6 Immediate Questions to ask After a Vendor Data Breach
Table of contents
In this guide to vendor data breaches we break down 4 core ways you need to shape your incident response including what questions to ask after a vendor data breach, 5 ways to understand its true cybersecurity scope, legal liabilities as well as communication and encryption tips.
A Vendor Data Breach Overview
If you are a cybersecurity professional, being prepared for a vendor data breach is an essential muscle to train.
In 2023, the average cost of a data breach globally reached $4.45 million (USD) representing a notable 15% increase compared to the past three years. This trend highlights the growing financial impact that organizations face due to data breaches.
In this guide, we’ll dive into the many vulnerabilities you’ll need to ask your vendor to asses with you so you can react with the best incident response plan.
In the aftermath of a vendor data breach, your first question or that any security team will assess “Who is responsible for this breach?”
After this it is a larger combined effort to access all of the vulnerabilities that have fallen like a domino stack.
It can happen that both both parties may be subject to liability after a data breach. This liability is based on a number of factors, including the agreement between both parties as to how sensitive data was managed.
After this there are a myriad of questions to ask that pertain to personal data, financial data, incident response and your attack surface to name a few.
Let’s examine the top questions to ask after your vendor data breach.
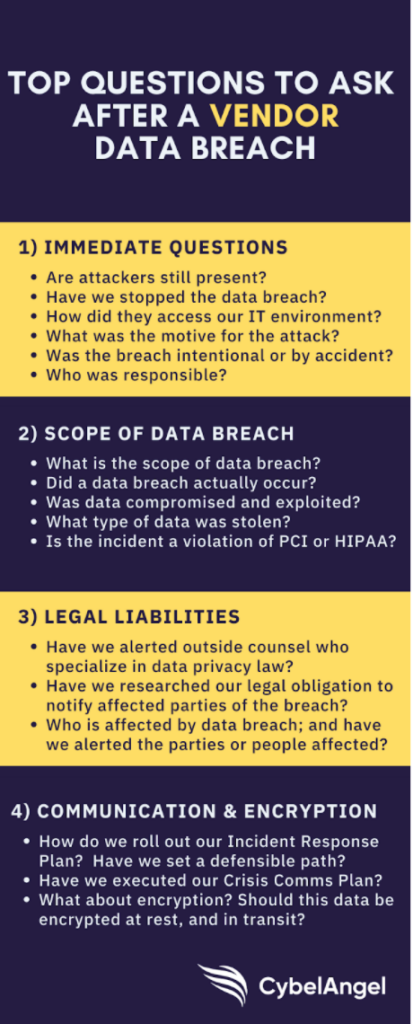
In the infographic to the right, see the top questions to ask your security team to assess after any vendor data breach. To be as thorough as possible best, run through these questions from top to bottom.
1: 6 data security questions to ask after a vendor data breach
Your security team face multiple pressing issues after a data breach and it can be difficult to choose an immediate course of action.
The most pressing question is to understand and grade your cyberattack threat. After this you need to run through the following list of data security questions. These will help you quickly define what kind of cybersecurity threat are you facing and the potential damage it poses to your organization.
Here are 6 data security questions you need to ask after a vendor data breach:
- Are cyberattackers still present?
- Has the data breach been stopped after the alert?
- How did these hackers access your IT firewalls?
- Is there a motive for the attack e.g. ransomware?
- Was this cybersecurity campaign intentional or was it caused by negligence like human error through a phishing campaign?
- What is responsible e.g. is it a malware vulnerability?
After you size up your threat, you then need to define the scope of the data breach to move forward and remediate.
2: Understand the true scope of data breach vulnerabilities
Sometimes there is a data leak, but it’s not yet a whole scale data breach. This means that for now that no cyberattackers have exploited your data; although it is freely available on the web. In this case, the priority is remediating the leak by securing your data from hackers. Ask these questions to determine the scope of the data leak:
- What is the scope of data leak?
- Did a data breach actually occur?
- What type of data was stolen?
- Was sensitive data compromised and exploited?
- Is the incident a violation of a data privacy regulation such as GDPR, HIPAA, CCPA, et al?
Once you’ve identified that an actual breach has taken place, you and your security team need to determine which data was stolen and how it is being used.
The type of data stolen will inform the scope of the data breach. Is it in violation of standards set for GDPR (General Data Protection Regulation), PCI (Payment Card Industry) or HIPAA (Healthcare Insurance Portability and Accountability Act), et al.
3: Address legal liabilities when sensitive information is leaked
After you know the scope and type of your data breach, you must ascertain your potential legal liabilities, including fines, lawsuits, and other costs that may arise from the data breach. Ask these questions:
- Have we alerted outside counsel who specialize in data privacy law?
- Have we researched our legal obligation to notify affected parties of the breach?
- Who is affected by this data breach; and have we alerted the parties or people affected?
Some companies have cybersecurity insurance to protect against data breaches. With data breaches on the rise, it’s no surprise that CISOs and CFOs now have the painful job to forecast lost equity and costs from future data breaches.
4: Review all cybersecurity communication and encryption
You will want to make sure your company has a defensible path to prevent future data breaches. From that plan and your Incident Response Plan, your Crisis Communications Plan can be updated and executed. Ask these questions:
- How do we roll out our Incident Response Plan? Have we set a defensible path?
- Have we executed our Crisis Communications Plan?
- What about encryption? Should this data that was breached be encrypted at rest and in transit?
Encryption plays a critical role to prevent data breaches.
Consider whether the type of data breached needs to be encrypted at rest — and in transit. Encrypting sensitive data can help to alleviate concerns among your vendors of similar data breaches in the future.
Proactive steps to take to prevent cybersecurity data breaches
The risk of a major data breach is significantly higher than in past years. Digital transformation initiatives and migrating to the cloud have jettisoned data far beyond the corporate security perimeter and placed it at great risk.
To secure data, take proactive steps and use an enterprise-grade platform to detect your data leaks anywhere they occur on the web, including your third-party vendor sites.
When you face the task of remediating and reporting data breaches, remember to ask the right questions. If your company is concerned about the security of its data on third-party sites, request a complimentary external exposure scan to find your data leaks.
You can use this dashboard to find what sensitive information is freely accessible through your vendor network.
Get ahead with a firm data breach prevention strategy
Before storing and exchanging data with third parties, ask questions of your vendors to determine the risk associated with their data management practices.
Choose vendors who have risk scores appropriate for the nature of your data.
Throughout the year, conduct regular checks by outside parties to audit data privacy and security. Global enterprises rely on CybelAngel, as an outside party to assess the data security of their strategic third parties.
Can I actually prevent a data breach?
To safeguard your organization from evolving cyber threats, it is crucial to embrace a long-term cybersecurity strategy.
Rather than a short-term, reactive approach, adopting proactive measures can yield significant benefits and is the smartest strategy moving forward in terms of cost benefits and results.
While there may be an initial impact on revenue-generating resources, investing in cyber risk management can have long-term payoffs. The Harvard Business Review citied a study of 5,882 U.S. hospitals that found that those that substantively adopted and deeply integrated IT security into processes and structures, rather than simply being symbolic adopters, could effectively reduce 37.8% of data breaches.
Prioritizing cybersecurity now will help protect your organization’s assets and reputation in the future. To stay ahead of hackers, use CybelAngel to prevent data breaches. Data leaks are inevitable; but damage is optional.