A Free Checklist to Avoid PII Leaks

Table of contents
Data breaches involving PII (Personally Identifiable Information) can result in severe consequences, including regulatory fines, damage to reputation, and financial losses.
To help you avoid PII leaks, here’s a comprehensive checklist based on recommendations from CISA, government agencies, and consultant groups.
But first, let’s look at some context…
Introduction to PII data breaches
PII includes personal data such as someone’s name, social security number, or financial information.
PII data breaches, or compromised credential leaks, are when where personally identifiable information (PII) is accessed without authorization. This can lead to identity theft, financial fraud, or other types of data privacy violations.
And the danger is ever-present.
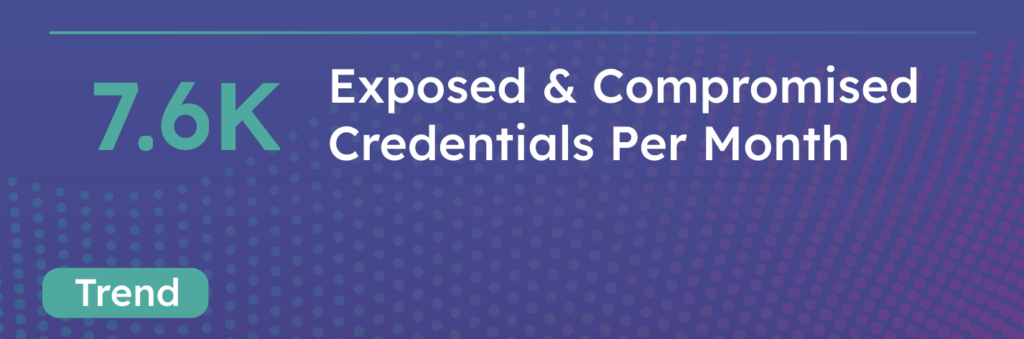
In 2023, CybelAngel found over 7,500 exposed credentials which were vulnerable to cybercriminals.
Is phishing responsible for PII data breaches?
Phishing attacks can be responsible for PII data breaches. However, they are just one of several potential breach mediums (see below).
What is responsible for most recent PII data breaches?
PII security breaches can happen for many reasons, including:
- Negligent handling and storage of sensitive data: For example, sensitive information could be sent to the wrong recipient, or digital devices left unattended.
- Malware and ransomware attacks: Malware (malicious software) can steal data through email attachments or software downloads. Ransomware involves encrypting the data until a ransom is paid.
- Social engineering tactics from hackers: For instance, phishing attacks can trick people into downloading malware or divulging personal data.
- Insider threats: Employees can often pose the biggest danger for PII data loss, because they can misuse their acesss permissions either deliberately or accidentally.
- Poor or outdated cybersecurity systems: Outdated software, unresolved vulnerabilities and weak encryption methods can increase the risk of a cyber incident.
- Lack of employee awareness and training: Many employees are unaware of the latest threats and cybersecurity best practices.
And the threat to personal data is higher than ever, with ransomware attacks increasing according to CybelAngel’s 2024 EASM report.
Who is ultimately responsible for PII?
In short—everyone!
Whether you’re a Chief Information Security Officer (CISO), a director, a third-party vendor, or an employee, it’s everyone’s responsibility to safeguard against PII privacy incidents.
Here’s a 8-step checklist to show you how.
PII data breach management checklist: 8 key steps
Here’s everything you need to know about data breach management and enjoy peace of mind about the PII data you process.
- Read up on privacy laws and regulations
- Limit the PII data you process
- Implement strong security measures
- Adopt a trustworthy cybersecurity tool
- Create an incident response plan
- Run regular risk assessments
- Invest in employee training and awareness programs
- Stay ahead of the latest cybersecurity trends
1. Get to know your jurisdiction’s privacy laws
Before you start your PII data protection strategy, it’s important to know which privacy laws are applicable to you.
Here are a few examples.
- GDPR (General Data Protection Regulation): A European Union regulation that mandates data protection and privacy for all individuals within the EU
- PCI DSS (Payment Card Industry Data Security Standard): A set of security standards designed for companies that process credit card information
- HIPAA (Health Insurance Portability and Accountability Act): A U.S. law for protecting sensitive patient data
Once you understand the legal and regulatory requirements in your area, you can confidently implement a PII risk management plan.
2. Don’t process more sensitive information than necessary
We’ll explore security solutions in a moment. But first, think about simplifying your databases.
The less data you process, the less you’ll appeal to cybercriminals. Collect and store just what you need for your operations—the rest should be deleted. This will already reduce your attack surface.
In its compliance checklist, the GDPR recommends running regular audits to review the information you process, and who can see it.
3. Make your security systems watertight
Protecting against cyber-attacks requires robust security measures, including:
- Safeguarding your network: Implement firewalls, data breach notification systems, and antivirus software
- Encrypting all sensitive data: Whether in transit or at rest, to prevent unauthorized access
- Implementing strong access controls: Use strong, unique passwords for all accounts, encourage the use of password managers, and enable multi-factor authentication (MFA)
- Setting up security policies and procedures: This will help you to proactively avoid data breaches

