not “Pro-Russia”.
Government websites affected included the Watchman of the State organization website, the Czech Statistical Office, and the Ministry of Foreign Affairs.
Attack against Poland
In December 2022, the hackers created websites impersonating the Polish government. The phishing website duped users into collecting payment information under the guise of a verification fee. The aim was to undermine the state and collect information to extort money.
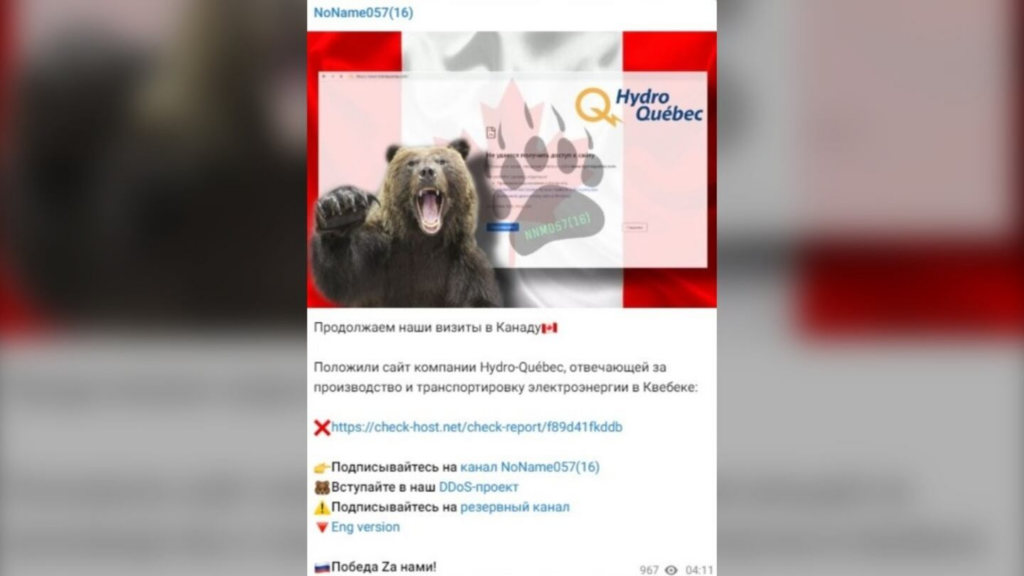
Canadian government websites attack
In September 2023, the NoName057(16) group launched a DDoS attack on many Canadian and Quebec government websites. The group took responsibility for taking down the websites of the ports of Montreal, Quebec City, Halifax, the Laurentian Bank of Canada, and the TD Bank.
A breakdown of the different industries that NoName05716 targets is shown below. Governments are the biggest target, making up 54% of their attacks. The secondary targets, the Banking and Transportation industries, are chosen by the hackers to disrupt resource supply.
How do NoName05716 attacks work?
NoName05716 relies on multiple tools to conduct their attacks.
DDoS attacks (distributed denial of service) are conducted using a self-made multi-threaded application, the so-called DDoSia project. The attack toolkit is used to overwhelm networks with packets, so the site is unable to function normally.
DDoSia was initially written in Python using CPU threads to launch attacks and requests at the same time. The current version of DDoSia now relies on HTTP protocol for Command & Control (C2) communication, with JSON configurations distributed by the C2 server, and is available on Linux, Windows, and MacOS, making it easy for any of their worldwide volunteers to participate.