4. Choose a reliable cybersecurity tool
IBM recently reported that only a third of data breaches were detected by an organization’s own security team.
This highlights the importance of investing in trusted cybersecurity software to complement your own data breach management efforts.
For example, you could invest in an external attack surface management (EASM) tool like CybelAngel to:
- Keep an eye on your assets and identify any vulnerabilities
- Avoid data breaches before they happen
- Proactively prevent account takeovers
- Monitor the dark web
- Protect your domain
Plus, CybelAngel offers remediation, cyber due diligence, and special threat investigation to support your security efforts.

5. Prepare an incident management protocol
Establish a strong incident response plan that outlines the steps to be taken in case of a data breach.
CISA (America’s Cyber Defense Agency) has a series of recommendations for incident management, but here are some quick key steps to help you get started:
- Who’s in charge? Identify the key stakeholders and members of the incident response team. These people will be responsible for implementing the plan and leading the mitigation and recovery effort.
- Have we documented it? Create a comprehensive document that outlines roles, responsibilities, and communication procedures—including to affected individuals.
- Has it been tested? Test and review the incident response plan regularly, making any necessary adjustments as you go.
- Do we have the right contacts? Establish relationships with law enforcement agencies, legal counsel, and third-party service providers to assist in a data breach response.
6. Prioritize regular risk assessments
By systematically evaluating your systems, you can pinpoint weaknesses before they are exploited by hackers. Here’s how to prioritize risk assessments effectively:
- Conduct risk assessments: Regularly examine your entire IT infrastructure, including hardware, software, and network components.
- Update and patch software and systems: Regularly update and patch all applications and operating systems to fix known vulnerabilities.
- Perform mock data breach scenarios: Simulate various types of attacks to evaluate how well your team can detect, respond to, and mitigate a breach in real-time.
- Evaluate detection and response capabilities: Review your monitoring tools, alert systems, and the responsiveness of your IT team.
- Implement continuous improvement: Risk assessment should be an ongoing process. After each assessment, implement improvements based on the findings.
7. Provide training to all employees (and vendors, too)
Employee training is crucial for maintaining robust data security—and consider including your third-party vendors, as well, since 79% of data breaches were linked with providers.

Regular training sessions educate employees and partners about data privacy and security, keeping them informed about the latest threats and best practices.
Here’s how.
- Emphasize the importance of handling and protecting PII responsibly. When employees understand the value of the data they work with, they are more likely to follow protocols.
- Teach your employees how to recognize potential data security incidents. Provide clear examples of phishing attempts, social engineering tactics, and other common threats.
- Establish a straightforward process for breach reporting and incident escalation within the organization. This ensures that any potential threat is quickly identified and addressed.
- Foster a culture of security consciousness to defend against cyber threats.
In their ‘Shields Up: Guidance for Organizations’ document, CISA recommends also running regular exercises to make sure all team members understand their roles and responsibilities in the event of a data breach.
8. Follow cybersecurity trends
Staying ahead in the ever-evolving field of cybersecurity requires vigilance and continuous learning. Following the latest cybersecurity trends helps organizations anticipate threats and implement proactive measures.
Keep an eye on the latest press releases, white papers, and data breach investigations, as this will inform your own PII security.
Here are some helpful resources to get started:
- CISA: This American government agency offers no-cost cybersecurity services and tools, including cyber hygiene services, advisors, and assessments
- GDPR: The GDPR offers a comprehensive checklist for anyone who is processing personal data, to ensure you stay compliant
- NIST: This US government agency offers cybersecurity frameworks to inform your own strategy
- National Cyber Security Centre: A UK government agency with updates, educational resources and services for cybersecurity
- Infosecurity Magazine: This online news site delivers the latest updates in the cybersecurity world
- The Hacker News: A website with insider news stories and tips on data breaches, cyber attacks, and more
- CybelAngel: This EASM tool offers a blog, industry resources, and webinars to help you better understand current trends
Conclusion
Preventing PII leaks requires a holistic approach that includes proactive security measures, a well-defined incident response plan, and comprehensive employee training.
By implementing the recommendations outlined in this checklist and adhering to best practices, organizations can significantly reduce the risk of a data breach and protect sensitive information.