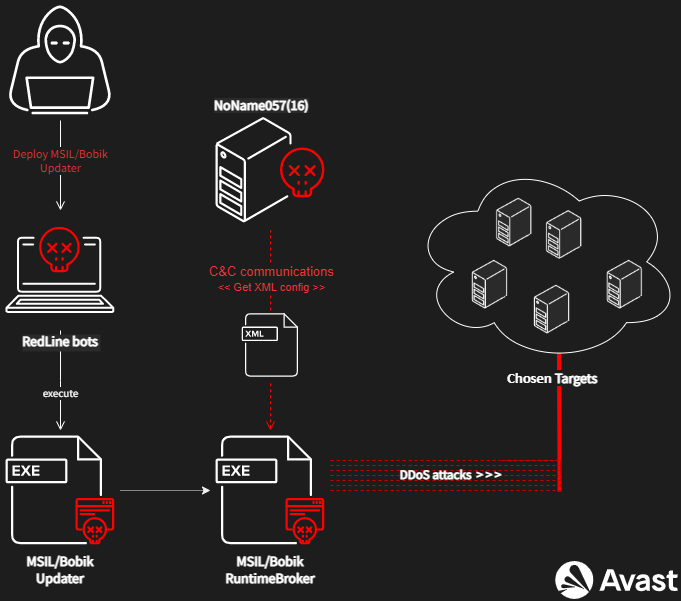
To carry out large-scale DDoS attacks, NoName05716 infects servers with malware called Bobik—adding them to a botnet to carry out future DDoS attacks for the group.
The stages of the attack are divided into two basic stages.
- The first is to spread the Bobik bot via the RedLine Stealer bot.
- In the second stage, Bobik’s Updater extracts and drops the final DDoS module to ensure DDoS attacks continue.
NoName057(16) is making efforts to make its malware compatible with more operating systems to increase usability and accessibility. In the future, it‘s expected that they will continue to make their applications and systems stronger.
Who does NoName057(16) target?
The pro-Russian hacker group targets and attacks Ukraine and NATO countries, including the Eastern neighboring countries (Lithuania, Poland, Czech Republic, and Latvia). Countries that vocalize their support of Ukraine over Russia quickly become targets for the hacktivist group—especially if the country is providing military support.
Western countries, on the other hand, are a secondary target for NoName05716. Countries including France, the United Kingdom, Italy, Canada, and other EU countries have bolstered support for Ukraine, making them in turn a target for pro-Russia hacktivist groups.
What are the recent activities of the hacking group NoName057(16)?
At the beginning of 2025, NoName05716 turned its attention to Italy. They attacked the websites of Italian ministries and critical infrastructure during Ukrainian President Volodymyr Zelensky’s visit to Rome. Comments made by the Prime Minister voicing support for Ukraine and condemning Russia have intensified the attacks against the country.
The hackers targeted around 20 websites, including Italy’s Guardia di Finanza, the Carabinieri, and multiple government ministries—Industry and Made in Italy, Foreign Affairs, Economy, Infrastructure and Transport, and Economic Development.
Defending against NoName057(16)
DDoS attacks are some of the most regularly occurring cyberattacks, reaching record highs in 2023, and are expected to increase in 2025. It‘s more important than ever to ensure that IT infrastructure is fortified to handle large-scale cyber threats from foreign malicious actors.
Here are some ways to bolster security against Russian state-sponsored and criminal cyber threats according to CISA:
- Limit traffic to your website. Firewalls are a useful tool to strategically restrict internet traffic and detect abnormal patterns to stay secure.
- Implement captcha systems in public forms without authentication. Captcha systems make it more difficult for bots to perform a DDoS attack.
- Evaluate security settings. Restrict access to crucial platforms and sites to minimize incidents of credential harvesting.
- Use a VPN to conceal IP addresses. Using a VPN to obscure your IP address makes it harder for an attacker to locate your network, which makes it harder for hackers to target your business.
- Restrict the number of connections per IP address. This makes it less likely that an attacker will find a way into the network through a known IP address.
- Create a disaster recovery plan. Plan for the worst-case scenario and educate internal teams to ensure that if an attack does occur, it can be dealt with swiftly.
- Invest in DDoS mitigation services. Leveraging professional DDoS mitigation services, like CybelAngel, can help internal cybersecurity teams monitor web traffic and apply necessary filtering techniques to thwart attacks.
Fight ransomware with CybelAngel
Hacktivist groups like NoName057(16) work in nimble structures, making their attacks more prolific and far-reaching. Given the tumultuous state of foreign affairs in 2025, it‘s now more important than ever to ensure your organization is up-to-date with the latest cybersecurity measures.
CybelAngel provides a full 360 view of cyber threats, ensuring that your team can take action before attacks occur. Find out more by getting in touch.

